by Stephanie Dunn
February 26, 2016
As organizations are reluctant to deploy file integrity monitoring solutions into their environment, many are forced to comply due to requirements within compliance standards such as PCI, HIPAA, and NIST 800-53. Monitoring any type of file change is crucial in identifying both routine and unauthorized file changes. This information can be used to determine who made the change, what file was changed, where the changes were made, and when. The File Integrity Monitoring dashboard can assist the organization by detecting file and directory integrity change events, monitoring File Integrity applications, and compliance checks.
The Cybersecurity Framework (CSF) provides guidance based on existing standards, guidelines, and practices that can be tailored to specific organizational needs. The Protect category is divided into multiple subcategories that address specific security requirements with Access Control, Awareness, Data Security, Policies and Procedures, Maintenance, and Technology Protection. The Data Security category (PR.DS) allows for information and records to be managed consistently and protects the confidentiality, integrity, and availability of organizational data. This dashboard focuses on the PR.DS-6 subcategory, which incorporates file integrity checking mechanisms that monitor event changes made within files and directories.
This dashboard uses “File” normalized events, which provides a list of events on file creations, modifications, deletions, and more. The Log Correlation Engine (LCE) processes events on file changes, which the analyst can use to obtain additional information on the file change made. When the change made, which host the change was made on, and by which user, can all be determined by the LCE. Compliance checks on file changes are performed, which can aid in maintaining overall compliance. In addition to monitoring for file integrity changes, deploying File Integrity Monitoring applications provides additional visibility and support when monitoring for file changes. Included are several File Integrity Monitoring applications, which will alert to any changes within the respective application. Any file changes among internal users will alert the analyst to potentially malicious activity, unauthorized access, or modification to files. The analyst should ensure that internal users have appropriate access privileges to prevent unintentional file access.
Any type of unexpected or unauthorized change can result in a loss of network services, data breaches, and fines and penalties due to non-compliance. Monitoring “file integrity change events” in real time enables the analyst to respond quickly, and can reduce any security gaps present on a network.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.2.0
