Finally Finding the 'Unknown Unknowns' Across Your Entire Attack Surface
CISOs dread the “unknown unknowns” – the assets, vulnerabilities, misconfigurations and system weaknesses that the security team hasn’t detected and thus hasn’t secured. These blind spots represent a golden opportunity for attackers – and a major security risk for organizations.
“Unknown unknowns.” It’s the answer I’ve heard most consistently from CISOs and other security leaders throughout my career when they’re asked: “What keeps you awake at night?” Most security programs are built to create broad visibility into the environment and identify where the organization is most at risk. With that insight, decisions can be made on how and where to best mitigate risk to reduce potential impact of loss to the business. In many ways, being a driving force within a risk management program is the core mission of any security effort. And while there are a number of tools and techniques that contribute to providing visibility, there is still a great deal of challenge around discovering and understanding the “unknown unknowns” and shifting them into the realm of what’s known. Once they’re visible and accounted for, security teams can leverage their risk decision-making engine and mitigate those risks like all the other known ones.
In recent years, we’ve seen two techniques in particular that are helping security teams close the gap on those “unknown unknowns”: External Attack Surface Management (EASM) and Attack Path Analysis (APA). Let’s discuss what these techniques are, why they’re becoming a critical part of a mature security program and how they help security organizations get their arms around their environment’s attack surface.
Attack surface management
One area that often hides “unknown unknowns” and that is particularly difficult to understand and manage is the externally-facing part of an organization’s infrastructure. Assets which are publicly and continuously accessible from the Internet are going to be the first things that an attacker will see and attempt to compromise, as they are expected to be connected to and even probed. Where this becomes a problem for defenders, though, is when there are assets out in the public space that they don’t know about. For example, there could be a leftover DNS entry, which could be hijacked by an attacker who intends to commit fraud with it, or a poorly secured server or web application that a well-intentioned developer has spun up as a test, but with the organization’s domain information. Typically, organizations have dozens of assets and services out there that security teams are not aware of – but attackers very likely are.
EASM technology specifically addresses this problem by continuously scanning and monitoring public-facing assets. These tools provide easy-to-digest searchability into whatever is found that is associated with an organization’s public assets (i.e., domain name, IP address space, etc.). Done right, EASM provides consistent, constant visibility into those public-facing assets, wherever and whatever they are. Anecdotally, when I have worked with organizations in my previous life as a consultant, EASM tools identify an order of magnitude more public-facing assets than most security teams believe they have. And with the rise of cloud infrastructure and environments, it’s easier than ever for developers, IT staff and yes, even the security team, to spin up new assets that may not be recorded or identified consistently. Leveraging EASM, though, means those potential attack vectors become known and steps can be taken to either bring them within the purview of the risk mitigation efforts or remove them outright from existence so they can no longer be maliciously utilized. It’s a powerful tool to shine a light into an area that’s very difficult to address without an automated toolset that can find, identify and organize Internet-exposed assets.
Attack path analysis
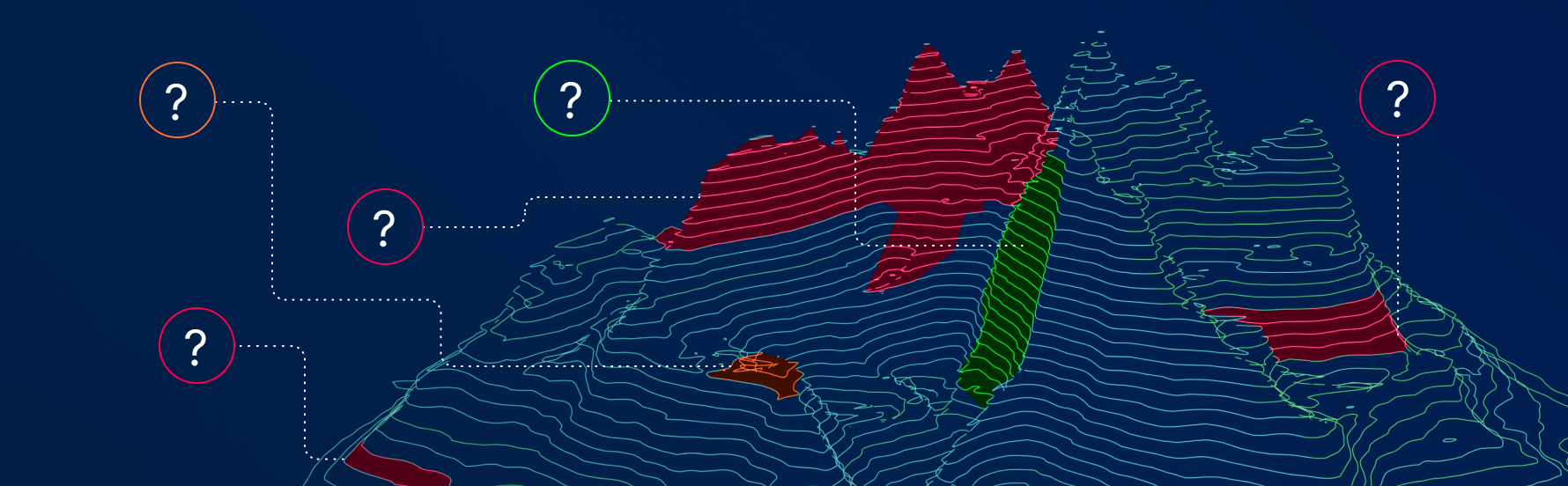
