by Cody Dumont
July 22, 2016
Security analysts often spend large amounts of time reviewing logs from systems attempting to locate the proverbial needle in a haystack. With the sheer volume of logs, Tenable’s Log Correlation Engine (LCE) provides several methods of focusing on the analysis process, beginning with which systems are sending logs, grouping logs by event type, and also by normalizing logs. LCE supports collecting logs from several sources, with the ability to collect and process common syslog messages and data from specialized agents. The data LCE analyzes is extensive and can assist in the detection of malware, unauthorized activities, and changes to information systems. This dashboard facilitates the initial log analysis and provides a starting point for practitioners to use in the hunt for compromised systems.
Organizations that choose to deploy the Log Correlation Engine Clients on workstations, servers, and other network infrastructure enable hosts to play an active role in the risk mitigation program. By implementing LCE clients on Windows workstations, CentOS, Red Hat, Fedora, FreeBSD, SUSE, Ubuntu, Mac OS X, and several other platforms, LCE is able to monitor closely to host based events such as running processes, file integrity events, network connections, and various application events. By allowing LCE to analyze host activity, the organization is provided with content for user activities and changes to systems, which may result in vulnerabilities, malicious activity and anomalous behavior.
LCE also supports other event collection agents such as the NetFlow Monitor and the Network Monitor. These agents allow LCE to look at traffic patterns at the packet level and based on flows. LCE uses different threat detection feeds to create normalized events when suspicious activities are discovered. LCE also supports special correlated events that can aid in the timeline analysis. The LCE Web Query Client uses web based APIs to extract cloud-based logs or other specialized events collection (such as RDEE and Splunk). When consuming logs from all aspects of the network, SecurityCenter Continuous View (CV) combines the events in event-based vulnerabilities, providing host detection and a deeper view into the security posture of an organization.
LCE supports over 35 different event types and over 10,000 normalized events, facilitating a very complete and robust threat detection system. When fully integrating SecurityCenter CV with the Passive Vulnerability Scanner (PVS) and Nessus, the organization can obtain a comprehensive view of the threat vectors to which their systems are exposed. When LCE or PVS detect malicious activity or when new systems come online, alerts can be configured to send email and launch scans. With the ability to collect information on running processes and detecting when a “Never Before Seen” event occurs, SecurityCenter CV can provide valuable information at the time the system is compromised.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring. The dashboard requirements are:
- SecurityCenter 4.8.2
- LCE 4.8.0
- Log Correlation Engine Clients
SecurityCenter CV allows for the most comprehensive and integrated view of network health by supporting a tight integration and API extensibility with SIEMs, malware defenses, patch management tools, BYOD, firewalls, and virtualization systems. Tenable’s Log Correlation Engine (LCE) supports future integration with log management tools, and malware defenses. Tenable’s Passive Vulnerability Scanner (PVS) supports network sensors, NetFlow, BYOD, firewalls, web, and authentication systems. By automatically discovering of users, infrastructure, and vulnerabilities across more technologies than any other vendor, SecurityCenter CV enables the organization to react to advanced threats, zero-day vulnerabilities and new forms of regulatory compliance.
Components
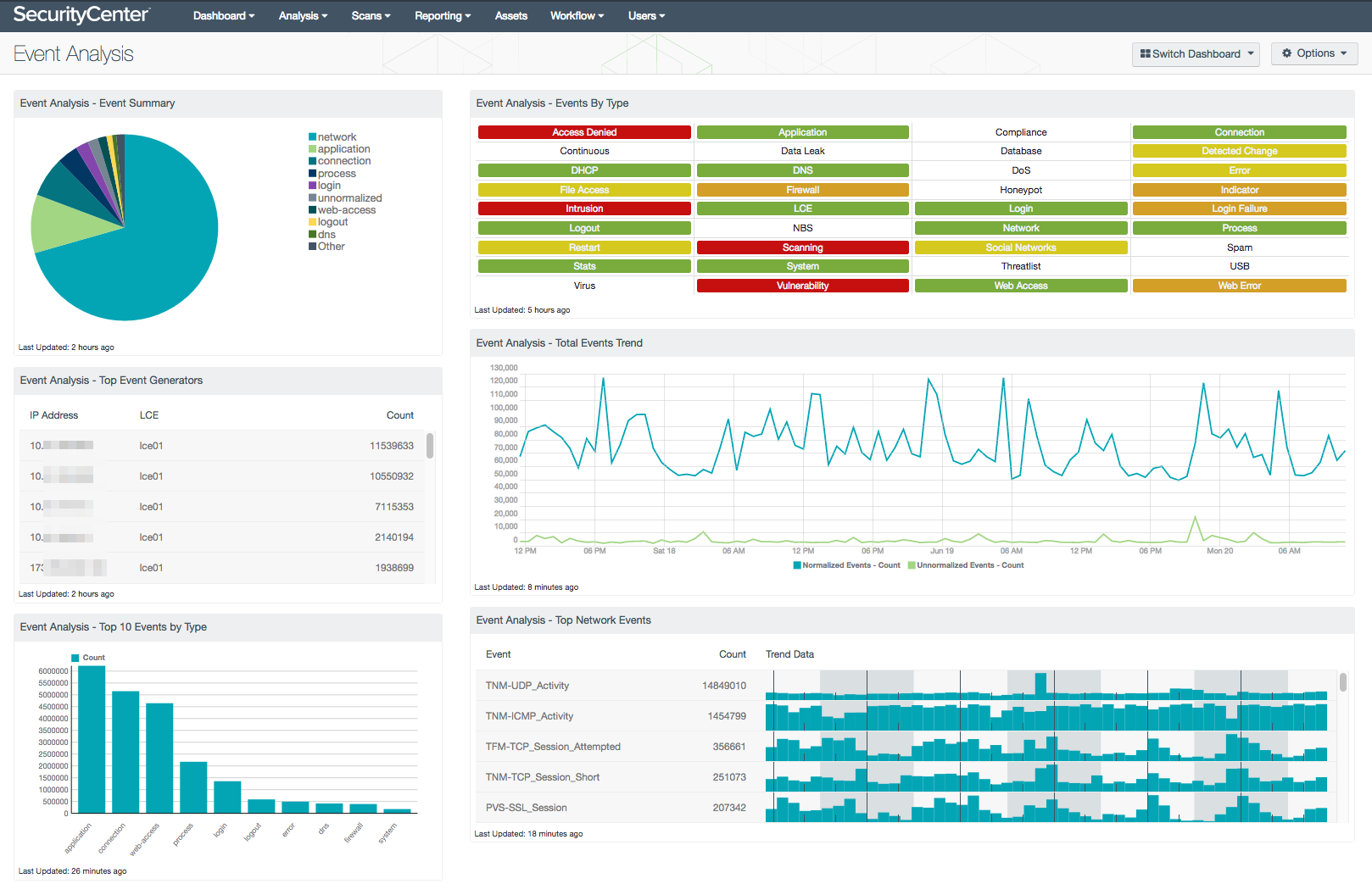
