Get started with Tenable’s exposure management solutions
Tenable One
Exposure management for your modern attack surface
Get comprehensive visibility across your modern attack surface with the Tenable One Exposure Management Platform to help your teams translate technical asset, vulnerability, and threat data into clear business insights and actionable intelligence.
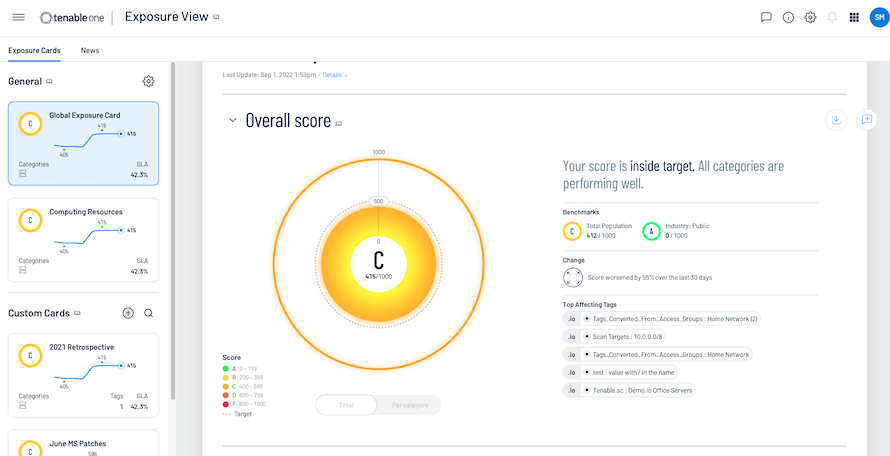
Key capability 1
Gain
a unified view of all types of assets and associated vulnerabilities, on prem or in the cloud.
Key capability 2
Anticipate
the consequences of a cyber attack proactively.
Key capability 3
Communicate
business-aligned cyber risk with peer benchmarking.
Buying security tools can be complex with various add-ons that make pricing hard. I consolidate security tools as much as I can, and with Tenable One it’s all included and streamlined.
Tenable One AI Exposure
Close your AI exposure gap with unified exposure management
