by Cody Dumont
July 31, 2014
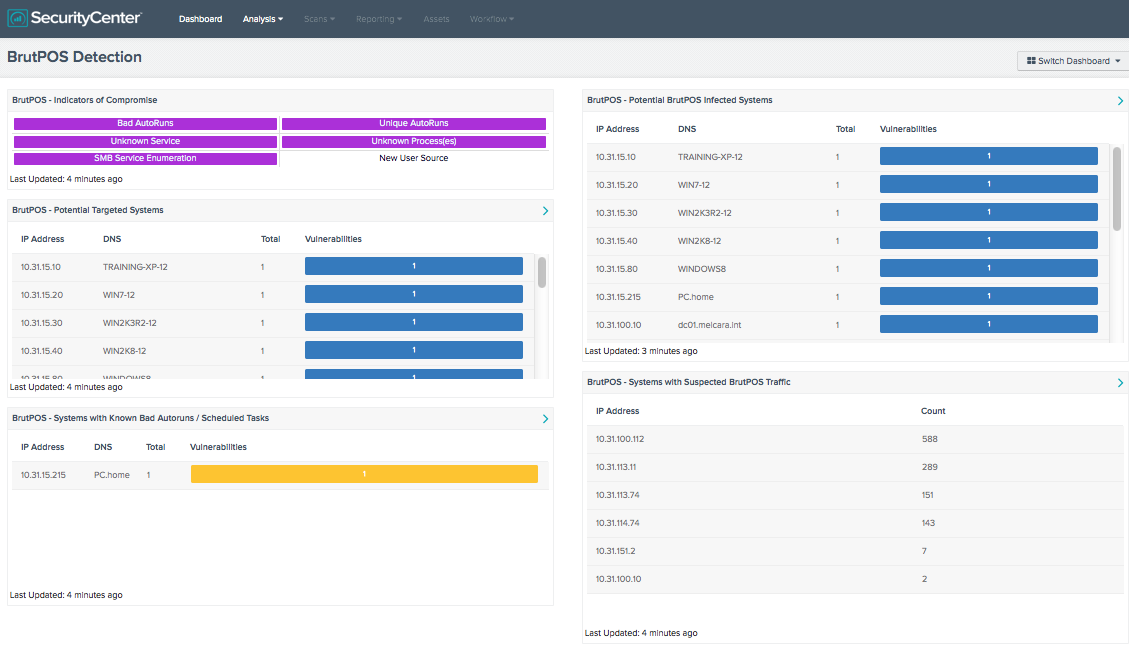
Attention all organizations with Point of Sale (POS) systems: BrutPOS malware is running rampant. By incorporating continuous network monitoring, SecurityCenter Continuous View (CV) can help identify systems at risk. Tenable’s Kenneth Bechtel https://discussions.nessus.org/thread/7629 blogged about how BrutPOS malware is spreading and targeting POS machines. This dashboard provides several of the indicators of compromised systems. Using the continuous network monitoring approach, this dashboard detects vulnerabilities using regex pattern matching in the plugin output text, and monitoring the events related to the known Command and Control addresses.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Security Industry Trends.
The dashboard requirements are:
- SecurityCenter 4.8.1
- Nessus 5.2.7
- LCE 4.2.2
SecurityCenter CV has the ability to monitor the network continuously, and to quickly identify vulnerabilities related to a BrutPOS compromise. By implementing SecurityCenter CV, an organization can reduce risk by staying in compliance and proactively discovering systems at risk. By using Nessus to detect and assess risk within the network, PVS to perform deep packet analysis, and LCE to correlate logs and related event data, SecurityCenter CV provides the most comprehensive and integrated view of network health.
BrutePOS - Indicators of Compromise: The search for rogue applications can be difficult. This component provides a series of saved queries to focus on the most relevant plugins related to the BrutPOS malware. The first row of indicators report on AutoRun entries targeted by BrutPOS. The second row looks for services and processes. The last row is split between enumerated services and new user sources. The indicators will turn purple when a match is found.
BrutePOS - Potential Targeted Systems: The plugin 70329 (Microsoft Windows Process Information) reports details about the running processes on a Windows system. This plugin is informational, and could be used for forensic investigation, malware detection, and to confirm your system processes conform to your system policies. The first step in assessing the risk of BrutPOS is to identify the systems that are targeted by the malware. This component uses a regex and plugin 70329 (Microsoft Windows Process Information) to identify systems targeted by BrutPOS.
BrutePOS - Systems with Known Bad Autoruns / Scheduled Tasks: This table provides a list of hosts with bad or unknown AutoRuns detected. The plugin 74442 (Microsoft Windows Known Bad AutoRuns / Scheduled Tasks) discovers Windows systems with one or more registry entries that are known to be associated to malware. This indicates the system may have been compromised by malware.
BrutePOS - Potential BrutPOS Infected Systems: The plugin 70329 (Microsoft Windows Process Information) reports details about the running processes on machine Windows system. This plugin is informational and could be used for forensic investigation, malware detection, and to confirm your system processes conform to your system policies. The component is separate from the “BrutePOS - Potential Targeted Systems” table due a different regex. The regex used in this component adds the string “llasc.exe” as part of the search pattern. The “llasc.exe” executable is known to be created by the BrutPOS malware.
BrutePOS - Systems with Suspected BrutPOS Traffic: This component reports on communication traffic with the IP addresses known to be command and control servers for the BrutPOS malware.