Cybersecurity Snapshot: 6 Things That Matter Right Now

Topics that are top of mind for the week ending Oct. 21 | The problem with Gen Zers and Millennials | Global shortage of cybersecurity pros worsens | An informal poll about attack surface growth | Password usage drops a bit | And much more!
1 – CISOs beware: Younger workers take more cyber risks
This may sound counterintuitive but employees between ages 18 and 41 tend to be less careful regarding cybersecurity. So take note, CISOs: You may need to intensify security awareness and training efforts aimed at workers from the Gen Z and Millennial generations.

Although they’re tech savvy “digital natives,” these employees are more likely to engage in risky behavior than their older counterparts, according to Ernst & Young’s “2022 EY Human Risk in Cybersecurity Survey.”
Specifically, a higher percentage of Gen Zers and Millennials:
- re-use passwords for personal and professional accounts
- ignore required IT updates for as long as possible
- accept browser cookies every time or often
Recommendations for strengthening employees’ cybersecurity knowledge and preparedness include:
- Provide training that’s relevant to their roles at least once a year. This makes them more likely to adopt practices like using strong passwords, flagging phishing attempts and encrypting data.
- Don’t respond to employee mistakes with punishments but rather with education. A positive security culture makes employees more willing to seek help and report incidents.
- When providing security training, don’t limit it to workplace practices, but rather include information that’s applicable to employees’ personal lives.
For more information about the survey, which was based on a poll of 1,000 U.S. employees who use a work-issued computer, read a summary of the findings.
More resources about employee security training:
- “Cybersecurity Awareness: Six Tips to Help Your Employees Be Cybersmart” (Tenable)
- “Security Awareness Training: 6 Important Training Practices” (EC-Council)
- “A compassionate approach to employee security awareness” (Tenable)
- “Security Awareness Training for the Workforce: Moving Beyond 'Check-the-Box' Compliance” (U.S. National Institute of Standards and Technology)
- “Cybersecurity awareness tips to empower your team to #BeCyberSmart” (Microsoft)
2 – Security concerns hurt usage of digital government services
To boost citizens’ usage of their digital services, government agencies worldwide must improve on several fronts, including cybersecurity. As things stand now, there’s a global “confidence gap” in governments’ ability to secure citizens’ digital data.
That’s according to a new Accenture study titled “Public service experience through a new lens,” based on a survey of 5,500 consumers and 3,000 public service workers in 10 countries in North America, Europe and Asia-Pacific.
A key finding: 53% of people surveyed said that accessing public services is frustrating. Overall, the study found citizens want public service experiences to be simple, empathetic and secure.

Zooming in on the security aspect, the study urges governments to boost their security practices to strengthen the level of trust placed on them by both citizens and public servants.
- Among citizens surveyed, only 49% said they’re confident that government agencies use their data for what they say.
- Only 33% of government employees surveyed said they receive cybersecurity and data security training.
- 43% of respondents said they’d be more likely to access digital government services if they felt more confident about data security and privacy.
So how can government agencies improve in this area? According to Accenture, the solution goes beyond technology and involves, among other things:
- Turning agency leaders into security champions
- Dissolving organizational silos
- Prioritizing cultural changes
- Improving public awareness via “transparent” outreach campaigns
For more information, check out a summary of the report or read the full report.
3 – Passwords used less, but still reign among auth methods
The usage of passwords has dropped, but they remain the number one authentication mechanism, dwarfing arguably more secure and convenient methods.
So says a report from the FIDO Alliance, a tech industry consortium that aims to promote the usage of alternative login technologies and the creation of authentication standards.
In its second annual “Online Authentication Barometer” report, the group says password usage is down by 5% to 9% across five main use cases, while the use of one-time passcodes (OTPs) delivered via SMS has inched up between 1% and 4%.
However, the group considers SMS OTPs a “legacy” multi-factor authentication method that offers a minor improvement over passwords, and advocates for the adoption of what it calls modern and “phishing-resistant” methods like on-device biometrics, FIDO security keys and passkeys.
As long as passwords remain the dominant login method, organizations will be impacted by the negative consequences of forgotten and stolen passwords, according to the report, which is based on a survey of 10,000 consumers in 10 countries.