Close your AI exposure management gap: the invisible attack surface that shadow AI, hidden attack paths, and data leaks create. Get a single, risk-aware perspective of all your AI tools and usage, cloud infrastructure, and identities so your security teams can stop reacting to isolated symptoms and start managing your AI security in one unified platform.
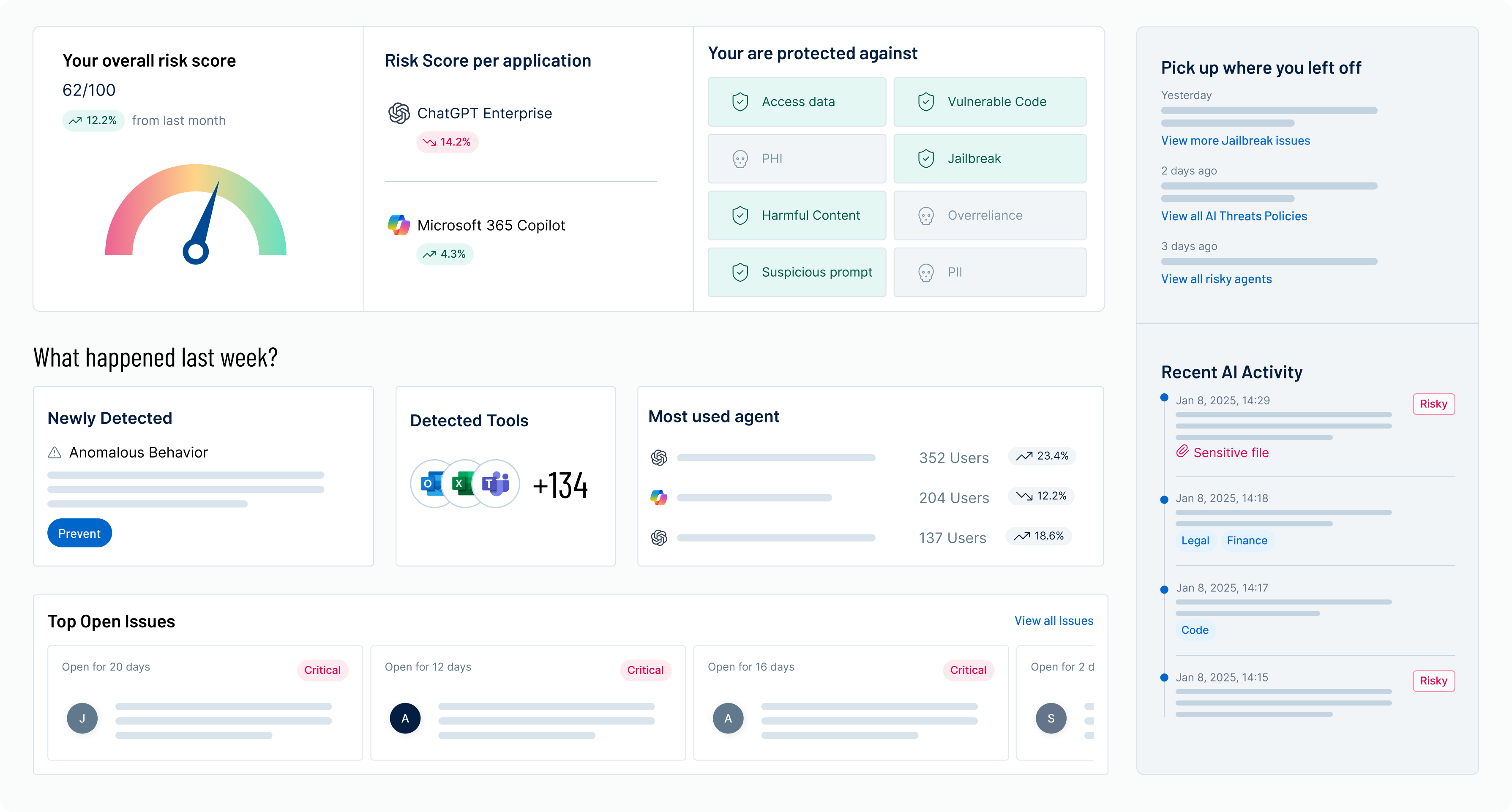
Key capability 1
Understand
how your organization uses AI.
Key capability 2
Secure
where AI creates risk.
Key capability 3
Close
gaps before attackers exploit them.
Tenable One Cloud Exposure
Experience unified cloud security posture and vulnerability management with Tenable One Cloud Exposure
Address your biggest risks in the cloud with Tenable One Cloud Exposure. Get a unified CNAPP and industry-leading CIEM that will give you context and prioritization guidance to make efficient and accurate remediation decisions. Easily spot and quickly address risks, even if you’re not a cloud security expert, in an intuitive user interface.
