by Megan Daudelin
April 1, 2016
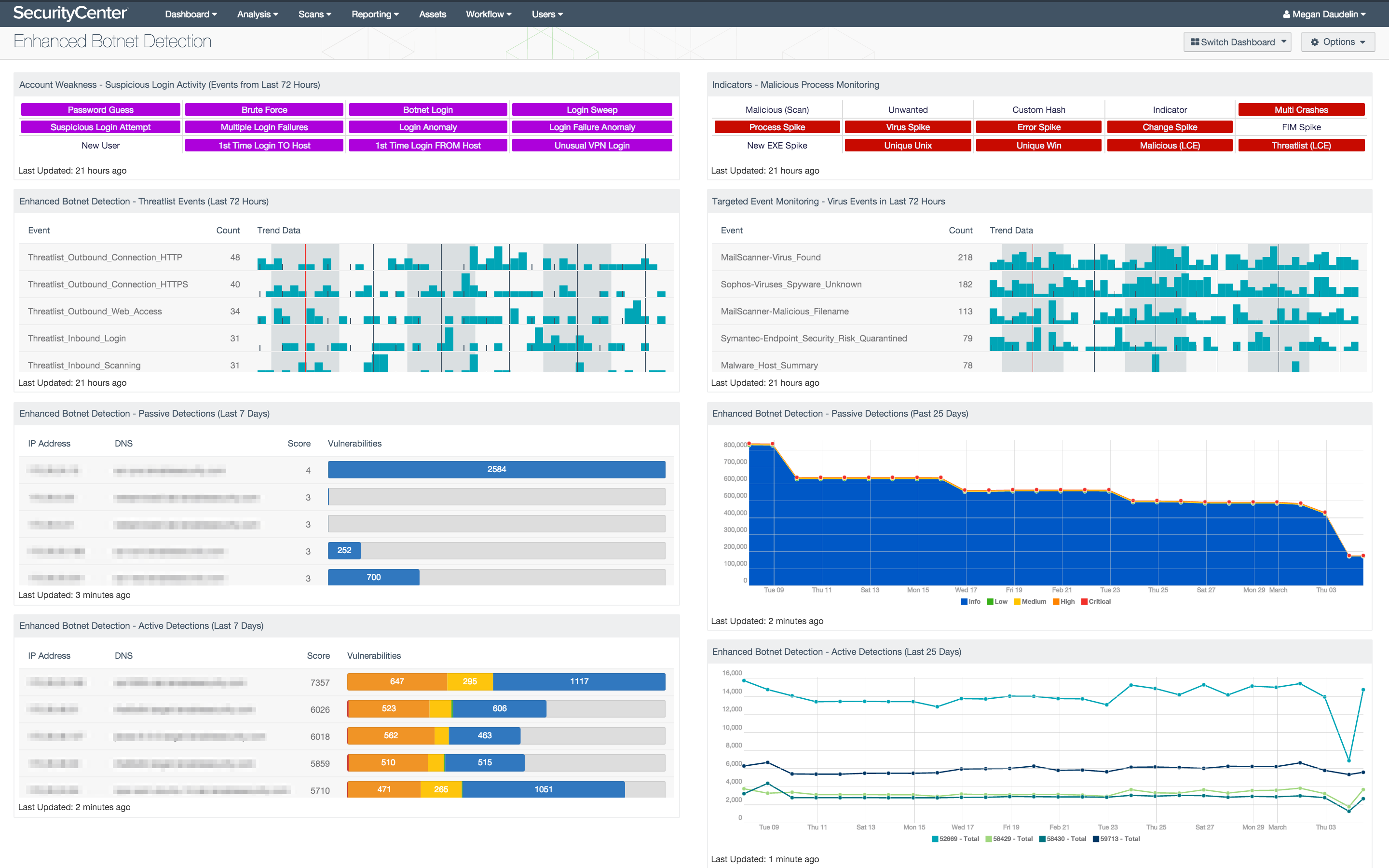
The Enhanced Botnet Detection dashboard assists security teams with monitoring the network for activity related to botnets. Specific events and plugins are used to identify potential botnet activity and the hosts involved. Detailed information about hosts with indicators of botnet activity is provided, along with trend data about botnet vulnerabilities over time. Event data is filtered to focus on threatlist and virus events, both possibly indicative of botnet activity. Indicator matrices alert on suspicious activity potentially related to botnet activity. By monitoring the network for botnet activity, security teams can more effectively ensure network integrity and security.
The components in the Enhanced Botnet Detection dashboard present events, hosts, and vulnerabilities that are possibly related to botnet activity. Matrices show indicators of potentially malicious or suspicious activity. Tables list events and hosts with detected activity related to botnets. Trend charts illustrate the presences of botnet-related vulnerabilities over time by severity and plugin. Each component can be modified to focus on subnets or systems of particular concern. Organizations can use the information provided to better monitor events and vulnerabilities potentially indicative of botnet activity.
This dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. This dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessment. The dashboard requirements are:
- SecurityCenter 5.2.0
- Nessus 6.5.4
- LCE 4.6.0
- PVS 4.4.0
- This dashboard requires “Full Text Search” to be enabled for each analyzed repository.
SecurityCenter Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. The Passive Vulnerability Scanner (PVS) performs deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. The Log Correlation Engine (LCE) performs deep log analysis and correlation to continuously discover and track systems, applications, cloud infrastructure, trust relationships, and vulnerabilities. By integrating with Nessus, PVS, and LCE, SecurityCenter CV’s continuous network monitoring is able to detect events and vulnerabilities across the enterprise.
The following components are included in this dashboard:
- Account Weakness - Suspicious Login Activity (Events from Last 72 Hours): This matrix shows potentially suspicious login activity, which can bring attention to accounts that are more threatened and require greater protection.
- Indicators - Malicious Process Monitoring: This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs and continuous scanning activity and places them into one spot.
- Enhanced Botnet Detection - Threatlist Events (Last 72 Hours): The Threatlist Events (Last 72 Hours) table provides a normalized event summary of the threatlist events detected in the past 72 hours by count.
- Targeted Event Monitoring - Virus Events in Last 72 Hours: The Virus Events in Last 72 Hours table lists the virus events by count detected in the last three days.
- Enhanced Botnet Detection - Passive Detections (Last 7 Days): The Passive Detections (Last 7 Days) table provides a list of hosts involved in botnet activity detected in the last seven days by score.
- Enhanced Botnet Detection - Passive Detections (Last 25 Days): The Passive Detections (Last 25 Days) area chart depicts the trend of vulnerabilities related to botnet activity over the past 25 days by severity.
- Enhanced Botnet Detection - Active Detections (Last 7 Days): The Active Detections (Last 7 Days) table provides a list of hosts with botnet-related vulnerabilities detected in the last seven days by score.
- Enhanced Botnet Detection - Active Detections (Last 25 Days): The Active Detections (Last 25 Days) line chart depicts the trend of vulnerabilities related to botnet activity over the past 25 days by plugin.