Frequency of abandoned purchases due to forgotten passwords
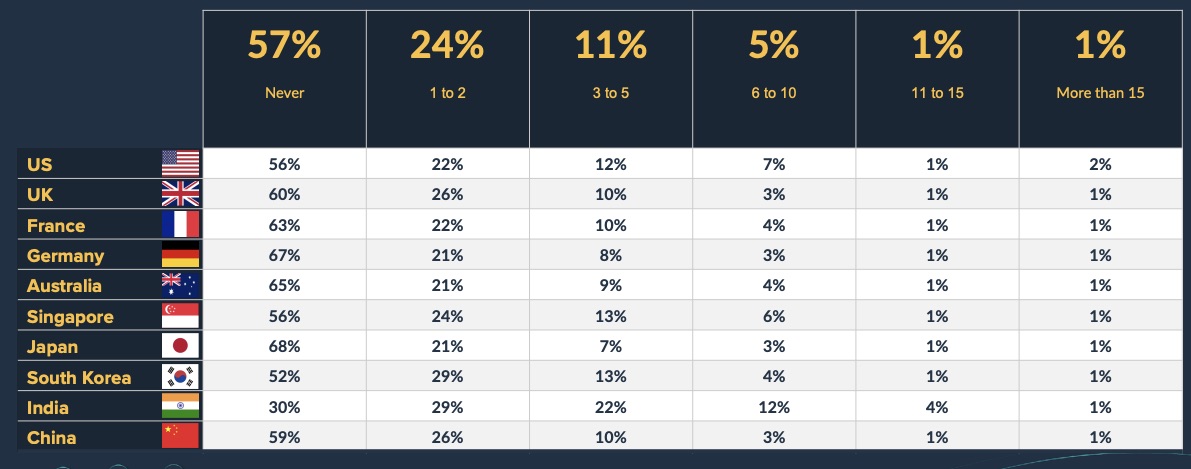
(Source: FIDO Alliance’s “Online Authentication Barometer” report, Oct. 2022)
For more details, read the report.
And here’s more information about the FIDO Alliance and the push for password-less authentication:
- “Next Level MFA: FIDO Authentication” (U.S. Cybersecurity & Infrastructure Security Agency)
- “A Big Bet to Kill the Password for Good” (Wired)
- “Infographic: What is FIDO?” (SC Magazine)
- “The FIDO Impetus to Passwordless Authentications” (RedmondMag)
- “There’s a big problem with Apple and Google’s plans to nix passwords” (Fast Company)
4 – U.S. companies struggle to fill cybersecurity jobs
Cybersecurity recruiters’ lives aren’t getting any easier. How bad is it out there? Currently in the U.S., there are 65 workers – most of them employed – for every 100 jobs posted.
Meanwhile, demand for cybersecurity pros is outpacing demand for employees across the board, growing 2.4 times faster in the 12-month period ending Sept. 30. Cybersecurity job postings in the third quarter were up 30% year-on-year, and up 68% compared with 2020.
