by Cody Dumont
May 18, 2015
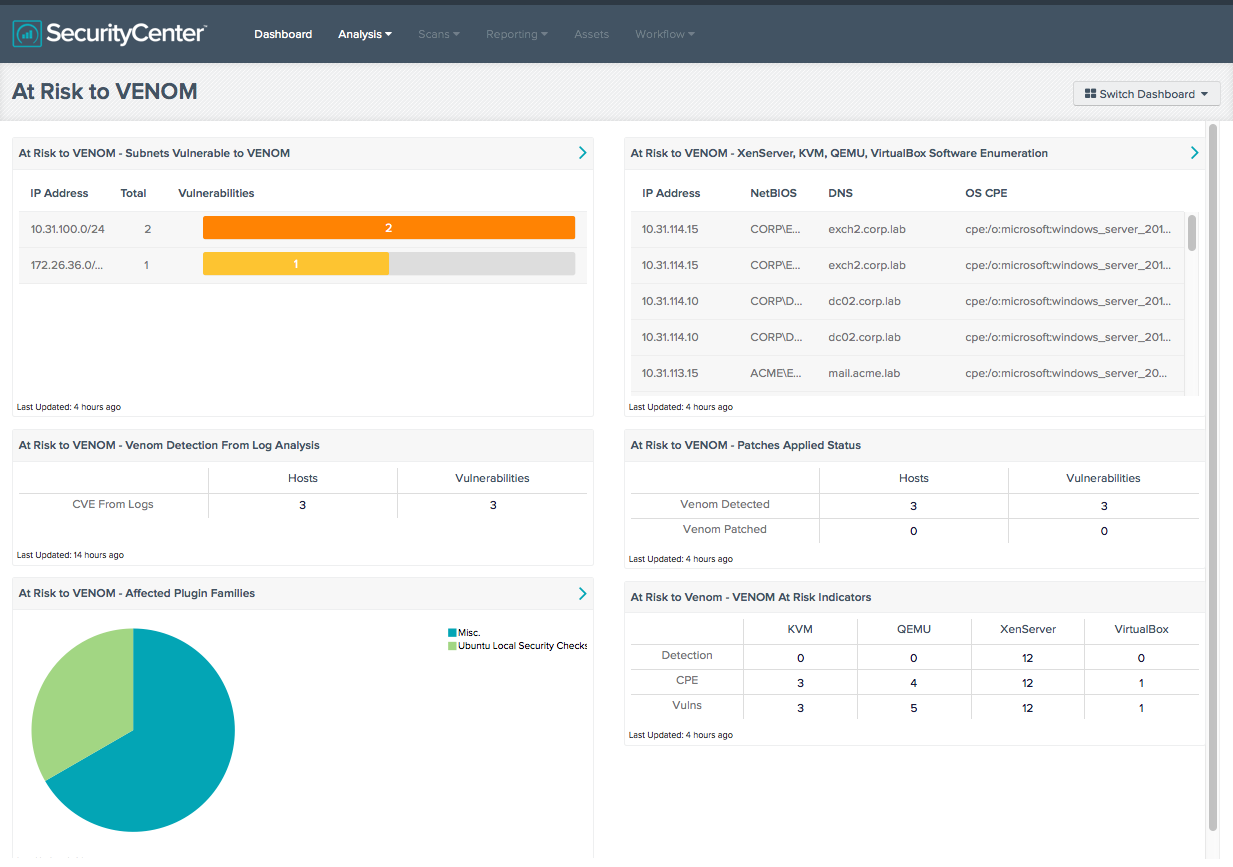
With the public announcement of VENOM (Virtualized Environment Neglected Operations Manipulation) vulnerability (CVE 2015-3456), how can organizations take a proactive approach to remediation? The VENOM vulnerability applies to VM guests and the hypervisors based on XEN and QEMU. This dashboard search for content related to XenServer, VirtualBox, QEMU, and KVM installations. This dashboard takes into account several technics such as software enumeration, CVE matching, and key word searches to help identify vulnerable systems.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Security Industry Trends.
The dashboard requirements are:
- SecurityCenter 4.8.2
- Nessus 6.3.6
The components in this dashboard utilize data collected from previous scans to help organizations respond to VENOM. The software enumeration component searches for systems with XenServer, VirtualBox, QEMU, and KVM installed. This will allow analysts to identify vulnerable systems before vendors release patches. There are other components that search for CPE strings and Vulnerability Name strings for the affected hosts. The remaining components search using the CVE 2015-3456.
One of the components reports mitigation progress. The first row searches using the CVE string in the cumulative database. The second row also using the CVE, but it searches with in the mitigated database. When a host is scanned, the results are stored in the cumulative database, as this where current vulnerabilities are stored. When the host is scanned again, if the vulnerability is no longer present, it is considered mitigated, and the results are moved to the mitigated database.
Users with SecurityCenter Continuous View and the Log Correlation Engine (LCE) deployed gain the benefit of extracting vulnerability data from logs collected and analyzed by the LCE. The LCE can identify vulnerabilities using various content in the logs to identify the vulnerability and associated CVE’s. The TASL summarizes software updates or installed, and keeps track of latest versions installed on each host. When new vulnerabilities are released, the LCE then identifies the vulnerability according to installed software.
SecurityCenter Continuous View (CV) provides organizations with proactive continuous monitoring to identify the newest threats across the entire enterprise. SecurityCenter CV enables the organization to react to advanced threats, zero-day vulnerabilities and new forms of regulatory compliance. SecurityCenter CV supports more technologies than any other vendor including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure.
Components
At Risk to VENOM - Subnets Vulnerable to VENOM: This table provides a list of subnets and the count of systems vulnerable to VENOM. Using the CVE to match vulnerabilities, these subnets have been confirmed to have vulnerabilities susceptible to VENOM vulnerabilities. The VENOM vulnerability could allow an attacker to escape the guest OS, and have access to the hypervisor kernel. The table shows the affected networks, total number of vulnerabilities, and a summary bar that is broken down by severity.
At Risk to VENOM - VENOM At Risk Indicators: This matrix identifies systems that may be vulnerable to VENOM. Using several search techniques to identify possible vulnerable systems, the analyst can take a proactive approach to mitigating the risk before vendors publish patches. The first row searches using the “detection” plugin IDs. The second row searches using CPE strings and the third row using plugin names. There could be false positives found in this table, however the content should be reviewed to allow for a proactive assessment.
At Risk to VENOM - Patches Applied Status: The matrix reports mitigation progress. The first row searches using the CVE string in the cumulative database. The second row also using the CVE, but it searches with in the mitigated database. When a host is scanned, the results are stored in the cumulative database, as this where current vulnerabilities are stored. When the host is scanned again, if the vulnerability is no longer present, it is considered mitigated, and the results are moved to the mitigated database.
At Risk to VENOM - XenServer, KVM, QEMU, VirtualBox Software Enumeration: This table provides a list of hosts that have XenServer, KVM, QEMU, VirtualBox software programs installed. Hosts identified by this table may not be vulnerable, but do have software related to vulnerability installed. For example, on a Windows computer, Citrix XenCenter (XenServer management software) could be present, but that is not vulnerable to VENOM. However this is another method to identify potential at risk systems.
At Risk to VENOM - Affected Plugin Families: This chart provides a summary view of the affected systems. The filter uses the CVE to identify the applicable plugin families. The chart will provide a summary count of the top 10 plugin families, and if more that 10 are present, a group called other will represent the other families.
At Risk to VENOM - Venom Detection From Log Analysis: This matrix provides users with the ability to identify vulnerabilities systems from CVEs collected via log analysis.