Nessus Compliance Checks for the Brocade Fabric OS
A new compliance plugin and audit file for auditing Brocade Fabric OS-based devices are now available for Tenable customers.
Brocade Fabric OS (FOS) runs on the Brocade family of Fibre Channel and FICON backbones and switches.
With this new plugin and audit file, Tenable customers can now audit their Brocade Fabric OS configurations for industry best practices, including checks for:
- Password policy
- Enabled services
- Lockout policy
- Insecure service configuration
- Authentication
- Logging and audit settings
To perform a Brocade Fabric OS audit, you will need:
- Root/admin credentials for SSH access, or a configuration file for offline configuration audits (as detailed in this blog post).
- Plugin #71842, which is now in the plugin feed in the Policy Compliance family
- The Brocade Fabric OS audit policy, now available from the Tenable Support Portal (see this Discussions Forum post for more info)
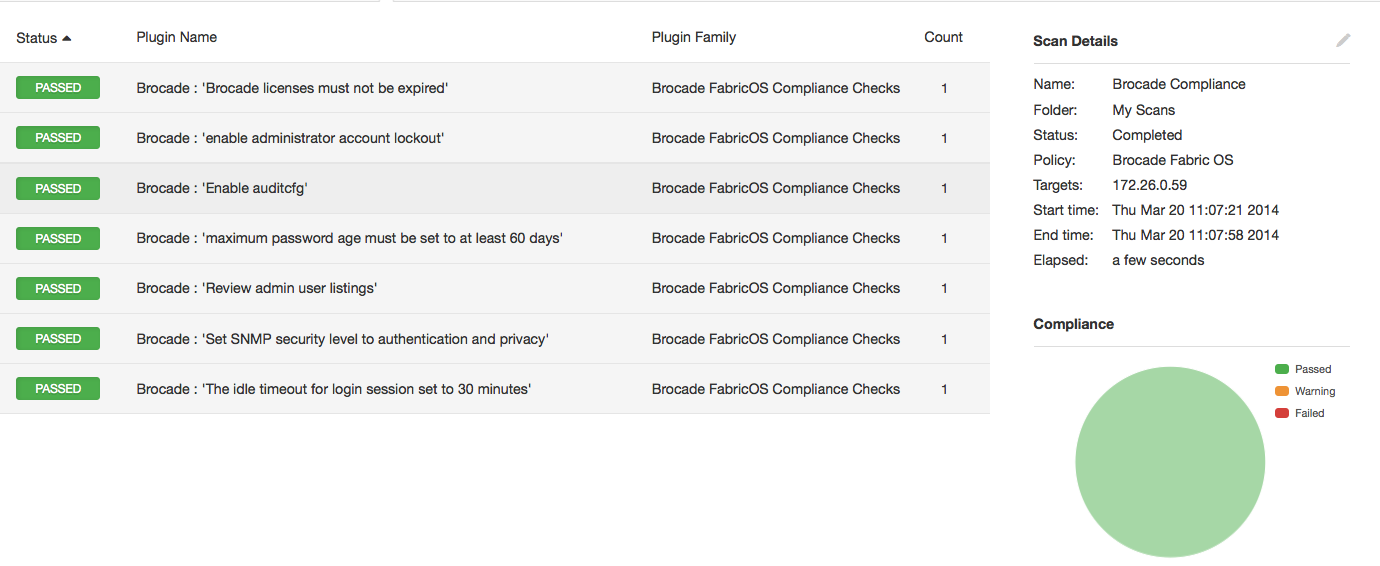
Sample configuration audit results are shown below in the familiar Nessus compliance format. Detailed findings include solutions to any failed configuration settings.
Auditing the configuration of Brocade Fabric OS devices further extends Tenable’s capabilities to help secure your company’s infrastructure. For further information about using Nessus to audit your network, security, or virtual infrastructure, view the following posts:
- Auditing Network Devices Without Scanning
- Nessus Audits HP ProCurve Routers
- Nessus Helps Harden FireEye Appliances
- New Nessus Configuration Checks Available for Citrix XenServer
- Nessus Secures NetApp Data ONTAP
- Nessus VMware vSphere/vCenter Audits Available
- Nessus Audits Palo Alto Networks PAN-OS Configurations
- Configuration Auditing Cisco Nexus Operating System (NX-OS) with Nessus
- Nessus Compliance Checks Available for Check Point GAiA
- Nessus Audits Juniper Junos Configuration
- Nessus Cisco Compliance Checks
Learn more
- Nessus
- Plugins
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success