Those Halloween-like stats come via the CyberSeek workforce analytics platform, a joint effort from the U.S. National Initiative for Cybersecurity Education, Lightcast and CompTIA.
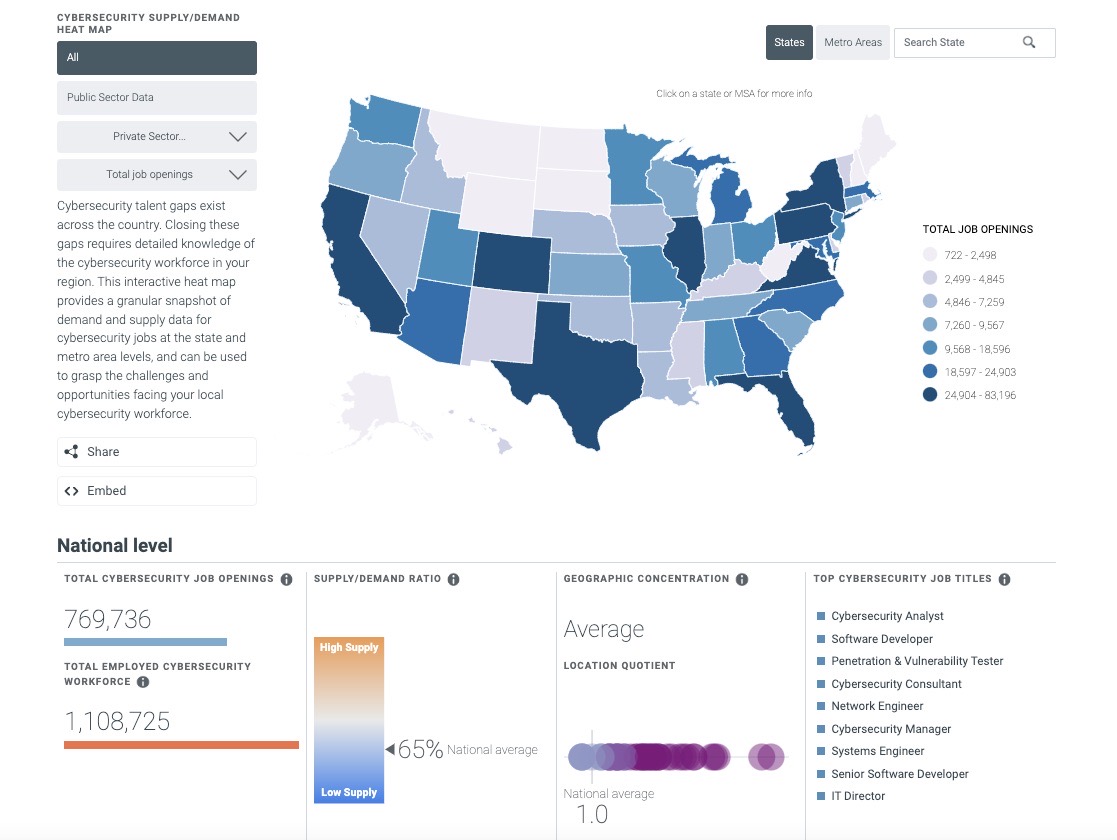
(Source: Cyberseek Heatmap on Oct. 20, 2022)
5 – And the staffing situation isn’t much better globally
3.4 million. That’s the number of cybersecurity pros needed to close the staffing gap worldwide, according to the (ISC)² Cybersecurity Workforce Study.
Although the cybersecurity workforce grew by 464,000 and stands at an all-time high of 4.7 million people, the situation didn’t improve in the past year. Why? The staffing gap grew 26.2% – more than twice the growth of the workforce.
The consequences of this problem are significant, as shown in the graph below, based on the study’s survey of almost 5,000 cybersecurity pros whose teams have staff shortages.
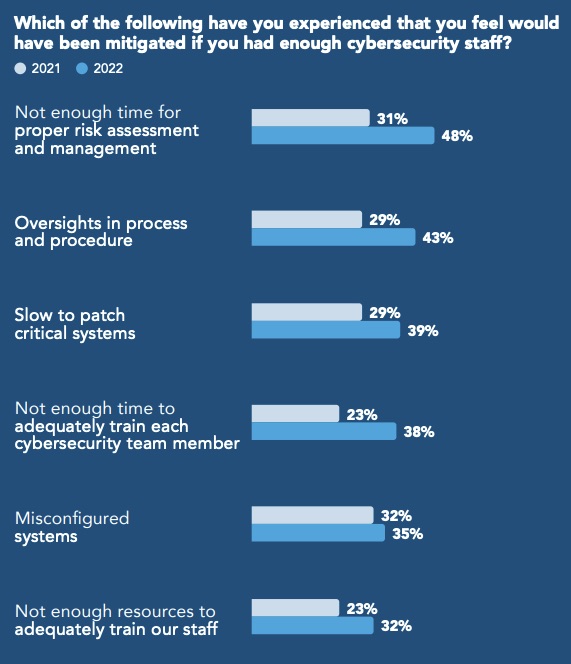
(Source: “ (ISC)² Cybersecurity Workforce Study”, Oct. 2022)