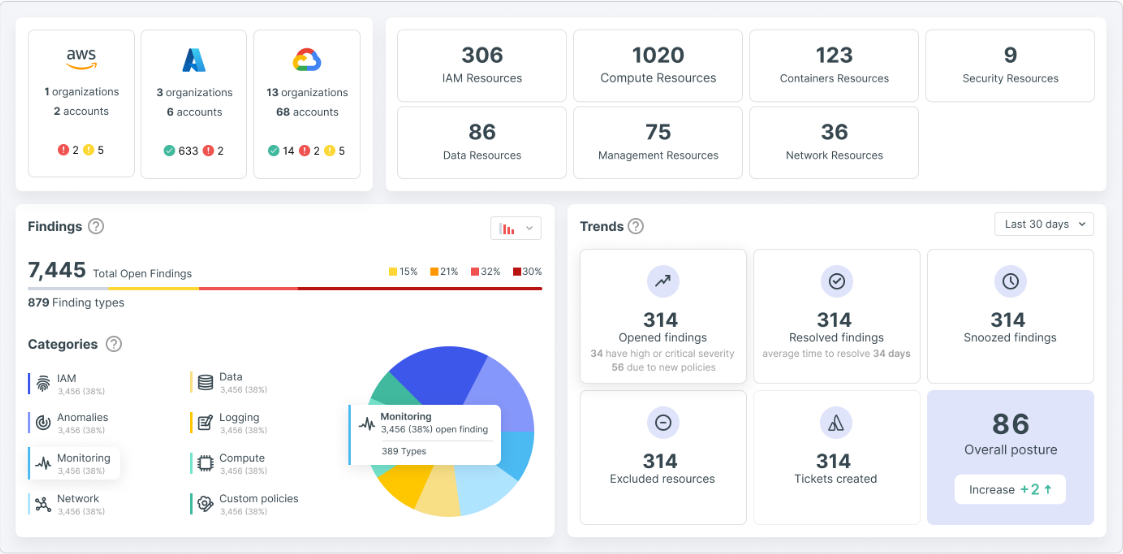
Key capability 1
Simplify
even the most complex issues with powerful visualizations and step-by-step remediation.
Key capability 2
Secure
cloud identities, permissions, and secrets, and enforce least privilege and zero trust across clouds.
Key capability 3
Accelerate
security across the organization with better collaboration across DevSecOps and IAM teams.
Tenable One Vulnerability Management
See everything. Predict what matters. Managed in the cloud.
Get a risk-based view of your entire attack surface — from IT infrastructure to cloud environments to critical infrastructure and everywhere in between — so you can quickly identify, investigate, and prioritize vulnerabilities. Powered by Nessus technology, Tenable Vulnerability Management provides the industry’s most comprehensive vulnerability coverage with the ability to predict which security issues to remediate first.
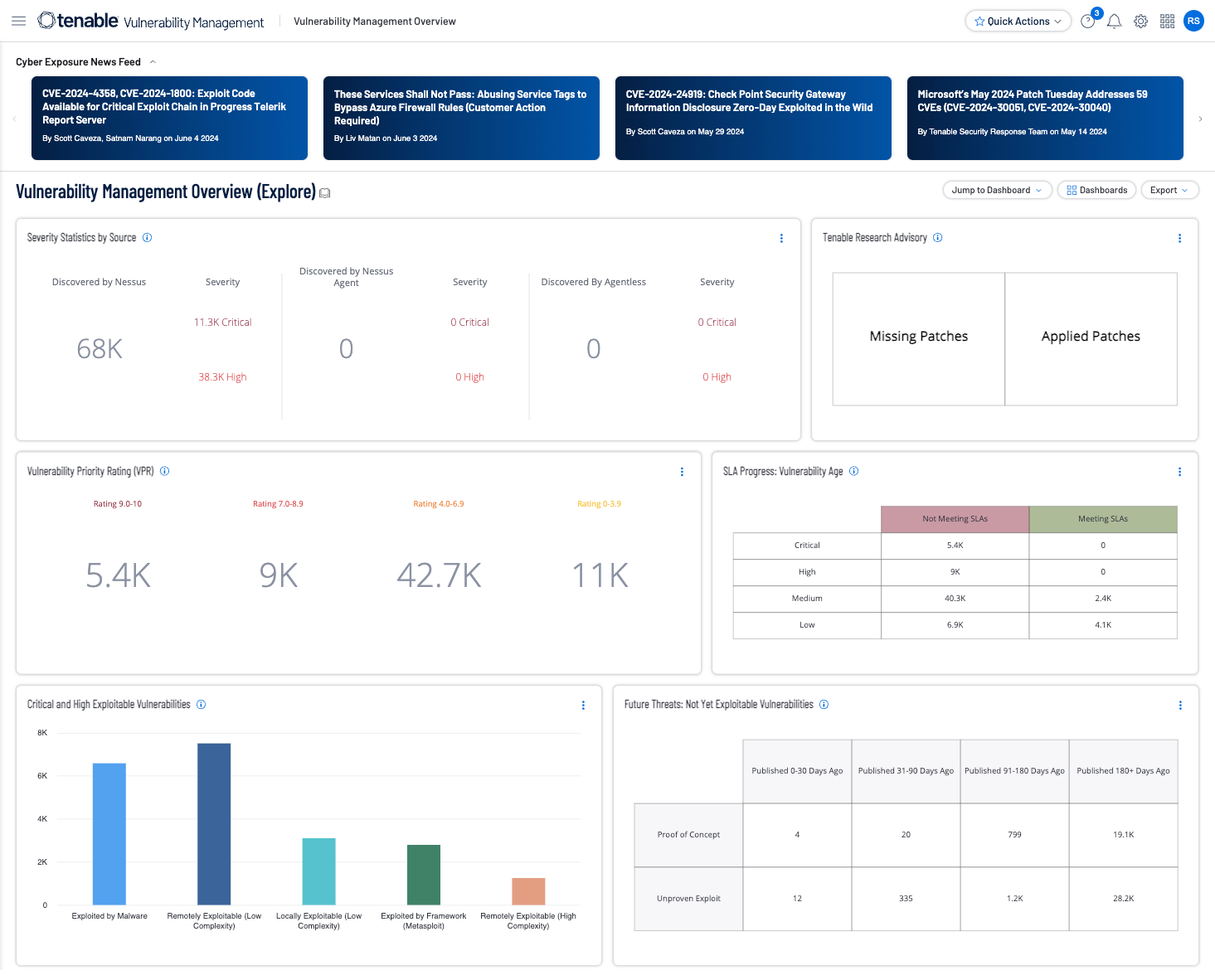
