by David Schwalenberg
March 29, 2016
The North American Electric Reliability Corporation (NERC) is a not-for-profit international regulatory authority whose mission is to assure the reliability of the bulk power system in North America. NERC Reliability Standards define the reliability requirements for planning and operating the North American bulk power system, which serves more than 334 million people. NERC is committed to protecting the bulk power system against cyber security compromises that could lead to misoperation or instability. The NERC Critical Infrastructure Protection (CIP) Standards provide a cyber security framework for the identification and protection of Bulk Electric System (BES) Cyber Systems, to support the reliable operation of the North American bulk power system.
One aspect of CIP-004 R4 (Access Management Program) involves implementing an electronic access management program, to authorize and review user electronic access based on need. CIP-004 R5 (Access Revocation) involves revoking user access in cases of terminations or transfers. CIP-007 R5 (System Access Control) involves enforcing user access control and securing user authentication. These requirements mirror important cyber security best practices dealing with user access and least privilege. User access must be limited in order to limit inadvertent or unauthorized access to information. User privileges must be limited in order to limit possible accidental or malicious misuse of applications and resources. If these areas are not addressed, attackers, malicious insiders, or careless users might negatively impact the reliable operation of the BES.
For organizations that are required to be CIP compliant, Tenable.sc Continuous View (CV) can lead the way to compliance. This dashboard can assist in monitoring user access management and control, including monitoring changes to accounts, privileges, and groups. The dashboard also highlights account and credential vulnerabilities, such as default accounts and password disclosures. Provided appropriate audit scans are run on the network, access control and least privilege compliance metrics will also be displayed. This dashboard can assist an organization in meeting the CIP-004 R4 and R5 and CIP-007 R5 requirements and measures. Analysts can also use this dashboard to easily drill down and gain more detailed information.
The CIP standards recommend categorizing BES Cyber Assets into different impact categories. An asset's impact category is based on the adverse impact to BES reliability that would occur if the asset was unavailable, degraded, or misused. Once the impact categories of systems have been determined, asset groups in Tenable.sc CV can be used to group together machines in each impact category. Asset groups can then be applied to this dashboard to narrow the focus and enable more accurate reporting on systems in specific impact categories. For more information on using assets with dashboards, see How to Add Assets in SecurityCenter and How to Use Assets with Dashboards. Alternatively, if the assets are in separate subnets, then subnet filters can be easily applied to narrow the focus of this dashboard.
This dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- SecurityCenter 5.2.0
- Nessus 8.4.0
- NNM 5.8.1
- LCE 6.0.0
- Compliance data
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution. For Supervisory Control and Data Acquisition (SCADA) systems, where reliability and not interfering with normal operations is a concern, Tenable.sc CV includes passive vulnerability detection with Tenable’s Nessus Network Monitor (NNM), as well as log correlation with Tenable’s Log Correlation Engine (LCE). Where possible, active vulnerability detection and compliance scanning with Nessus can also be done. Using Tenable.sc CV, an organization will obtain the most comprehensive and integrated view of its SCADA network.
