Organizations struggle to maintain comprehensive visibility across distributed infrastructure environments where assets continuously appear, evolve, and disappear without centralized tracking or validation. Security teams face mounting pressure to quantify and measure risk for diverse asset populations whose scanning status, authentication health, and vulnerability profiles remain fragmented. Additionally the team must reconcile conflicting asset inventories, credential failures, and incomplete scan coverage that impacts an accurate risk assessment. This report helps to unify asset discovery data, scan authentication indicators, and vulnerability detection results into a single report, allowing for the planning and execution of remediation actions.
Asset discovery is the foundation of effective vulnerability management by identifying assets through continuous assessment and identifying transient or decommissioned systems consuming licensing resources unnecessarily. Tenable Vulnerability Management helps organizations to deploy discovery scanning to identify live hosts across network ranges, enabling the identification of previously unknown assets into comprehensive vulnerability assessment processes before those systems introduce unmonitored risk vectors. Risk managers utilize these discovery metrics to evaluate scanning program maturity by comparing discovered asset populations against licensed asset allocations, revealing gaps where infrastructure expansion outpaces security program capacity. The distinction between discovered assets awaiting detailed assessment and fully assessed assets providing complete vulnerability profiles enables strategic decisions about scanning infrastructure investments and credential deployment priorities.
Monitoring the success of network and agent based scans provide visibility into authentication success rates, credential configuration problems, and scanning coverage gaps that directly impact vulnerability detection accuracy and remediation prioritization confidence. The security and IT operations teams work together to diagnose upstream scanning problems by analyzing authentication failure indicators, insufficient privilege notifications, and intermittent credential issues that prevent local security checks from executing successfully during vulnerability assessments. Authentication success indicators differentiate between assets receiving credentialed scans that enumerate installed software and detect configuration weaknesses versus uncredentialed scans limited to network-visible vulnerabilities, establishing confidence levels for risk quantification. Organizations experiencing persistent authentication failures across asset populations prioritize credential remediation initiatives and privilege escalation configuration to improve scan depth before investing in expanded scanning frequency or additional vulnerability assessment tooling.
Vulnerability prioritization enables organizations to focus remediation resources on genuine exploitation risk rather than addressing theoretical vulnerabilities based solely on severity classifications that ignore environmental context and threat intelligence. Tenable’s Vulnerability Priority Rating (VPR) leverages Artificial Intelligence to better forecast real-world exploitation likelihood based on threat actor behavior patterns. Leveraging VPR alongside traditional severity-based aggregation and port-based vulnerability analysis, the security team is able to better identify exploitable attack surfaces where adversaries are most likely to gain initial access or escalate privileges during compromise campaigns. This contextual risk analysis allows the CISO to justify remediation investments by correlating vulnerability exposure with asset criticality classifications, demonstrating that selected findings threaten business-essential systems supporting revenue generation, regulatory compliance, or operational continuity.
Tenable Vulnerability Management helps organizations maintain asset lifecycle management by maintaining accurate inventories as infrastructure evolves through acquisition, deployment, reconfiguration, and decommissioning phases. Organizations see everything by maintaining comprehensive asset inventories spanning assessed and discovered assets alike. The predictive capabilities that surface through Vulnerability Priority Rating (VPR) integration and exploitability indicators that forecast the findings adversaries weaponize. Security teams act with confidence by leveraging credentialed scans, exposure management and focusing on actionable remediation tasks on genuine threats. This report embodies exposure management principles by providing unified visibility across asset discovery, scan health diagnostics, and vulnerability detection that collectively answer strategic questions about risk posture and tactical questions about remediation execution priorities.
Additional Chapters
- Scan Authentication Summary: This chapter provides a summary of scan health in relation to authentication success and failures. System and network devices must be routinely scanned to ensure they are operating in compliance with organizational and regulatory requirements for vulnerability and configuration management.
- Scan Health: Risk managers utilize this chapter to evaluate credentialed scanning program health across authentication success rates, privilege sufficiency, and credential configuration quality metrics that directly impact vulnerability detection completeness and remediation prioritization confidence.
- Asset Discovery Statistics: Risk managers utilize this chapter to evaluate asset discovery program effectiveness by analyzing detected assets across the organization. The chapter segments analysis into three distinct sections examining licensed asset populations observed within specific timeframes, discovered asset assessment status, and scan frequency patterns that reveal coverage consistency.
- Summarize Local Checks Status: Organizations validating scan quality leverage local checks status to distinguish between systems receiving comprehensive credentialed vulnerability assessments versus those limited to network-based scanning that misses installed software vulnerabilities and missing patches. The chapter filters on specific diagnostic plugin identifiers reporting local checks availability including authentication failures, privilege escalation requirements, unsupported platform scenarios, and successful patch assessment executions.