So what can be done? This a sampling of steps organizations are taking to attract and retain workers, based on the report’s survey of almost 12,000 cybersecurity pros and decision makers globally:
- Provide flexible conditions, such as working from home (cited by 64% of respondents)
- Invest in training (64%) and in certifications (58%)
- Automate aspects of cybersecurity jobs (57%)
- Hire for aptitude and attitude, and train for technical skills (50%)
- Broaden geographic boundaries for hiring
- Recruit among employees who don’t work in IT and security
For more information about this topic:
- “Latest Cyberspace Solarium Commission 2.0 Report focuses on cyber workforce” (CSO Magazine)
- “Struggling to fill IT, cybersecurity jobs? Look for non-tech candidates” (Tenable)
- “Cybersecurity skills gap: Why it exists and how to address it” (TechTarget)
- “Cybersecurity teams need to fill jobs. They’ll need entry-level roles.” (Protocol)
- “Hiring entry-level and junior candidates can alleviate the cybersecurity skills shortage” (TechRepublic)
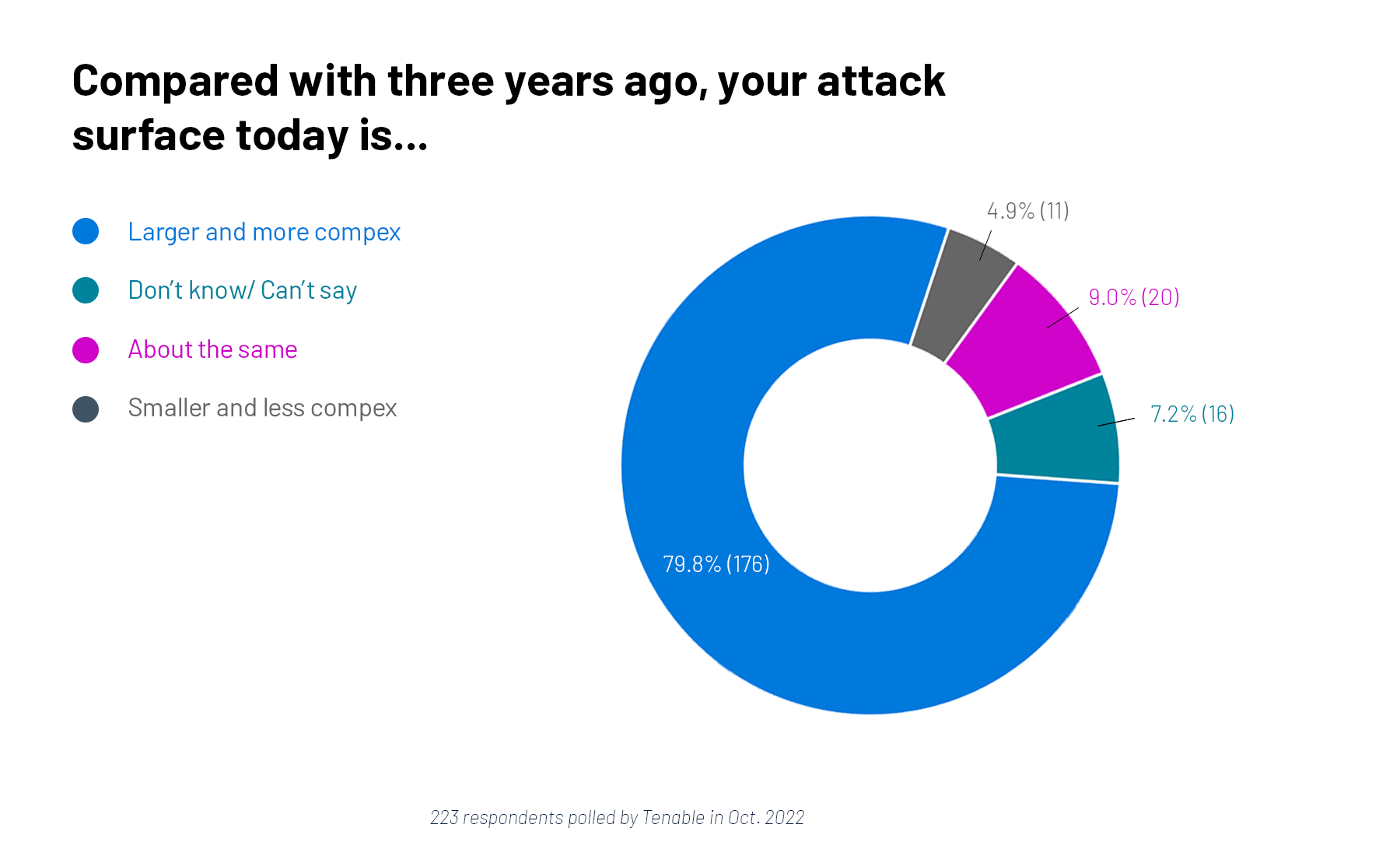
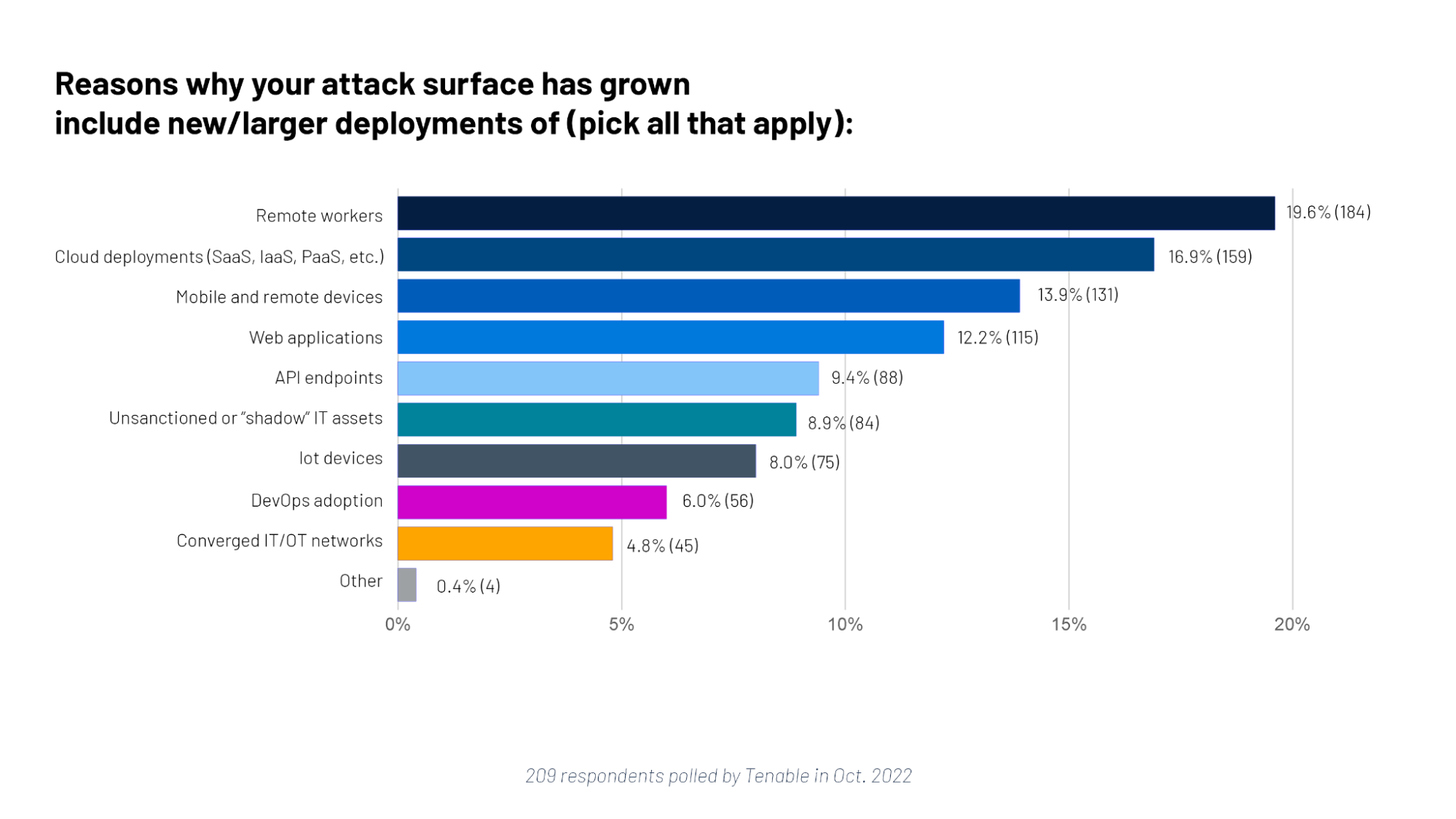
6 – A poll on attack surface woes
It’s no secret that the attack surface is expanding due to the adoption of modern technologies that make IT environments more distributed, heterogeneous, ephemeral and, ultimately, harder to defend. To get a reality check, we polled Tenable webinar attendees on this topic, and this is what they said.
For more information, check out these Tenable resources:
- “Finally Finding the 'Unknown Unknowns' Across Your Entire Attack Surface” (blog)
- “From Risk-Based Vulnerability Management to Exposure Management” (infographic)
- “Exposure Management: Our Vision for Securing the Modern Attack Surface” (blog)
- “Understanding and Achieving Exposure Management” (podcast)
- “Exposure Management: Reducing Risk in the Modern Attack Surface” (blog)
- “Exposure Management for the Modern Attack Surface” (on-demand webinar)
- “3 Real-World Challenges Facing Cybersecurity Organizations: How an Exposure Management Platform Can Help” (white paper)
Learn more
- Attack Surface Management
- Cybersecurity Snapshot
- Exposure Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success