Putting the S.M.A.R.T. in Smart Cities: How to Address the Expanding Attack Surface

The concept of a smart city came of age in conjunction with another now ubiquitous term: digital transformation. Cities and counties rely heavily on their taxing authority to provide critical services such as public safety, public works and infrastructure maintenance. By using the latest IP-enabled technology, local jurisdictions, or smart cities, can improve the efficiency of service delivery, freeing up revenues to support additional – or enhanced – services to their residents.
Smart cities: New opportunities for service delivery, new vectors for risk
As great as this concept sounds, it’s already experienced some headwind as various initiatives get closer to being operational, with none more significant than the maintenance of cyber hygiene and integrity of information security.
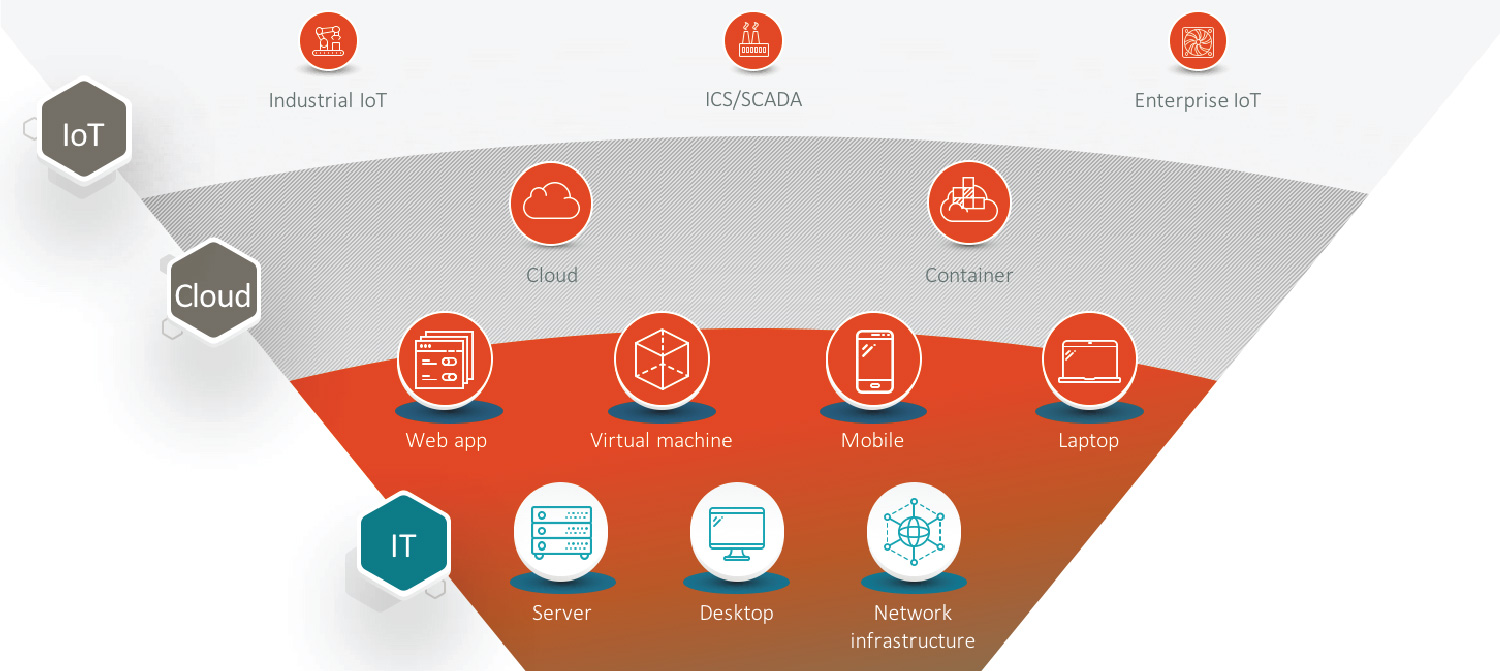
Smart cities have fundamentally outkicked their coverage on information security as they’ve adopted their digital transformation plans. Digitizing local services has expanded the attack surface, potentially creating greater liability than the benefits offered from their adoption. IT departments are focused on maintaining uptime for users as well as gathering and analyzing the data that drives effective provisioning of services. Digital transformation of smart cities will spread the local IT shops very thin by adding new projects that must be completed concurrent to the smart city initiatives. The adoption of cloud computing strategies and the integration of large numbers of IoT devices are among the list of projects they’ll need to tackle.
Many cities are moving to cloud computing to deal more efficiently with the deluge of data necessary to manage smart city initiatives. This will expand the cyber attack surface beyond the the usual confines of the local IT world. Adding smart devices such as refuse containers, streetlights and parking meters will add a plethora of new IoT integration challenges. Finally, municipally owned utilities will create an integration of IT and operational technology (OT) that may be well beyond IT’s current capabilities.
So, is this expanding attack surface a mystery to local IT departments? Nope, and it’s not a mystery to the black-hat hackers who want to disrupt local services and perhaps siphon off the benefits of these services undetected. Say a city-owned utility utilizes a number of IoT devices to manage the distribution of power or water to local residents. Being able to manipulate those IoT devices to provide more or less of those services to certain residents could be of tremendous financial value to a threat actor. And the truth is, this activity could go undetected for an extended period of time without the introduction of an enhanced – and coordinated – Cyber Exposure capability.
How can smart cities address the expanding attack surface?
Smart cities can ensure they’re addressing this expanded cyber attack surface by creating a set of S.M.A.R.T. information security goals to go along with their digital transformation goals:
Specific – Ensure each smart city digital transformation initiative has a specific Cyber Exposure corollary. For example, if introducing digital waste disposal systems is a smart city goal, ensure both the IoT devices and software that manages them are actively and passively scanned, as appropriate. In other words, don’t “outkick the coverage” and implement an initiative without addressing the potential vulnerabilities it may present.
Measurable – Information security standards apply to the expansion of smart city initiatives. Ensure a process is in place to automate the reporting of known vulnerabilities and their threat level. And make this information available to the executive suite via clear, concise dashboard reporting.
Attainable – Although smart city digital transformation has great promise, it also gives threat actors a wider set of potential targets. Cities and counties should be very deliberate about how they bring initiatives online, so the benefits are attainable without a corresponding increase in potential liabilities due to expanding the attack surface too quickly. The public will appreciate the benefit over time, but will damn the risks immediately if there’s a breach.
Reasonable – Not every city and county will have the time or resources to implement every single smart city initiative. It just won’t happen. The reasonable path is to ensure the risk of threats is never greater than the pace of implementation.
Time-Specific – In the digital age, a year is what five years used to be. Moore’s law is still in effect, and digital progress is not slowing down. However, local government remains first and foremost a provider of services at the most basic level: power, water, sanitation and transportation, to name a few. Those have not changed. The challenge is to ensure that digital transformation time frames don’t shift the focus from the provisioning of services to the completion of digital transformation. That would be exactly what the threat actors want– and the resulting disruption could fracture the public trust for years.
- Government