Event Analysis - Event Summary: This chart provides a visual summary of the network event types most collected by LCE. The events collected are sorted in descending order by count. When network collectors such as the Netflow Monitor or Network Monitor are used, the “network” type will often be most used. However, take care to not filter out the “network” type, as other types may then take over as the most used and obscure the visual results.
Event Analysis - Top Event Generators: This event summary component displays the top hosts generating events over the last 72 hours. For each host IP address, the LCE receiving the event and total event count is displayed. The hosts are displayed in descending order by event count. The primary benefit of this component is to identify the host from which the most events are collected, thereby identifying the systems with the most logged activity. Should something suspicious occur, this order might change from day to day.
Event Analysis - Top 10 Events by Type: This bar chart component displays information on event type summary top 10 details over the last 7 days. When performing analysis of large amounts of data, often the largest data samples needs to be removed to allow for other data to be properly viewed. In this case, the event type “network” is removed from the filter to ensure that all data can be seen more easily. Network events are usually have 5 to 8 times more events than other events. The filter in this chart uses the underscore “_” and dash “-“ to identify all normalized events, then the type “network” is removed. The chart provides visual details of event trends, sorted by count in descending order.
Event Analysis - Events By Type: This indicator provides a series of indicators for each event type, and is refreshed every 24 hours. This matrix allows the security administrator to receive information on current events. The color of the indicator reflects the severity: Low is green, Medium is yellow, high is Orange, and critical is Red. The different colors of the indicators signify the threat level of the event type. If no events are present, then the indicator is white. Events that are a normal event, but are more likely to have caution warranted, are green. For example, a 'detected-change' event can be a routine firewall change, or a prefetch file change on a Windows computer, both of which may not be an issue. By using a 'Caution' indicator, these events need to be monitored, but might be legitimate. The medium level, which is colored yellow, indicates some sort of a problem that should be investigated. For example, 'web-errors' may indicate a misconfigured server. The orange indicators are for a higher risk and should be addressed immediately. For example, as shown in the sample image, there is a 'Virus' event. These events should be investigated as soon as possible. Finally, the red color indicates a critical event and provides an indication of compromise or more serious event and should be investigated over all others.
Event Analysis - Total Events Trend: This line chart provides a comparison of normalized events versus unnormalized events. By comparing the normalized event detection from unnormalized detection, administrators can monitor for unnormalized events on the network. Tenable’s Technical Support can be contacted and raw logs can be submitted to Tenable development teams for normalization. When performing analysis of large amounts of data, often the largest data samples need to be removed to allow for other data to be properly viewed. Displayed is a line chart comparison over the last 72 hours of total normalized events versus unnormalized events. This provides the analyst with a quick overview of any current event spike activity.
Event Analysis - Top Network Events: This table provides a summary view of all normalized events part of the network event type. The Events Analysis dashboard removes the network event type from several components, due to the high quantity of events. This component breaks the events out by normalized event, allowing for the analysts to review the data.