- Assets with Tenable Applications Installed: Risk managers utilize this chapter to maintain inventory visibility into Tenable applications deployed across network, ensuring that vulnerability management tooling remains current with vendor-released security updates and operational improvements.
- Tenable Application Vulnerabilities: Security operations teams utilize this chapter to identify vulnerabilities affecting Tenable platform components themselves, ensuring that vulnerability management infrastructure maintains current security patch levels and avoids scenarios where scanning systems introduce exploitable weaknesses into monitored environments.
- Discovered Assets Seen in Last 30 Days: The operations team utilize this chapter to identify newly discovered assets requiring integration into the vulnerability assessment processes, distinguishing systems with basic network-level detection from those receiving full credentialed scans with local security checks.
- Host Discovery Scan Plugin Results: Risk managers utilize this chapter to evaluate host discovery scanning program effectiveness by analyzing network-level detection capabilities that identify assets without consuming Tenable Vulnerability Management license.
- Assets with Local Check Scan Results in Last 30 days: This chapter provides a summary of assets that have been scanned using valid elevated credentials or by a Tenable Agent during the last 30 days. These systems have been assessed using the most thorough means possible, and if supported have completed a missing patch assessment. Running scans that utilize Local Checks are essential in fully assessing assets for risk and enumerating the installed OS, applications, running services and patching. The requirements for this chapter are: TenableVulnerability Management (Nessus, Tenable Agent).
- Assets Seen in Last 30 Days with No Local Check Scan Result: This chapter provides details about assets that have been active in the network, and have been scanned in the last 30 days. However, the assets displayed have not been scanned using elevated credentials that enable local checks or by a Tenable Agent (for Windows, Linux and Mac OS assets) in the last 30 days. Running scans that utilize Local Checks are essential in fully assessing assets for risk and enumerating the installed OS, applications, running services and patching.
- Uncredentialed Licensed Scan Results in Last 30 days: This chapter provides details about assets that have been scanned during the last 30 days in which the asset was considered licensed and counted towards Tenable's license limit. A licensed scan uses non-discovery plugins and can identify vulnerabilities more accurately.
- Assets Seen in Last 30 Days with No Licensed Scan Result: This chapter provides details about assets that have been present on the network during the last 30 days, but have not been scanned in a manner that consumes a license. A Licensed Scan is anything beyond a basic Host Discovery Scan (such as a non-Credentialed subnet scan or a Local Check scan with Credentials or the Tenable Agent).
- Assets with Tenable Agent and an Agent Scan Result in the Last 30 Days: The assets in this chapter are identified as having been scanned during the last 30 days with Tenable Agent, which ensures the system is properly assessed to perform all local checks. Tenable Agent scans use lightweight, low-footprint programs that are installed locally on the asset. Tenable Agents collect vulnerability, compliance, and system data, and report that information back to Tenable Vulnerability Management for analysis.
- Assets with Tenable Agent but no Agent Scan within Last 60 Days: The assets in this chapter are identified as having been scanned during the last 60 days with Tenable Agents, which ensures the system is properly assessed to perform all local checks. However the Tenable Agent of the assets has not reported into Tenable Vulnerability Management in the last 30 days.
- Current Upstream Scanning Problems: Security operations teams utilize this chapter to diagnose upstream scanning problems affecting credentialed assessment quality, identifying specific plugin findings that indicate authentication failures, insufficient privileges, or protocol issues preventing successful vulnerability detection. The chapter filters on informational plugins reporting scanning diagnostic conditions rather than actual vulnerabilities, focusing analysis on technical issues that compromise assessment completeness rather than security exposures requiring remediation.
- Scan Information Results: Security operations teams utilize this chapter to analyze scan information plugin results that provide diagnostic insights into assessment methodologies, WMI enumeration capabilities, and system information gathering processes executed during vulnerability scans.
- Patching and Troubleshooting Findings: Security operations teams utilize this chapter to identify informational plugin findings that provide diagnostic insights into patching workflows and system configuration issues affecting update deployment success rates.
- Discovered Vendor Agents and Clients: Security operations teams utilize this chapter to inventory vendor agents and client software deployed across infrastructure, identifying endpoint security tools, management agents, and monitoring software that introduce additional attack surfaces requiring patch management attention.
- Top Exploitable Ports: The Vulnerabilities by Ports chapter displays vulnerabilities counts by TCP Port. The first widget, Vulnerability Counts by Port and Severity, is a stacked bar chart displaying these vulnerabilities by port and severity. The count of low to critical vulnerabilities is shown, along with the combined total of these vulnerabilities for each identified port on the bar.