- LCE 6.0.0
Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable.sc CV is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. By integrating with LCE, Tenable.sc CV provides the most comprehensive view of file changes on a network.
The following components are included in this dashboard:
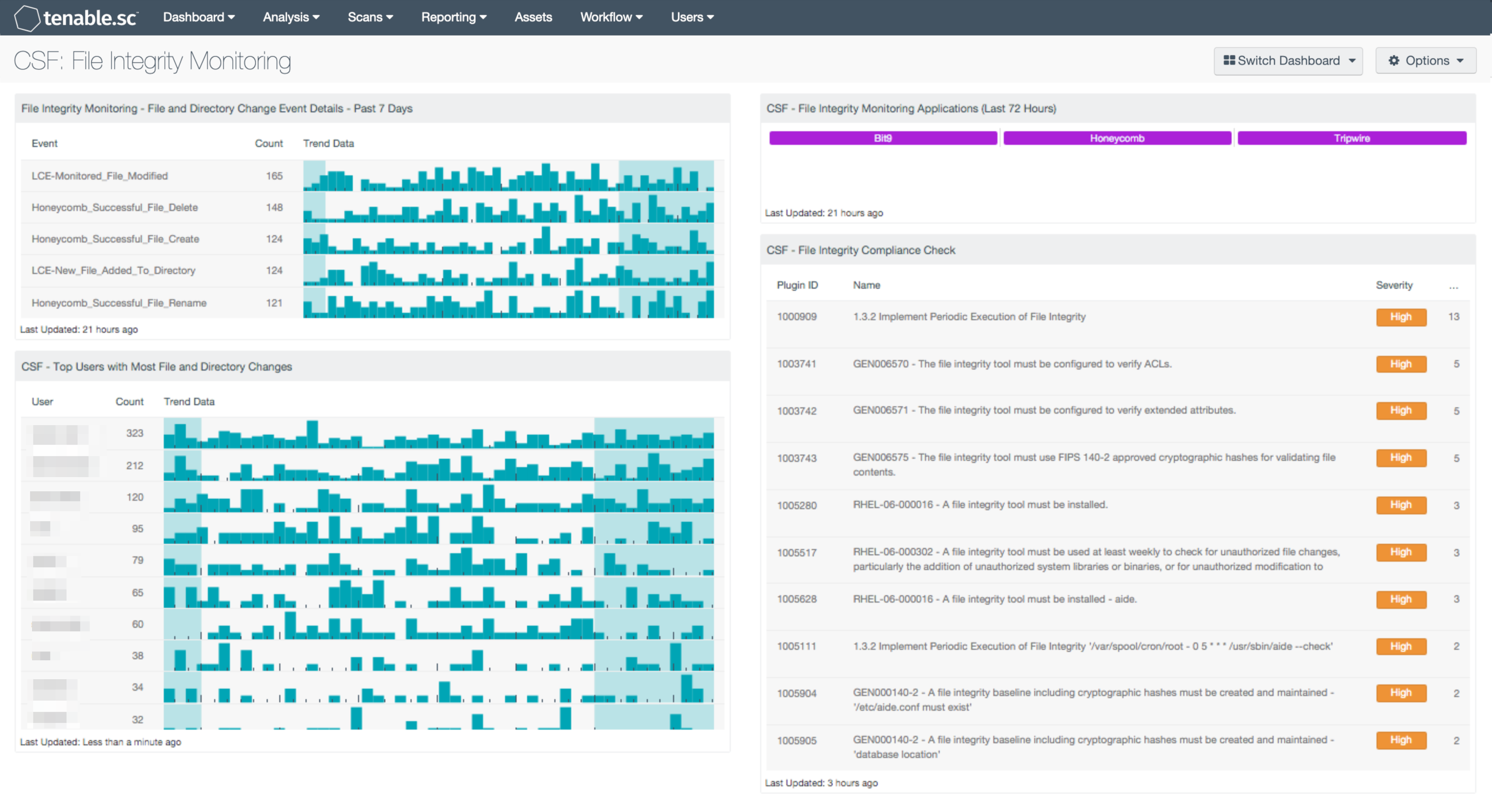
- File Integrity Monitoring - File and Directory Change Event Details - Past 7 Days: This table lists the events related to file changes detected in the past 7 days by count. This table uses the Normalized Event Summary tool and filters based on the keyword “File” and the “detected-change” type. The data in this table can be useful in determining the most common file change events and where they originate.
- CSF - Top Users with Most File and Directory Changes: The Top Users with Most File and Directory Changes table lists the top users with the most file changes detected in the past 7 days by count. This table uses the Normalized Event Summary tool and filters based on the keyword “File” and the “detected-change” type. This table can be modified to fit organizational requirements. The data in this table can be useful in determining the top users with the most file changes events and where they originate.
- CSF - File Integrity Monitoring Applications (Last 72 Hours): The File Integrity Monitoring Applications component presents a list of events from three File Integrity Monitoring applications within the last 72 hours. The matrix includes normalized events for each respective application. When an event has been detected, the indicator will turn purple. The analyst can click on the indicator to view the event list, and obtain information on Normalized Event, IP Address, User, and more. Each application can be modified or tailored to fit organizational requirements. Tenable can also create customized events types for specific File Integrity Monitoring Applications and events that are not covered.
- CSF - File Integrity Compliance Check: The File Integrity Compliance Check table presents a list of File Integrity compliance checks on a network. Many organizations are required to follow compliance regulations such as PCI DSS and HIPAA, which require file integrity monitoring as a part of compliance objectives. This table uses the “File Integrity” plugin name and “Compliance” plugin type to perform file integrity compliance checks. Data within this table is sorted by the highest total of hosts at the top, and includes the Plugin ID, Plugin Name, and Severity level. The analyst can drill down to obtain IP addresses, possible solutions, and additional information to aid with compliance.