Tenable One
Attack Surface Management
Get comprehensive visibility into your internet-connected assets, services, and applications to better assess and manage cyber risk.
Easily understand and manage your external risks
Transform vulnerability data into meaningful insights
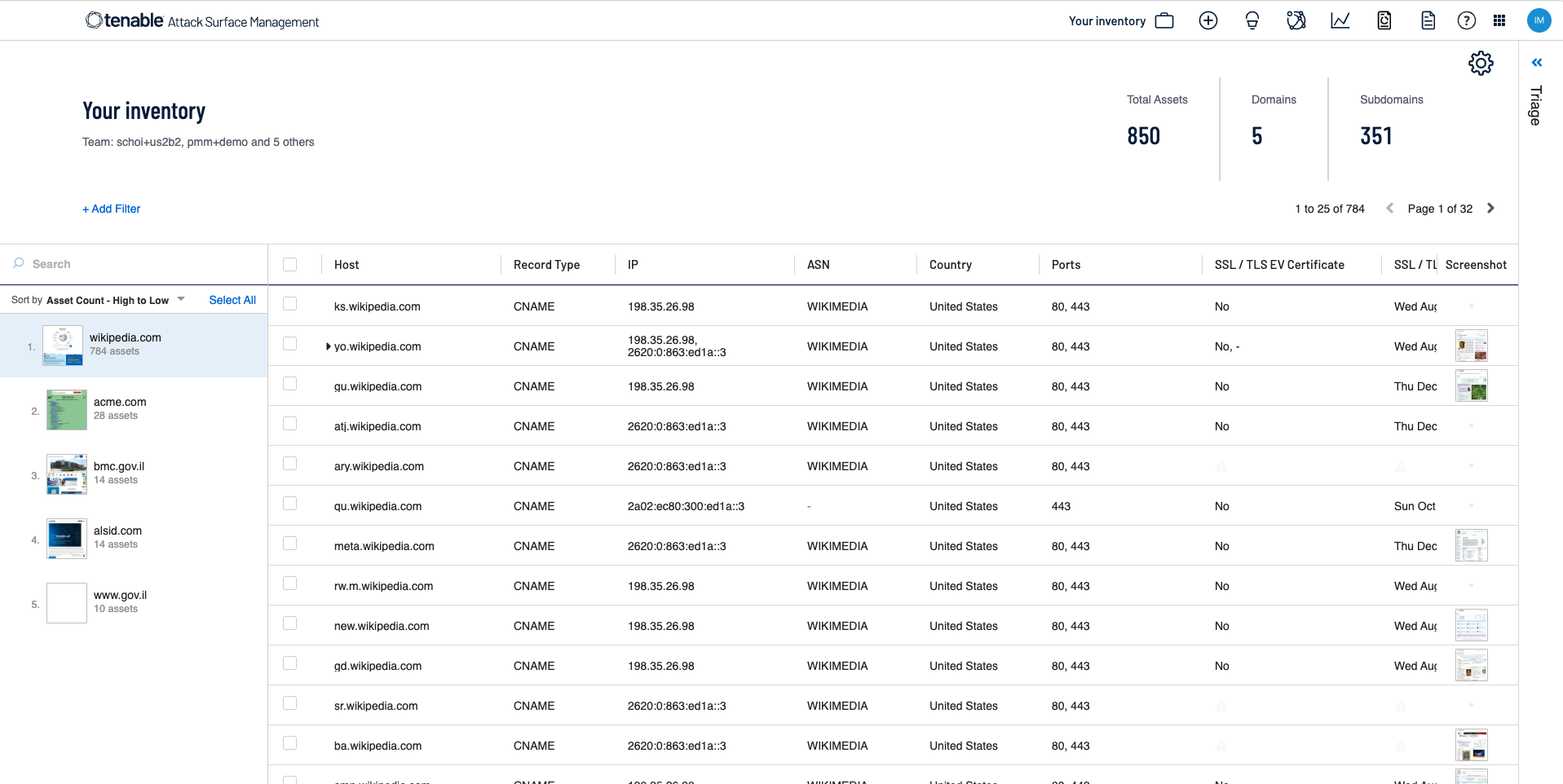
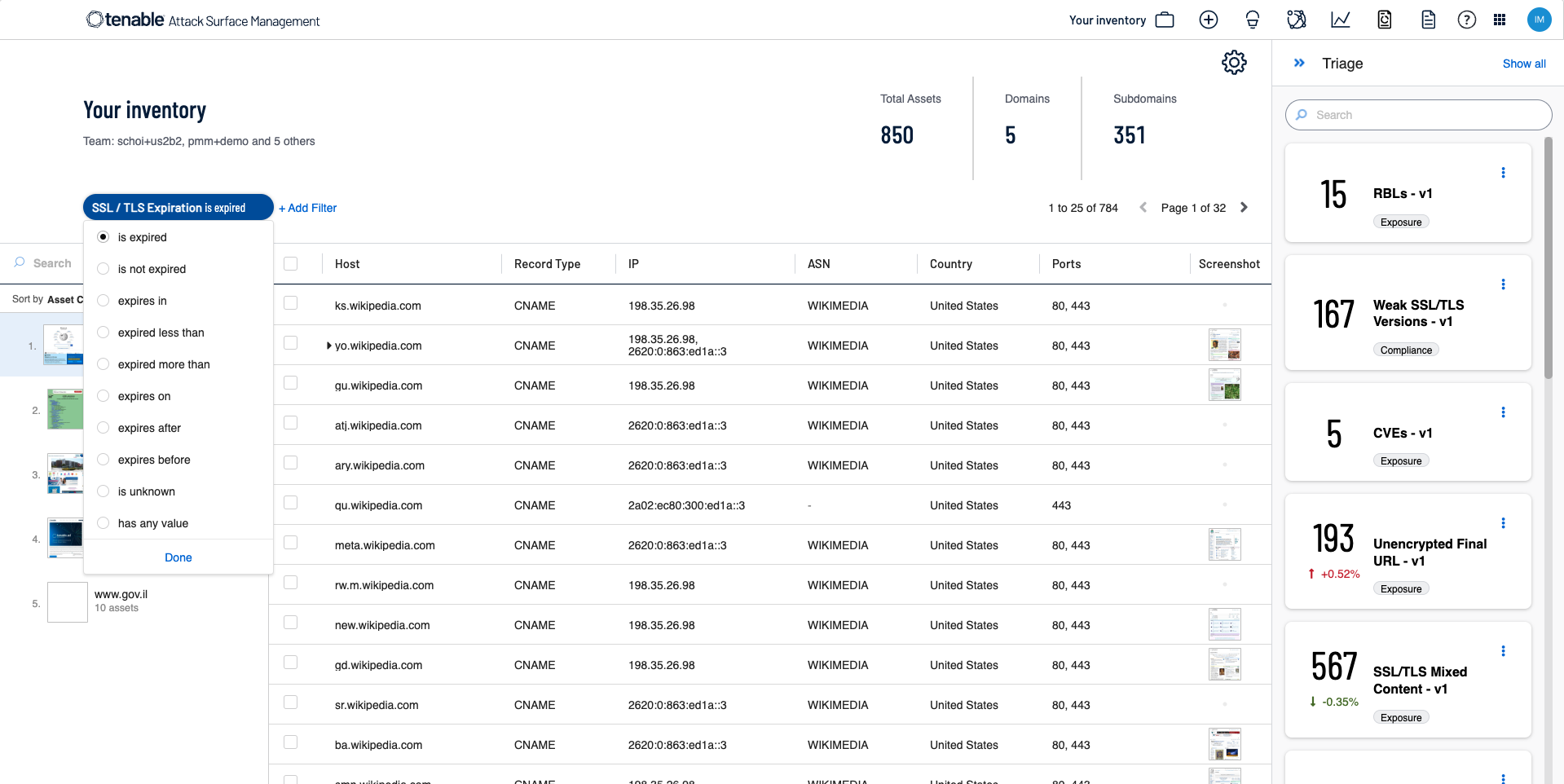
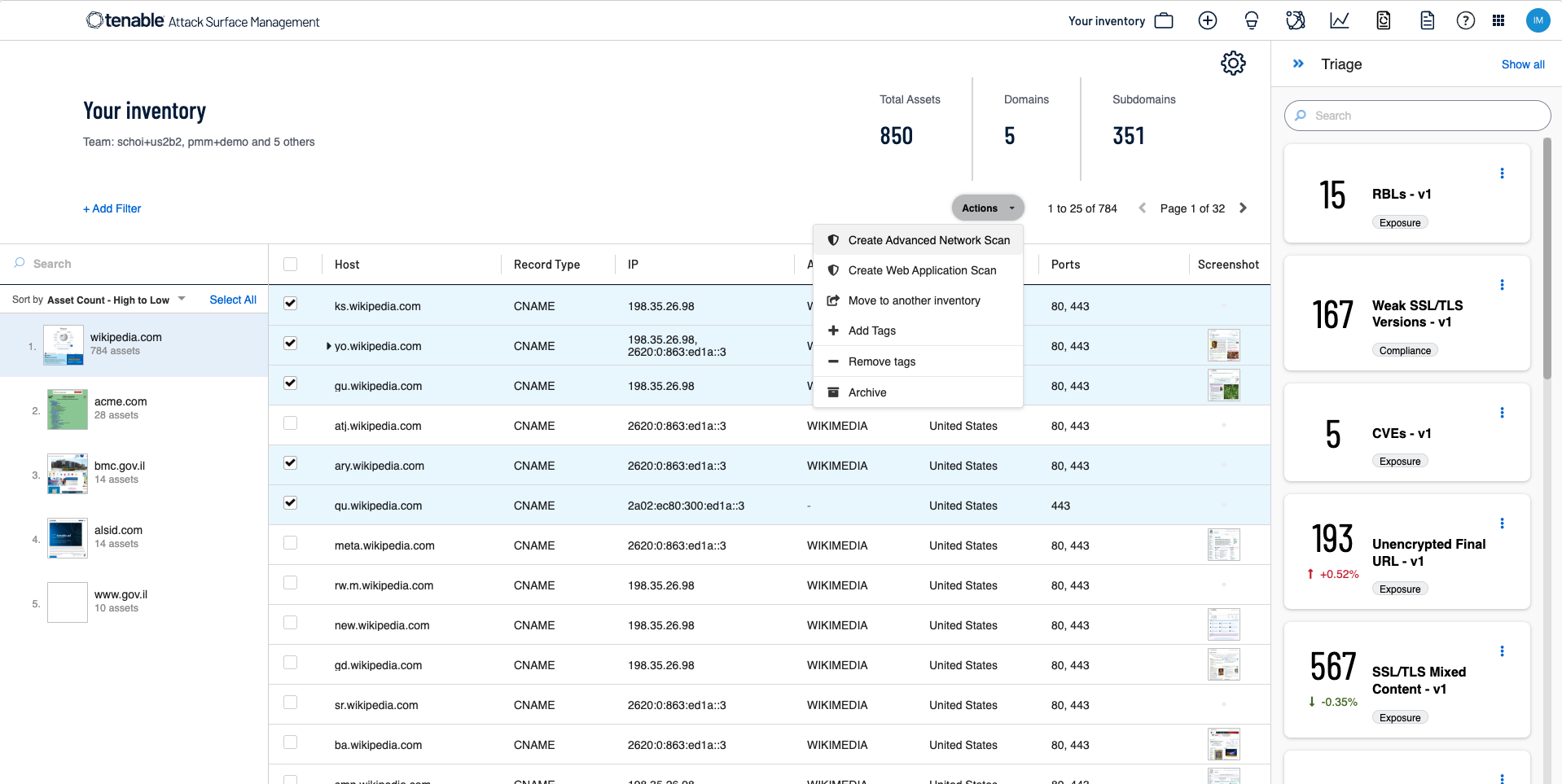
Use Tenable One Attack Surface Management to continuously map the entire internet and get comprehensive visibility into your internet-facing assets, even those you don’t know about. Discover and manage external attack surfaces for a complete picture of your exposures.
External attack surface management for:

tenable one
The world’s only AI-powered exposure management platform
Tenable One reduces cyber risk by unifying security visibility, insight and action across the entire attack surface, helping organizations quickly find and fix critical weaknesses.
See why customers choose Tenable One Attack Surface Management
In an era of constant cyber threats, Tenable One Attack Surface Management is an extra set of eyes, proactively shining a light on unknown assets and helping organizations stay ahead of potential attacks.