Key capability 1
Built
for cybersecurity leaders and practitioners.
Key capability 2
Predict
critical vulnerabilities to know what to fix first.
Key capability 3
Provide
unified visibility and a continuous view of all types of assets.
Tenable Security Center
See everything. Predict what matters. Managed on prem.
Get a risk-based view of your IT, security, and compliance posture so you can quickly identify, investigate, and prioritize vulnerabilities. Powered by Nessus technology, Tenable Security Center provides the industry’s most comprehensive coverage with real-time continuous vulnerability assessment for your network to predict which security issues to remediate first.
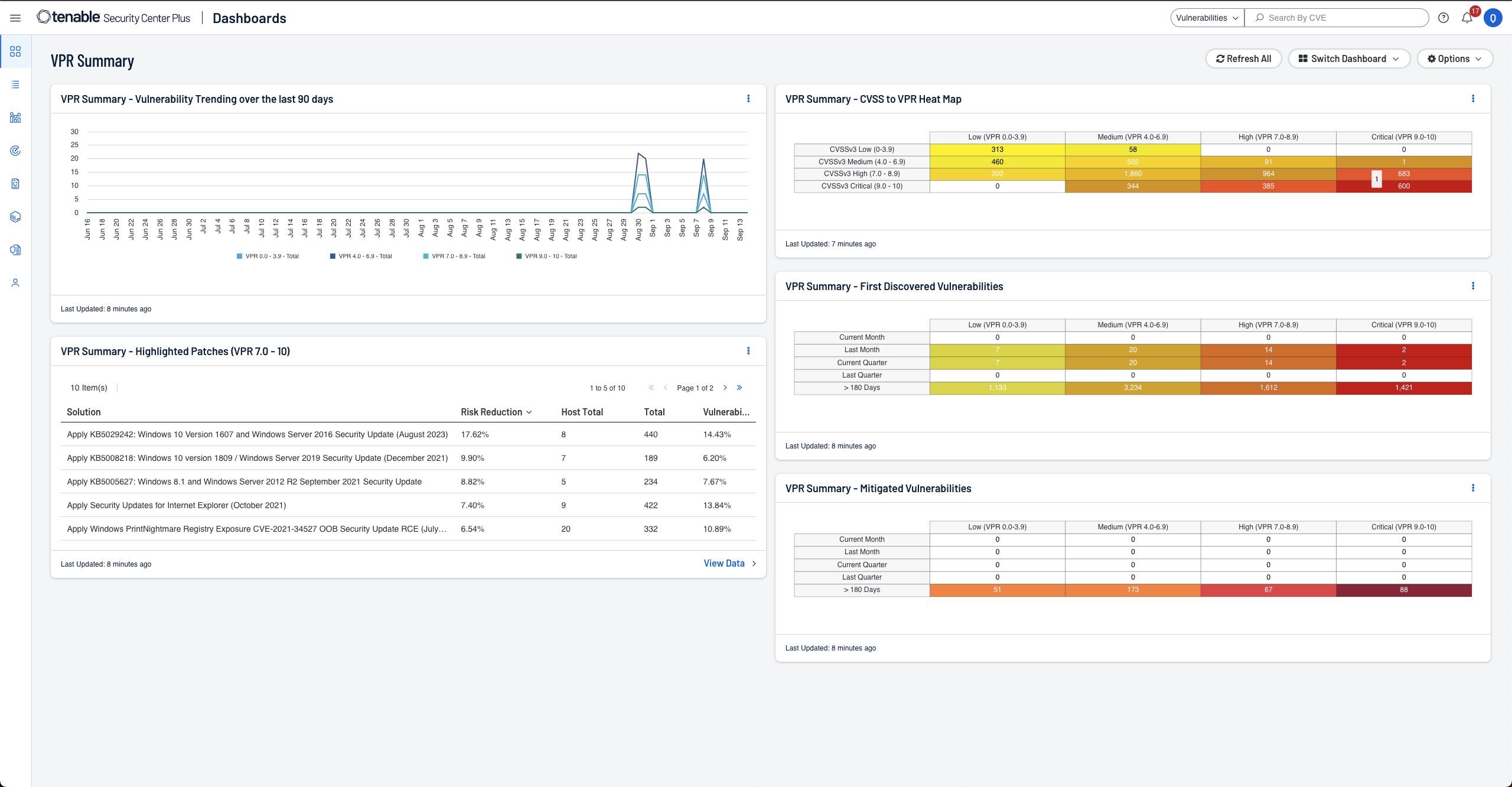
Key capability 1
Built
for cybersecurity leaders and practitioners.
Key capability 2
Predict
critical vulnerabilities to know what to fix first.
Key capability 3
Streamline
compliance reporting against regulatory mandates.
