by Cody Dumont
June 20, 2016
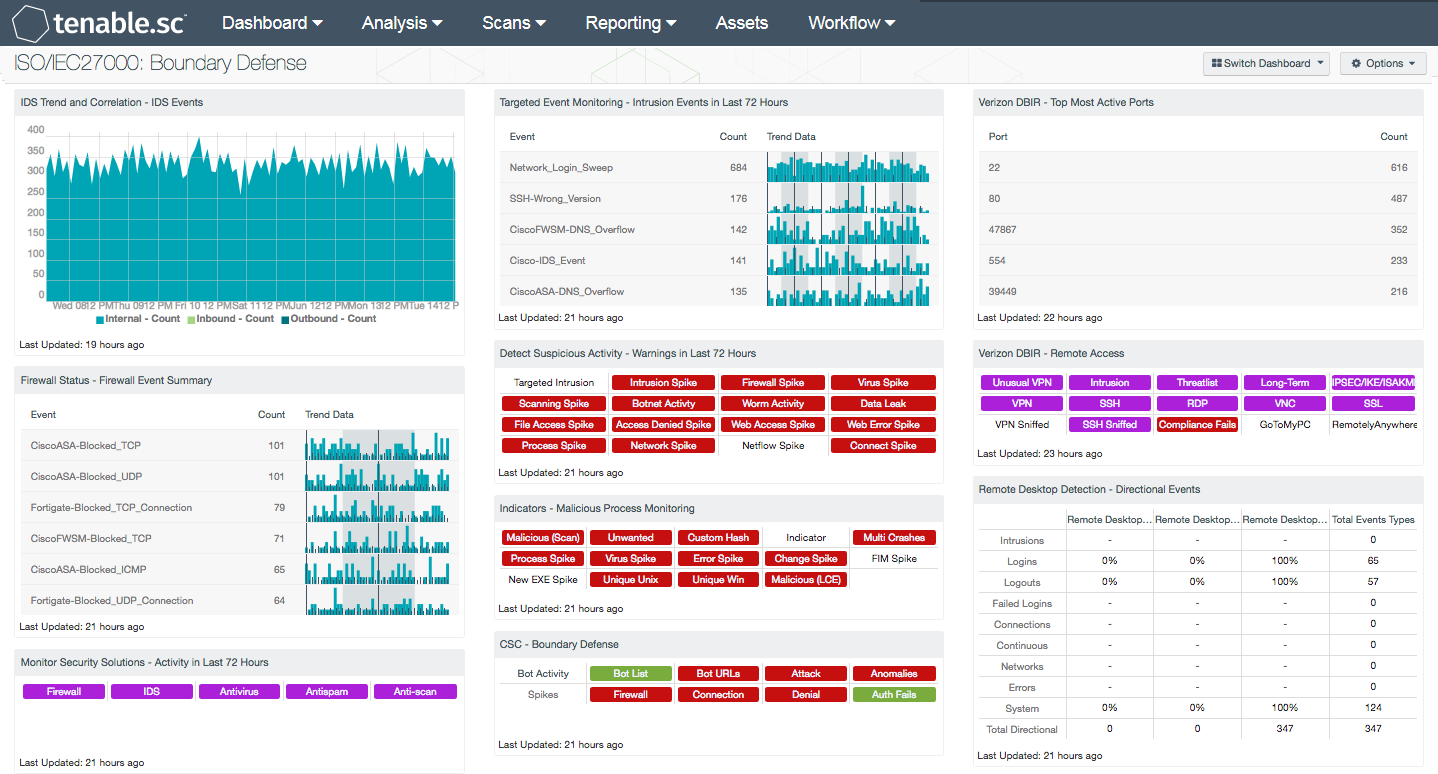
Firewalls and routers are normally the first layer of defense in protecting a network against threats, however without a multi-layered defense strategy, boundary devices can be easier to breach. Devices that are misconfigured or have weak security polices can leave critical systems exposed to attacks and network breaches. The ISO/IEC27000 Boundary Defense dashboard can assist the organization in detecting intrusion events, identifying suspicious activity, and monitoring remote access devices on a network.
The ISO/IEC 27002:2013 framework is a global security standard that provides best practice solutions in support of the controls found in Annex A of ISO/IEC 27001:2013. The framework establishes guidelines and general principles for initiating, implementing, maintaining, and improving information security management systems (ISMS). Each of the security controls and objectives provided within the standard can be tailored to specific business and regulatory objectives and assist with maintaining overall compliance. This dashboard focuses on the ISO/IEC 27002 13.1.1 and 13.1.3 controls that will assist organizations in ensuring that remote access is properly managed, network integrity is protected, and data leakage is controlled.