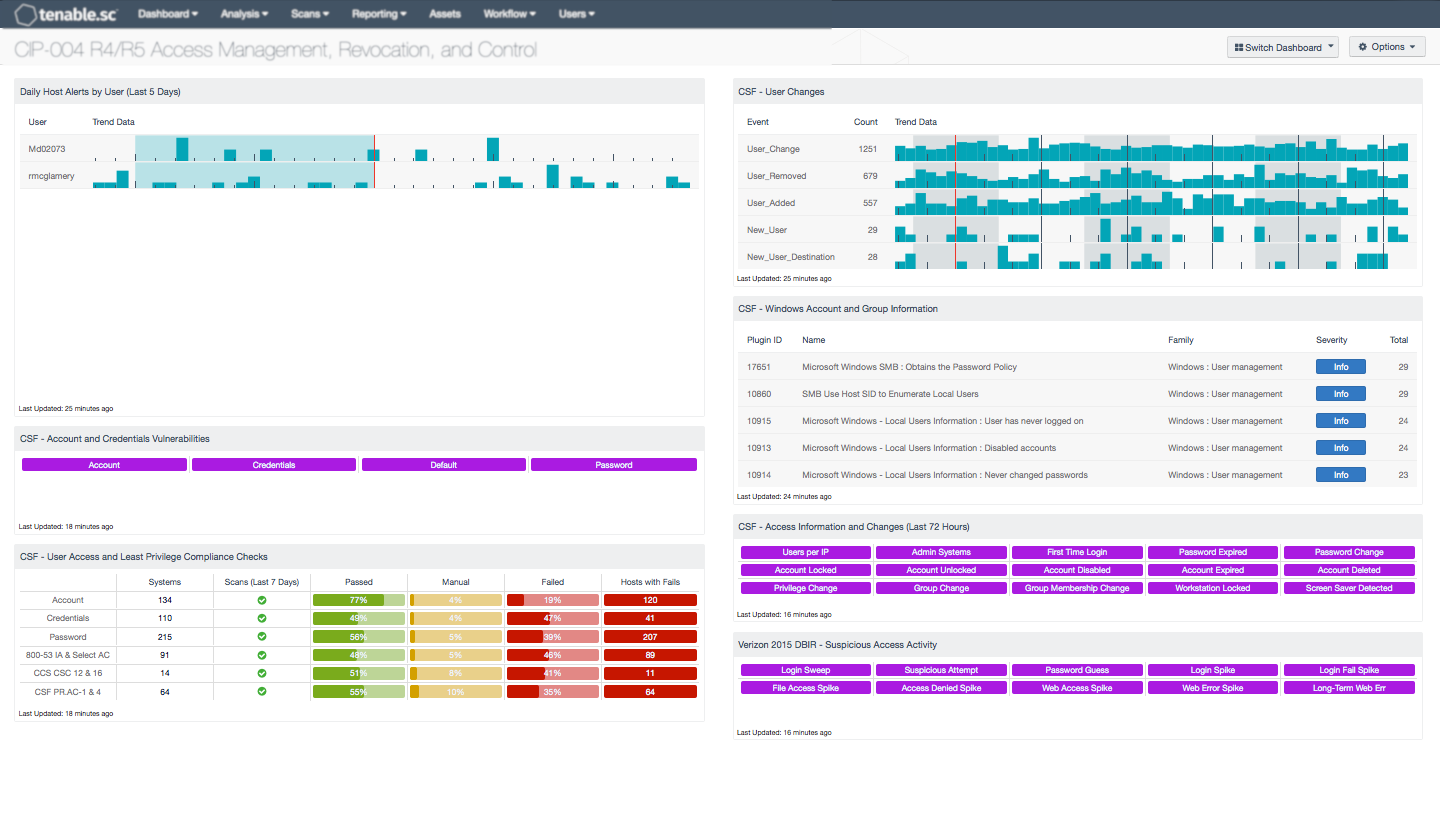
The following components are included in this dashboard:
- Daily Host Alerts by User (Last 5 Days): This table component displays alerts of user activity for the last five days.
- CSF - Account and Credentials Vulnerabilities: This component displays warning indicators for vulnerabilities actively and passively detected on the network related to accounts and credentials.
- CSF - User Access and Least Privilege Compliance Checks: This component displays user access and least privilege compliance information in areas such as password requirements, lockout policy after failed logins, and controlled use of administrative privileges.
- CSF - User Changes: The User Changes component presents data on new and existing user events on the network over the past 72 hours.
- CSF - Windows Account and Group Information: This table displays detections of Windows account and group information, such as accounts that have never been logged into, disabled accounts, and group user lists.
- CSF - Access Information and Changes (Last 72 Hours): This matrix component can help an analyst quickly pull up information on systems where certain user access-related events and changes have occurred.
- Verizon 2015 DBIR - Suspicious Access Activity: This matrix assists the organization in monitoring for suspicious access activity such as suspicious login activity and spikes in file and web accesses.