Tenable One OT Exposure
Get the operational technology you need. Reduce the risk you don’t.
Get the operational technology (OT) security you need and reduce the risk you don’t with Tenable One OT Exposure for asset inventory, vulnerability management, forensics support, and configuration controls. With complete visibility into your converged OT/IT infrastructure, you can maximize the safety and security of your OT environment.
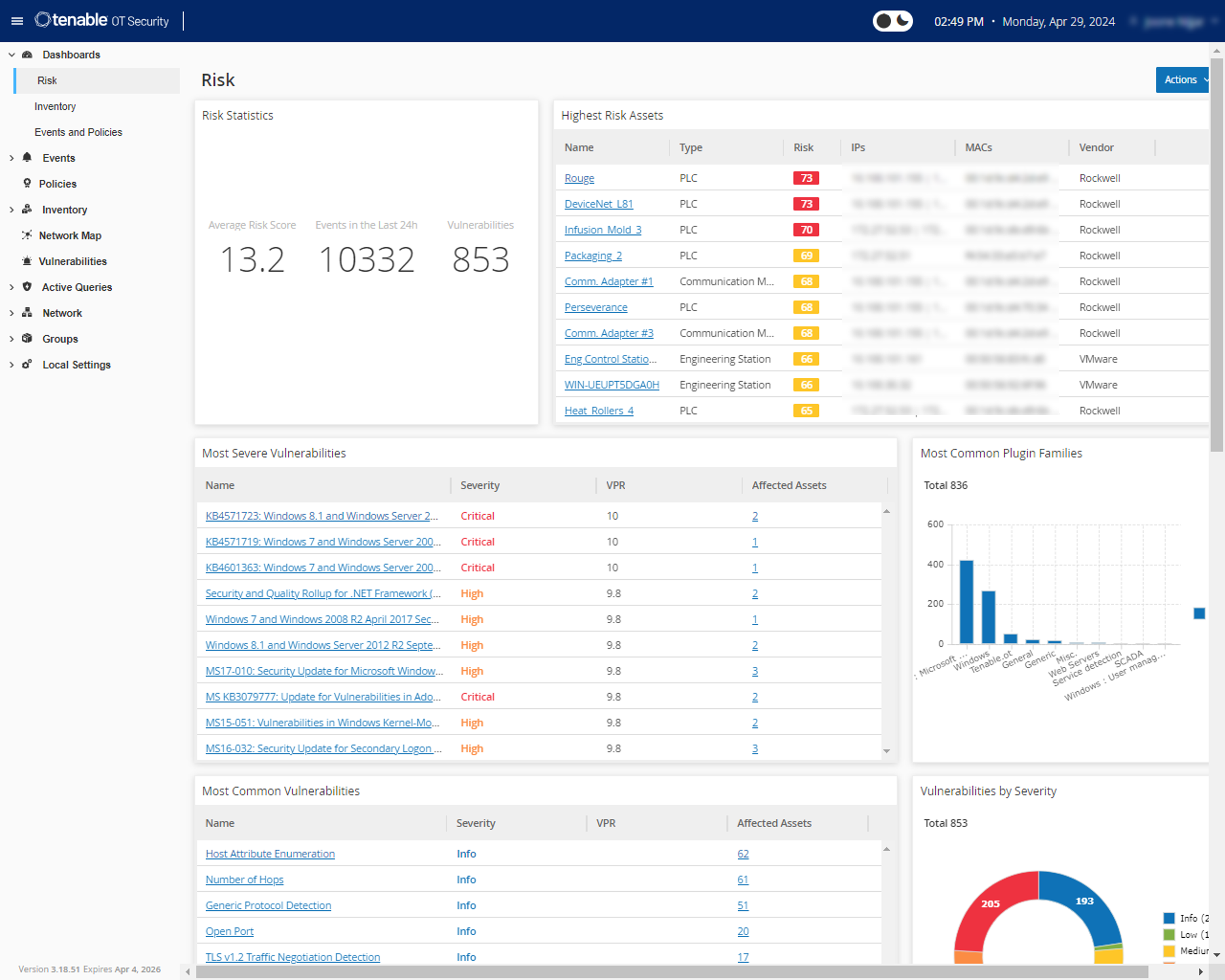
Key capability 1
Built
for cybersecurity (OT/IT) and compliance practitioners.
Key capability 2
Comprehensive
visibility into OT devices with active querying.
Key capability 3
Unified
OT and IT security in a single platform.
Tenable One Identity Exposure
Identity-led exposure management across Active Directory and Entra ID
Discover and prioritize identity risks across Active Directory, Entra ID, and hybrid environments to eliminate attack paths before attackers exploit them. Tenable One Identity Exposure continuously uncovers misconfigurations, excessive privileges, and dormant accounts — helping security teams see how attackers could move through their environment and take action before breaches occur.

Key capability 1
Discover
every identity and relationship across AD, Entra ID, and hybrid systems.
Key capability 2
Map
attack paths to reveal how exposures enable lateral movement and privilege escalation.
Key capability 3
Prioritize
and remediate with guided, actionable insights.
Tenable Nessus
Built for the modern attack surface
Nessus is one of the most widely deployed cybersecurity technologies on the planet. Every feature makes vulnerability scanning simple, easy, and intuitive, despite the complexity of the modern attack surface. With Nessus, you’ll spend less time and effort assessing, prioritizing, and remediating vulnerabilities so you can stay one step ahead of attackers.
