Deploying Your Industrial Cybersecurity: 4 Tips For Success

Securing industrial environments requires a form factor that is optimal for your business. The latest Tenable.ot product updates provide greater freedom to deploy your security and manage threats the way you want to see them.
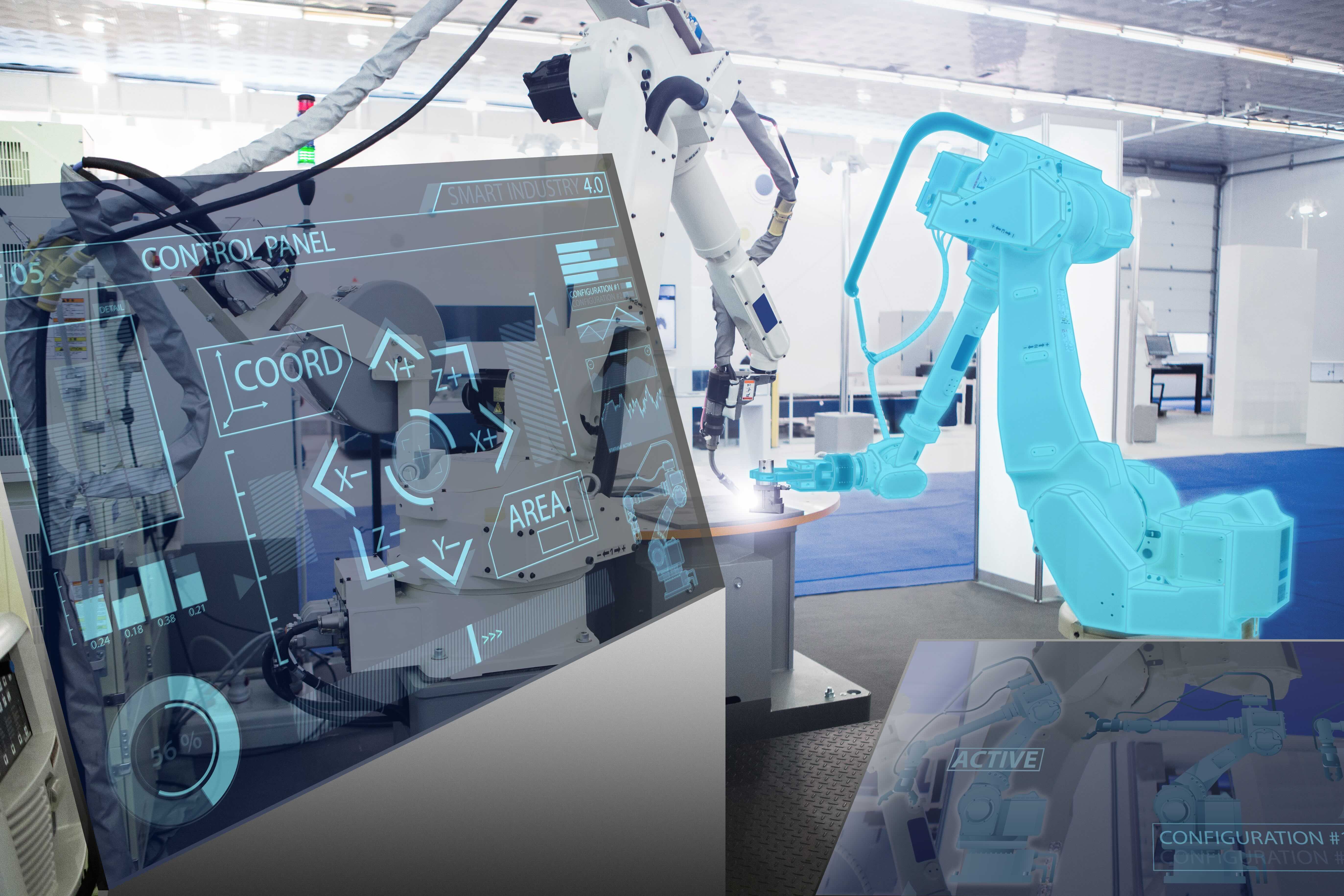
Every modern industrial organization needs a plan for securing their operational technology (OT) environments. If that wasn’t already clear, the latest alerts from the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and National Security Agency (NSA) offer clear evidence that OT cyberattacks have occurred and are ongoing. The continued rise of emerging technologies like IT/OT convergence and Industry 4.0 only further expose industrial environments to cyber risk.
