Organizations frequently struggle to maintain comprehensive visibility into database attack surfaces. The complex interplay between database vulnerabilities, supply chain risks, and configuration compliance often keep the IT operations team competing against priorities of the database administrators. The Risk Manager needs to balance the operational priorities with new threats from exploitable vulnerabilities and system hardening recommendations. By creating a comprehensive view of the threat landscape of databases and their related applications, Tenable Vulnerability Management (TVM) is able to provide executive-level metrics demonstrating program effectiveness and identifying resource allocation priorities, along with actionable tasks for database-related findings. This report provides a consolidated view of database security intelligence in three areas: database specific vulnerabilities, database supply chains specialized, and configuration audit for databases.
The Risk Manager uses this report to present consolidated database security metrics to leadership, demonstrating the Organization's patching effectiveness through patched versus unpatched vulnerability counts, identifying supply chain exposure through database driver and related software vulnerabilities, and proving configuration compliance against industry benchmarks. The operational chapters within the report, guide the Security Operations Team to establish baseline database asset inventory, prioritize migration planning for unsupported end-of-life database versions, and focus remediation efforts on exploitable vulnerabilities requiring immediate attention.
When viewing the database vulnerability findings, taking into account the age of exploitable vulnerabilities, provides the Risk Manager with critical intelligence to initiate difficult conversations with leadership about systemic remediation barriers and organizational friction preventing timely patching. This analysis reveals root causes such as application compatibility constraints, inadequate maintenance windows, or insufficient coordination between database administration and application development teams. Armed with this data, the Risk Manager can justify budget requests for additional resources, advocate for process improvements, or propose alternative security controls when traditional patching approaches prove insufficient.
Configuration compliance metrics ensure the Security Operations Team's vulnerability remediation efforts are complemented by proper security hardening, recognizing that unpatched vulnerabilities represent only part of the risk equation when fundamental security controls remain disabled or misconfigured. Granular control-level findings hold the Security Operations Team accountable for systematic configuration hardening against industry standards. During audit discussions, these compliance metrics demonstrate the Organization's security posture maturity and measure configuration management program effectiveness.
Asset-centric risk analysis directs the Organization's finite remediation resources toward database servers exhibiting the highest concentration of exploitable vulnerabilities, ensuring maximum risk reduction from limited security budgets. By combining exploitability status with Asset Criticality Rating, high-value database servers supporting the Organization's critical business functions receive prioritized security attention. Coordinated remediation campaigns planned with the Security Operations Team address multiple vulnerabilities per maintenance window, maximizing security improvement while minimizing operational disruption to the Organization's production database services.
Through Tenable's exposure management approach, the Risk Manager transforms traditional vulnerability assessment by moving beyond identifying the software assets to understanding the risk the findings mean for the Organization's strategic objectives. This database security intelligence unifies vision by consolidating visibility across the entire attack surface, exposing gaps that leave the Organization vulnerable to database-specific attacks impacting revenue-generating systems. The analysis unifies insight by examining vulnerability, supply chain, and configuration risks as interconnected threats, connecting disparate data points to identify true exposures threatening the Organization's business value and competitive position. The Risk Manager unifies action by mobilizing executive leadership and security teams to prioritize remediation based on actual business impact rather than relying on generic CVSS scores alone. By integrating machine learning predictions of exploit likelihood with Asset Criticality Ratings, the Risk Manager advances the Organization from reactive database patching to proactive risk reduction aligned with business strategy. This comprehensive approach protects the Organization's business value, market reputation, and customer trust by ensuring finite security investments address database exposures with the highest likelihood of attack and the greatest potential business impact.