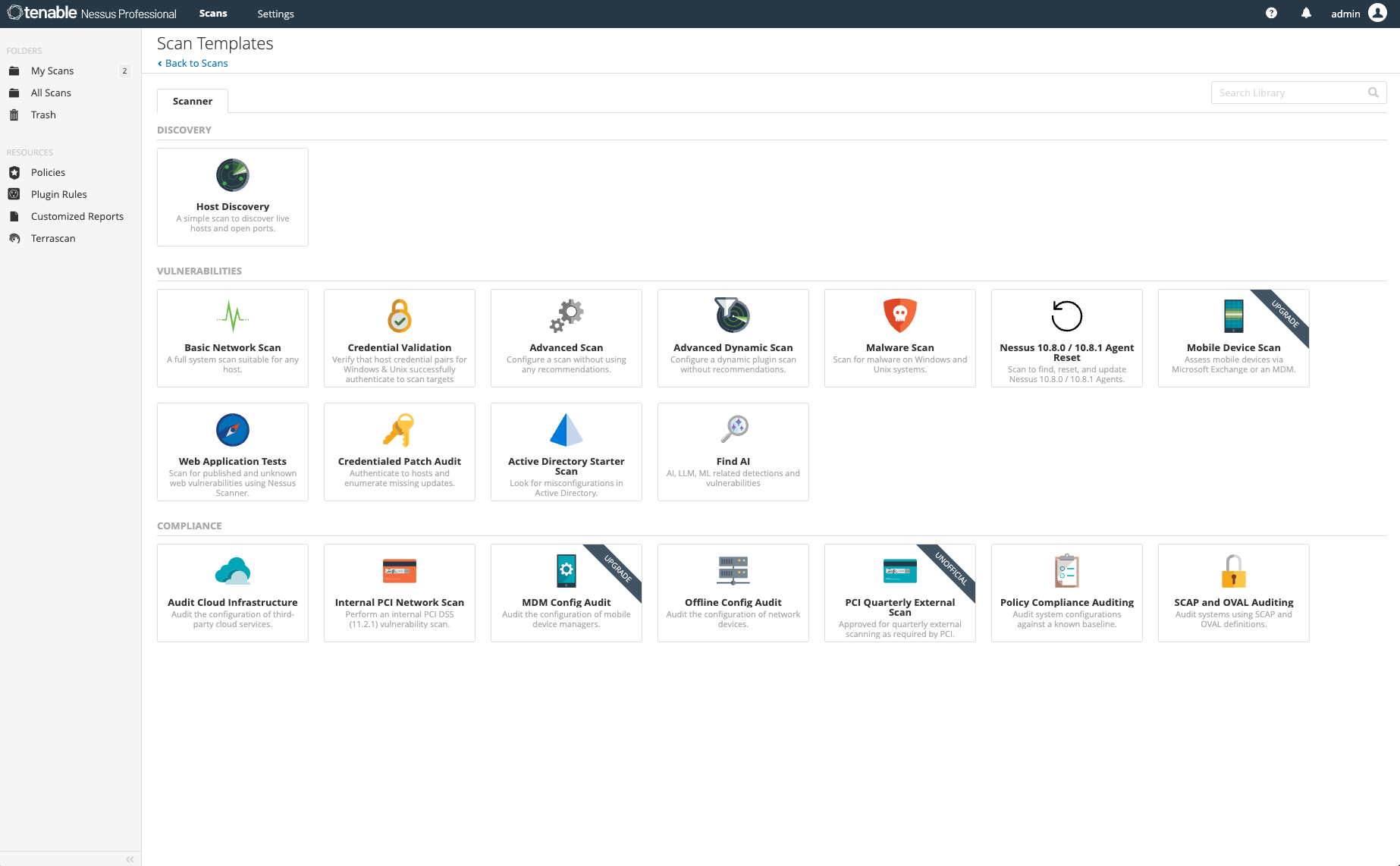
Key capability 1
Ideal
for consultants, pen testers, developers and SMBs.
Key capability 2
Industry’s deepest
and broadest CVE coverage.
Key capability 3
VA coverage
for IT assets, web applications, and attack surface discovery.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success