Organizations today are adopting mobile devices and cloud-based solutions to meet business needs. With additional devices such as IDS/IPS, Firewalls, and VPN’s coming online, organizations can easily lose track of critical events. To ensure complete network security, every potential entry point into a network must be monitored to protect from internal and external threats. Remote access using VPN, SSH, and Remote Desktop is no exception, as this can allow attackers to access internal resources. Tenable.sc Continuous View (CV) and Log Correlation Engine (LCE) are able to detect activity on boundary devices such as botnet activity, spoofing attempts, password guessing, and more.
This dashboard will assist organizations in monitoring the status of network boundary devices and remote access services. This will provide the organization with targeted information that the analyst can use to identify potential security policy gaps, prevent intrusions, and improve its overall defense-in-depth strategy.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.3.2
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.0
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring platform. Tenable.sc CV includes active vulnerability detection with Nessus and passive vulnerability detection with Tenable’s Nessus Network Monitor (NNM), as well as log correlation with Tenable’s Log Correlation Engine (LCE). Using Tenable.sc CV, the organization will obtain the most comprehensive and integrated view of its network devices and assets.
Components
IDS Trend and Correlation - IDS Events: This component displays inbound outbound and internal IDS events for the past seven days. This is useful to see if there have been any large spikes in attacks in either direction.
Firewall Status - Firewall Event Summary: This component displays the top 50 normalized firewall events by event count for firewalls from vendors such as Cisco, Juniper, Palo Alto, Fortinet, and many more. Each event will display the normalized event name, total event count, and trending data of this specific normalized event name. Using Tenable.sc CV for monitoring the different types of firewall events, a security analyst can determine if any malicious or suspicious firewall activity is occurring on the network.
Monitor Security Solutions - Activity in Last 72 Hours: This component assists in monitoring security solutions. The matrix presents activity indicators for various security solutions: Firewall, IDS, Antivirus, Antispam, and Anti-scanning. This component assumes that if log events were received in the last 72 hours from a particular technology, then that technology is active on the network, so the indicator is highlighted. Further investigation is warranted if a protection technology should be active, but no events are being received.
Targeted Event Monitoring - Intrusion Events in Last 72 Hours: The Intrusion Events in Last 72 Hours table displays the intrusion events by count detected in the last three days. Events are normalized by LCE and filtered on the event type “intrusion,” which denotes logs from network IDS, firewalls, applications, and operating systems that indicate some sort of network attack. This component alerts analysts to recent potential intrusion attempts to allow for remediation or reconfiguration.
Detect Suspicious Activity - Warnings in Last 72 Hours: This matrix presents warning indicators for potentially suspicious network activity detected in the last 72 hours. Each indicator is based on one or more Log Correlation Engine (LCE) events; the indicator is highlighted red if the event occurred in the last 72 hours. Any warnings should be further investigated. More information can be obtained on these events (such as details, time, and IP address) by clicking on the specific indicator in the dashboard component and viewing the raw syslog.
Indicators - Malicious Process Monitoring: This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs and continuous scanning activity and places them into one spot. This component is included in dashboards related to the 2015 Verizon Data Breach Investigation Report (DBIR).
CSC - Boundary Defense: This component displays information on a series of plugins that detect bot activity or spikes in connection, authentication failures, and denials.
Verizon DBIR - Top Most Active Ports: This table provides a list of the top 100 ports in use on the network. This table can be useful when monitoring network flows or establishing a baseline of traffic. Any new ports discovered should be investigated to determine their source and purpose. Any sudden change in count should be investigated as well. In the Verizon 2015 DBIR and the Mandiant M-Trends 2015 reports, common indicators of compromise were unauthorized FTP and other protocols. This component is included in dashboards related to the 2015 Verizon Data Breach Investigation Report (DBIR).
Verizon 2015 DBIR - Remote Access: The Verizon DBIR notes that it is important to restrict remote access to systems. This matrix assists the organization in monitoring its remote access. The Unusual VPN indicator is highlighted purple when a VPN login originates from an IP address that is not normal for the user ID. Multiple indicators highlight VPN, SSH, RDP, VNC, and SSL traffic events within the last 72 hours, including potential intrusion events, events associated with known bad IP addresses (threatlist), and long-term events. The VPN Sniffed and SSH Sniffed indicators are highlighted purple if those protocols, respectively, are passively detected on the network. The Compliance Fails indicator is highlighted red if there are any remote access compliance failures. The GoToMyPC and RemotelyAnywhere indicators are highlighted purple if those applications are detected on the network. Clicking on a highlighted indicator will bring up the analysis screen to display details on the detections and events and allow further investigation.
Remote Desktop Detection - Directional Events: Understanding the normal network traffic flow and the direction of Remote Desktop (RDP) communications allows for anomaly analysis and increases the likelihood of breach detection. This component provides a table of RDP network traffic directional flow by nine event types. The event types used are: Intrusion, Login, Logout, Failed Login, Connection, Continuous, Networks, Errors, and System. Tenable.sc Continuous View defines network traffic flow as internal, inbound and outbound. The Total Event Types column displays a count of all of the respective events, while the remaining three columns show the percentage of events according to directional flow.