Chapters
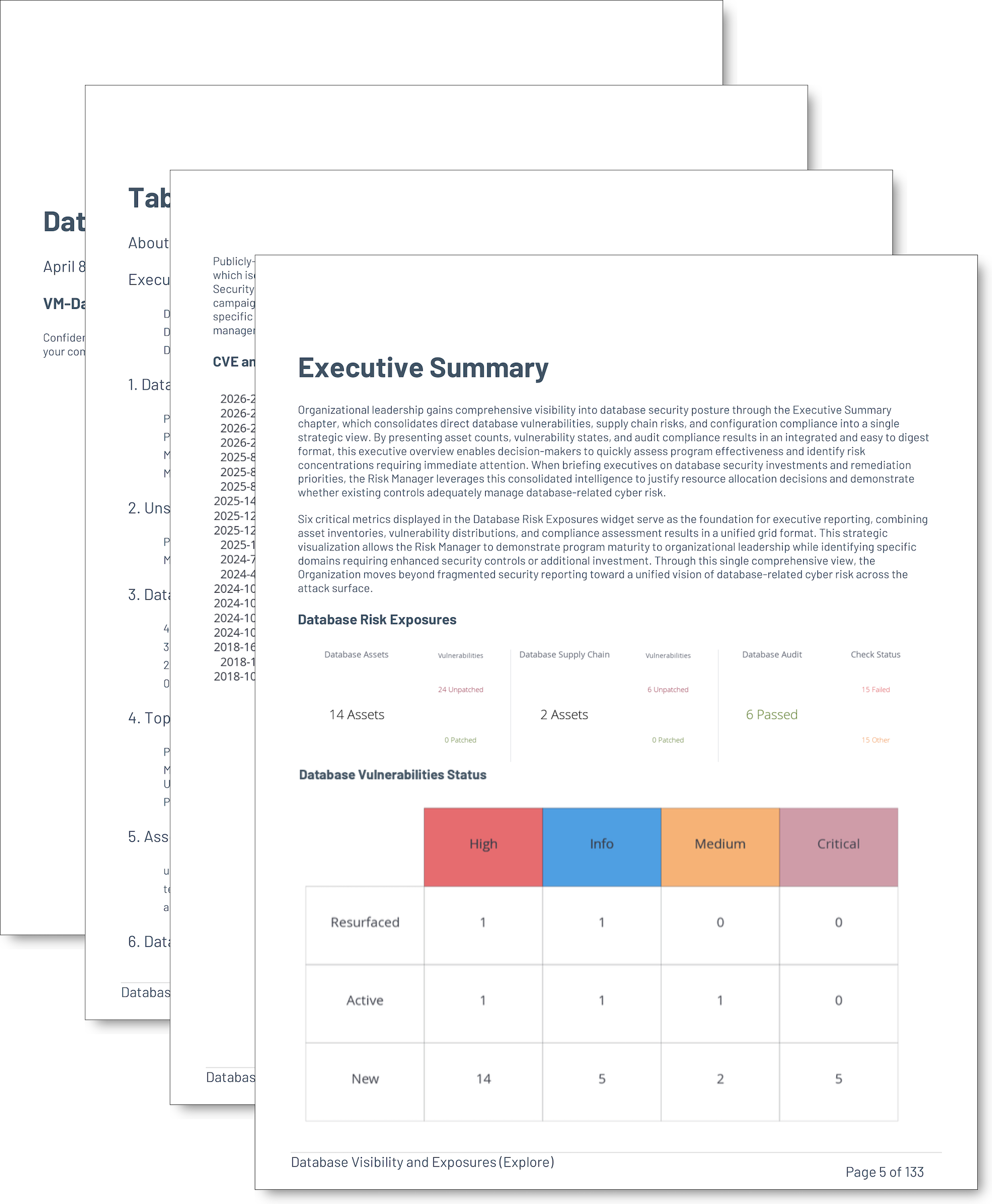
Executive Summary: This chapter provides organizational leadership with comprehensive visibility into database security posture, by consolidating direct database vulnerabilities, supply chain risks, and configuration compliance into a single strategic view. By presenting asset counts, vulnerability states, and audit compliance results in an integrated and easy to digest format, this executive overview enables decision-makers to quickly assess program effectiveness and identify risk concentrations requiring immediate attention.
Database Application Installations: Database discovery intelligence empowers the Risk Manager to establish comprehensive baseline inventory revealing platform distribution, instance quantities, and network deployment locations across the Organization's technology infrastructure. When presenting security program effectiveness to organizational leadership, the Risk Manager leverages detection plugin findings to justify investments in license management, technology standardization initiatives, and vulnerability management coverage expansion.