FAQs
-
What is Tenable One Attack Surface Management?
-
Tenable One Attack Surface Management is an external attack surface management (EASM) solution that identifies which assets and services your organization has residing on the internet that threat actors could externally access. Once those assets and services are properly attributed to your organization, Tenable One Attack Surface Management performs a number of different actions to provide context around security posture.
-
What challenges does Tenable One Attack Surface Management solve?
-
The problem for most organizations is they are largely blind to the full and ever-changing scope of internet-facing assets and services. Tenable One Attack Surface Management eliminates this problem by continuously monitoring the internet and attributing assets and services to your organization. It helps you rapidly discover and identify all externally facing assets that could become exploitable targets for cyber criminals and eliminates blind spots in your organization’s attack surface.
-
What is the benefit of Tenable One Attack Surface Management?
-
Discovering the vast majority of your internet-accessible assets is a foundation for good security. Tenable One Attack Surface Management allows you to discover and assess these assets your organization didn’t know about, so you have visibility into your external risk.
-
What is the difference between cyber asset management tools (CSAM, CAASM) and Tenable One Attack Surface Management?
-
While cyber asset management tools provide a centralized inventory of assets to help improve investigations and analysis, Tenable One Attack Surface Management helps you understand your external-facing attack surface where threat actors seek to gain an entry point into your organization. This helps you remove important blind spots to discover internet-accessible assets you didn’t know existed and also provide important asset criticality context to inform exposure prioritization. Tenable One also provides built-in cyber asset management capabilities to alleviate the need for a separate tool to deploy.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success