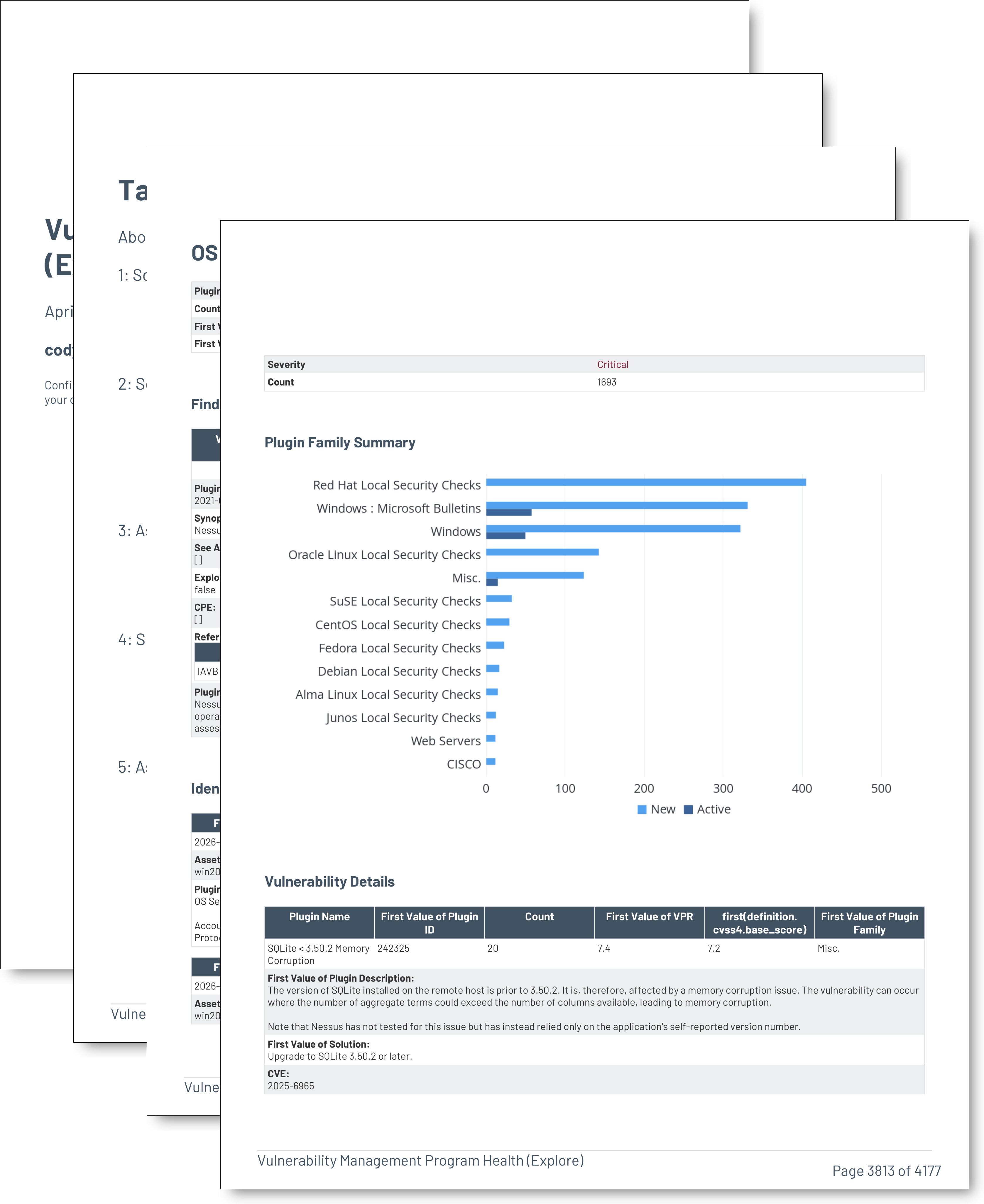
- Vulnerability Summary by Severity: Risk managers utilize this chapter to understand vulnerability distribution across severity classifications, enabling resource allocation decisions that match remediation capacity to exposure density within each risk tier.
- Assets That Have Not Been Seen for More than 180 Days: Risk managers utilize this chapter to identify stale asset data representing systems absent from scan results for extended periods, distinguishing decommissioned infrastructure consuming licensing capacity from active assets experiencing scanning coverage gaps.
- Assets That Have Not been Seen For More Than 365 days: Risk managers utilize this chapter to identify stale asset data representing systems absent from scan results for extended periods, distinguishing decommissioned infrastructure consuming licensing capacity from active assets experiencing scanning coverage gaps.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success