by Josef Weiss
August 12, 2014
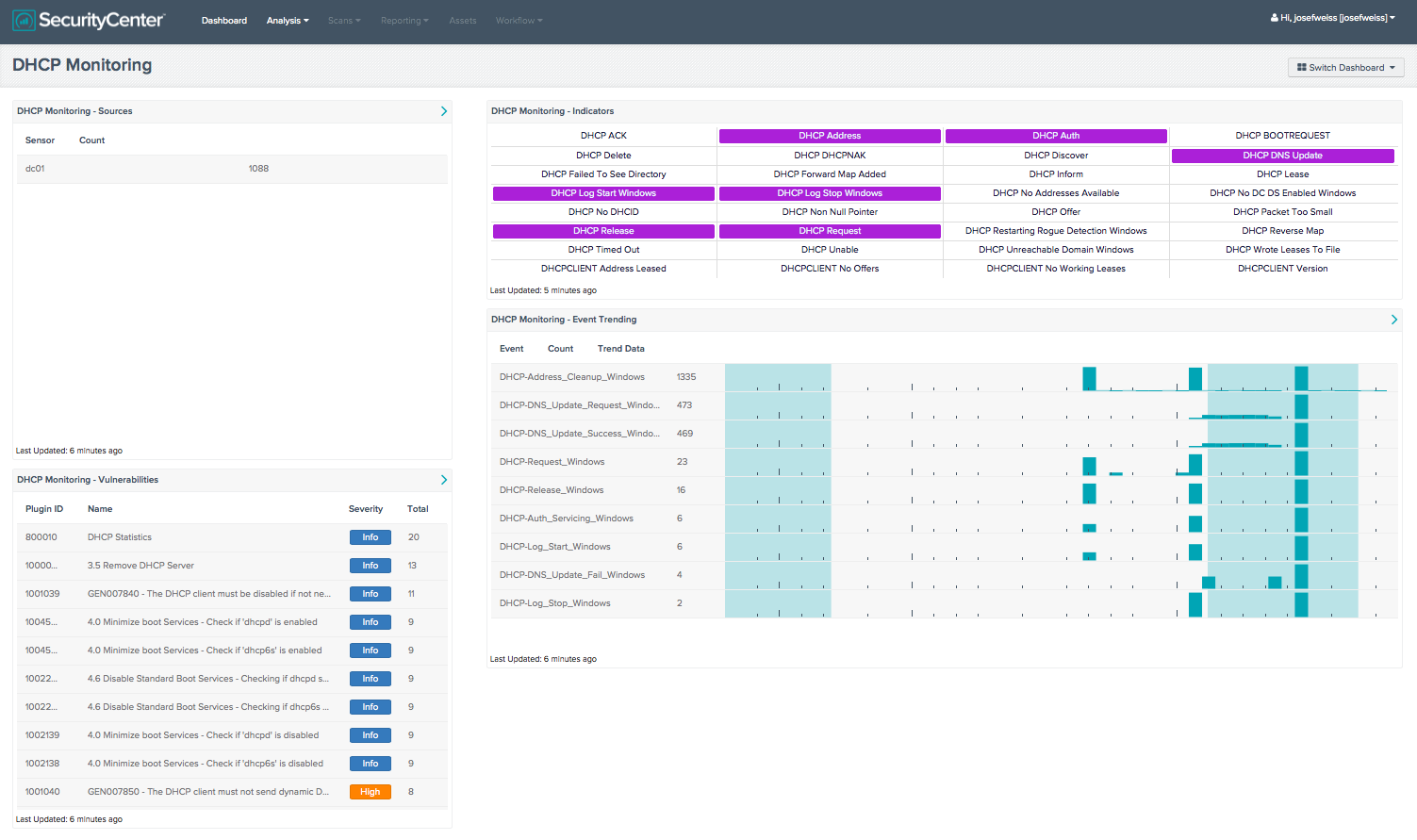
This dashboard provides a series of components that assist the analyst by providing indications for DHCP Sources, DHCP Vulnerabilities, and DHCP Events, and a series of indicators for over 30 DHCP-related events.
DHCP Servers are of critical importance to most organizations and monitoring their statistics can provide many benefits, such as outage detection and protocol failures. It is important to follow best practices for security when using DHCP servers on the network. This dashboard provides a series of components that assist the analyst by providing indications for DHCP Sources, DHCP Vulnerabilities, and DHCP Events, and a series of indicators for over 30 DHCP-related events. When combined with SecurityCenter CV, LCE, and PVS, DHCP protocols and logs can be easily monitored.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring.
The dashboard requirements are:
- SecurityCenter 4.8.1
- LCE 4.2.2
The DHCP Monitoring Collections contains the following components:
- DHCP Monitoring - Event Trending - This component trends DHCP events that have occurred within the environment over a 5 day period. The component utilizes the Normalized Event Summary tool and the ‘DHCP’ keyword to trend LCE normalized events over the specified time period. The table shows the top 50 events, with the event with the highest count displayed first in the table.
- DHCP Monitoring - Indicators - This component contains 32 indicators that trigger when various DHCP-related events occur. The events are DHCP-specific LCE normalized Events.
- DHCP Monitoring - Vulnerabilities - This component displays known DHCP vulnerabilities, sorted by the total number of reported vulnerabilities. The table displays the plugin ID, name, severity, and the total count of vulnerabilities found to exist.
- DHCP Monitoring - Sources - This component displays the sources that have been detected to have sent DHCP event data. Sources are presented by utilizing the Sensor Summary tool and the ‘DHCP’ string as a normalized event field.