Now, if EASM can help identify the potential entry points for an attacker, then APA can identify which vulnerabilities, misconfigurations and other system weaknesses will likely be used to reach critical datasets and assets. At the most basic level, APA creates relationships between disparate types of security findings to pinpoint places that, unbeknownst to the security team, could be compromised, or areas where security controls can be circumvented to reach critical targets. Some SIEM tools and breach attack simulation (BAS) products attempt to identify these relationships between vulnerabilities , but their capabilities are either limited in scope or only replicate known attacks in static ways against a single vulnerability. However, APA technology approaches this from the bottom up, leveraging vulnerability assessment and exposure management efforts, which provide a more complete understanding of the configuration, vulnerability state and risk context for each asset. That way, APA tools can create a far better picture of the security posture of each asset and thus offer a more comprehensive view of the relationships between all of the data.
Think of it like this. If a nail puncture can cause a flat tire, then we know that there is a threat (nails) and a vulnerability (rubber is not impervious to punctures). We could use this information to test the other tires and confirm that there is a potential they’re also at risk from a nail puncture. But, if we tried to apply that same threat to other parts of the car, the analysis falls apart. The body of the car won’t suffer the same impact if a nail punctures the metal. The engine block might not even be damaged at all. Using a single threat and vulnerability type over and over again to assess the risk to the whole of the car doesn’t really provide meaningful information about what’s at risk and what could go wrong.
But, what if we related different types of threats that related to each other? A nail puncture could cause a flat tire, and if the tire blows out completely, the car may ride on the rim long enough to cause structural damage to the suspension or braking system. If the car is old or hasn’t been properly maintained, the domino effect could continue unfolding, causing damage to the engine or cooling systems. In this case, we’re seeing different types of threats and weaknesses, but we’re able to relate them to each other to see how there could be a broader, systemic failure that stems from a single, initial threat.
This holds true in exactly the same way for the modern attack surface within our organizations. A public-facing asset might be compromised because of a misconfigured port, which then allows the attacker to launch a SQL Injection attack from that host against a corporate web application. The breached application in turn exposes data that allows the attackers to obtain a username and password that provides access to another host. From there, they can launch a broader attack against a known exploitable Windows vulnerability that gives them elevated administrative access, which can then be used to traverse the internal network to reach whatever critical assets the attackers might want. This is a truer picture of how attacks unfold. , To successfully defend against attacks, we must be able to understand the entire path and where one vulnerability type can lead to exploiting another, often completely different type of vulnerability. This is the key for deciding where to implement security controls that are quick to deploy and cost effective, so that we can close the holes in our defenses we didn’t previously know about.
Defense-in-depth strategies have always been about layering security controls in a way that protects the assets and pathways we know about. APA surfaces the “unknown unknowns” of where an attacker is likely to strike and traverse through the environment, making those particular attack vectors “known knowns” and allowing teams to extend their controls to close those gaps.
No more “unknown unknowns”
As environments get more and more complex, the potential for attack vectors that are “unknown unknowns” goes up exponentially. Leveraging our existing best practices for vulnerability assessment, configuration assessment and risk management to serve as the foundation for an analysis of the relationships between all of those findings arms security teams with an invaluable tool to protect their infrastructure, reduce the number of “unknown unknowns” and, hopefully, sleep a bit better at night.
Want more guidance about your security strategy? Check out Tenable’s 2021 Threat Landscape Retrospective, which provides a comprehensive analysis of last year's threat landscape that security professionals can use to improve their security right now, and view the webinar "Exposure Management for the Modern Attack Surface: Identify & Communicate What's Most at Risk in Your Environment and Vital to Fix First."
Learn more
- Attack Surface Management
- Executive Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success