Unsupported Installed Database Applications: End-of-life database installations demand immediate executive attention when the Risk Manager presents vulnerability exposure intelligence to organizational leadership, as unsupported software lacks vendor security patches and creates unremediable vulnerability accumulation over time. By leveraging filtering in the plugin names, the Risk Manager quantifies the scope of end-of-life database installations requiring migration investments. When briefing executives on compliance posture, the Risk Manager emphasizes how running unsupported database software creates regulatory framework violations that expose the Organization to audit findings, financial penalties, and reputational damage across customer-facing business operations.
Database Findings Count by Severity: Severity-based vulnerability distribution provides the Risk Manager with essential metrics when communicating database security posture to organizational leadership, audit committees, and regulatory stakeholders. By grouping active database findings according to CVSS severity classifications, the Risk Manager establishes baseline measurements for vulnerability management program maturity assessments and tracks progress over time. When presenting executive briefings, the Risk Manager emphasizes that severity ratings inform risk conversations without dictating prioritization decisions, ensuring leadership understands comprehensive vulnerability distribution patterns across Critical, High, Medium, Low, and Informational severity levels for complete transparency during board presentations.
Top Exploitable Database Exposures: Immediate threat assessment empowers the Risk Manager to answer the critical executive question: which database vulnerabilities could threat actors exploit during a coordinated campaign against the Organization's infrastructure using currently available attack tools. By applying exploitability filtering to reveal all current database vulnerabilities with accessible public exploitation techniques, the Risk Manager presents organizational leadership with the complete exploitable attack surface requiring urgent security investment. When briefing executives on cyber risk posture, the Risk Manager emphasizes how this comprehensive exploitability view differs from aged vulnerability analysis, ensuring decision-makers understand the full scope of vulnerabilities where working exploit code exists and remains accessible to adversaries targeting revenue-generating database systems.
Assets with the Most Exploitable Database Vulnerabilities: Asset-centric risk assessment enables the Risk Manager to direct finite remediation resources toward database servers exhibiting the highest concentration of exploitable vulnerabilities rather than dispersing effort across individual vulnerability types. By combining exploitability filtering with Asset Criticality Rating, the Risk Manager presents organizational leadership with risk-ranked target lists prioritizing high-value database servers supporting critical business functions. When justifying security investments to executives, the Risk Manager is able to clearly demonstrate how a production financial database server with three exploitable vulnerabilities demands more urgent attention than a development database server with a single exploitable finding, ensuring remediation budgets align with actual business risk exposure.
Database Vulnerabilities First Seen More Than 365 Days: Security debt from exploitable database vulnerabilities persisting beyond one year signals systemic challenges in the Organization's vulnerability management lifecycle that demand executive attention. When the Risk Manager presents these aged exploitable findings to organizational leadership, the analysis reveals resource constraints, patch scheduling conflicts, and application compatibility concerns preventing timely remediation of database vulnerabilities protecting the Organization's most sensitive data assets.
Other Useful Database Findings: This chapter captures database-related security issues that fall outside the standard database plugin family classification, using negative filtering combined with keyword matching to identify relevant findings. The chapter reveals issues such as database credential scan failures, database client vulnerabilities, connectivity problems, and vulnerabilities in database-related software. Database credential scan failures prove particularly significant because authentication failures prevent vulnerability scanners from performing deeper security assessments, leaving potential vulnerabilities undiscovered and creating blind spots in security visibility.
Audit Benchmarks Collected using Database Checks: Configuration compliance intelligence enables the Compliance Manager to demonstrate the Organization's adherence to industry benchmarks when presenting security posture to audit committees and regulatory stakeholders. By analyzing specialized audit plugin results assessing database systems against standards covering authentication mechanisms, encryption settings, logging configurations, and access controls, the Compliance Manager quantifies how many controls pass versus fail for each benchmark. When briefing organizational leadership, the Compliance Manager emphasizes how configuration auditing verifies that available security controls are properly enabled according to vendor and industry guidance, complementing vulnerability scanning to provide comprehensive database security assessment beyond software flaw identification.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success