OT security is essential to protecting critical infrastructure and capitalizing on new innovations. But the optimal way of deploying that security can differ based on your organization’s unique mission, goals and requirements. Like any other technology, OT security should be agile enough to operate around the business with minimal disruption, rather than the other way around. This is especially true during the COVID-19 response, as organizations seek greater agility in equipping their teams – both on-prem and remote – with the visibility, security and control they need to keep essential systems running.
We’re excited to announce a few updates to Tenable.ot™ that can help any industrial or critical infrastructure organization solve for the most urgent cyberthreats, in a way that maximizes uptime, safety and efficiency.
‘OT Anywhere’: Gain remote visibility into your OT infrastructure
We built Tenable.ot to support a variety of options for achieving visibility across your converged IT/OT operations. Building on our traditional appliance- and OS-based deployments, Tenable.ot is now fully integrated with Tenable.io. For the first time ever, you can leverage the power of the cloud to gain visibility into your OT infrastructure - from anywhere in the world with an internet connection.
As modern OT infrastructure converges with IT systems and connected devices, the cloud becomes a much more attractive, efficient and cost-effective way of managing and securing industrial environments. This is especially true if your organization is:
- Adopting data-rich Industry 4.0 workflows
- Deploying industrial IoT devices such as smart sensors, monitors and alarms
- Distributed across multiple locations
- Not able to accommodate additional gear
Rather than shipping staff members to remote locations to collect data or make adjustments, you can now pipe all of that OT information into the cloud and manage your controls from anywhere. This versatility is key to supporting more agile collaboration and innovating without introducing additional cyber exposure.
Achieve a single view of all your IT and OT vulnerability data
Visibility is the first part of the OT security equation; you also need a solution capable of managing the vast number of vulnerabilities that might exist across your converged IT/OT environment. Siloed views of one side or the other will inevitably create blind spots and lead to inefficient workflows.
Security teams can maximize their impact by finding a solution that prioritizes vulnerabilities based on the latest threat intelligence and recommends clear actions to reduce the greatest amount of risk with your limited resources. By harnessing the combined power of Tenable.ot and Tenable.sc, we’re proud that our platform is the first on the market to provide converged IT/OT vulnerability management, including
- A “single pane of glass” view with triaged threats across your IT/OT attack surface
- VPR scoring that predicts the 3% of vulnerabilities that pose the greatest risk
- Unparalleled asset discovery through patented Active Querying technology (for OT assets) and our Nessus® Professional integration (for IT assets)
Streamline your traditional OT security deployments
In addition to equipping your team with the latest capabilities, you also want to make sure you’re getting the basics right. For traditional deployments, Tenable.ot offers a dedicated appliance with optional sensors or deployment on your own gear that meets our tested minimum requirements. This is known as “Tenable Core.”
By packaging the application with a supported version of CentOS, Tenable Core further streamlines the deployment and management of multiple products, including Nessus, Tenable.sc, and the Nessus Network Monitor (NNM). This expedites your time to deploy and eliminates the disruption of a production environment.
The freedom to choose
The rising tide of industrial cyberattacks shows no signs of letting up anytime soon. Defending your critical infrastructure requires a solution capable of providing comprehensive security across your converged environment. With Tenable’s “OT Anywhere” initiative, you can now choose the optimal form factor for your organization to most efficiently guard your OT infrastructure against unacceptable threats.
To choose the right OT security technology that suits your needs, check out our industrial cybersecurity checklist for an overview of key criteria and capabilities your team should consider. When you’re ready to learn more, you can send us a note to schedule a demo.
Learn more
- OT Security
- SCADA
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success