Getting Started with Nessus on Kali Linux
Kali Linux, a Linux distribution designed specifically for penetration testing, comes prepackaged with many pen test tools. Nessus® provides a penetration tester with a wealth of capabilities that will assist in the engagement, such as:
- Identifying local and remote vulnerabilities
- Configuration and compliance audits
- Checking for default credentials
- Web application scanning
Nessus isn’t installed on Kali Linux by default, but this post will show you how to install Nessus and provide some suggestions for using it in a penetration testing engagement to gain a more complete understanding of your organization's security posture.
Please Note: Because the Kali Linux installation of Nessus has been very popular over the past several years, the instructions in this blog were updated by Juan Vela on May 13, 2019, to reflect the latest version of Nessus. If you are interested in learning how to install Nessus version 5 on Kali Linux, please read our 2014 blog, Installing and Using Nessus on Kali Linux.
Installing and configuring Nessus
Prior to downloading Nessus, ensure that your Kali Linux installation is up to date:
apt update && apt upgradeStep 1: Purchase Nessus and obtain an Activation Code
Nessus can be purchased directly from Tenable or through an authorized reseller.
After purchasing Nessus, an Activation Code will be available on the Tenable Support Portal.
Step 2: Download Nessus
Navigate to the Tenable Nessus downloads page and select the appropriate version for your installation of Kali Linux, either the 32-bit or 64-bit Debian package.
Step 3: Install Nessus
Using the command line, install the Nessus package. Once the installation completes, start the Nessus service:
/etc/init.d/nessusd startIf you would like Nessus to start when Kali Linux boots, issue the command:
update-rc.d nessusd enableAfter the Nessus service starts, use a web browser to navigate to the Nessus Web Interface at: https://localhost:8834/.
Step 4: Configure and use Nessus
You may see a warning about the SSL certificate not being configured appropriately. You can continue past this warning or consult the Nessus User Guide to properly set this up.
To configure Nessus, follow the installation wizard. Create an administrator user account, activate with your activation code from the Tenable Support Portal and let Nessus fetch and process the plugins.
Refer to the official Nessus documentation for any other questions or issues with installing Nessus.
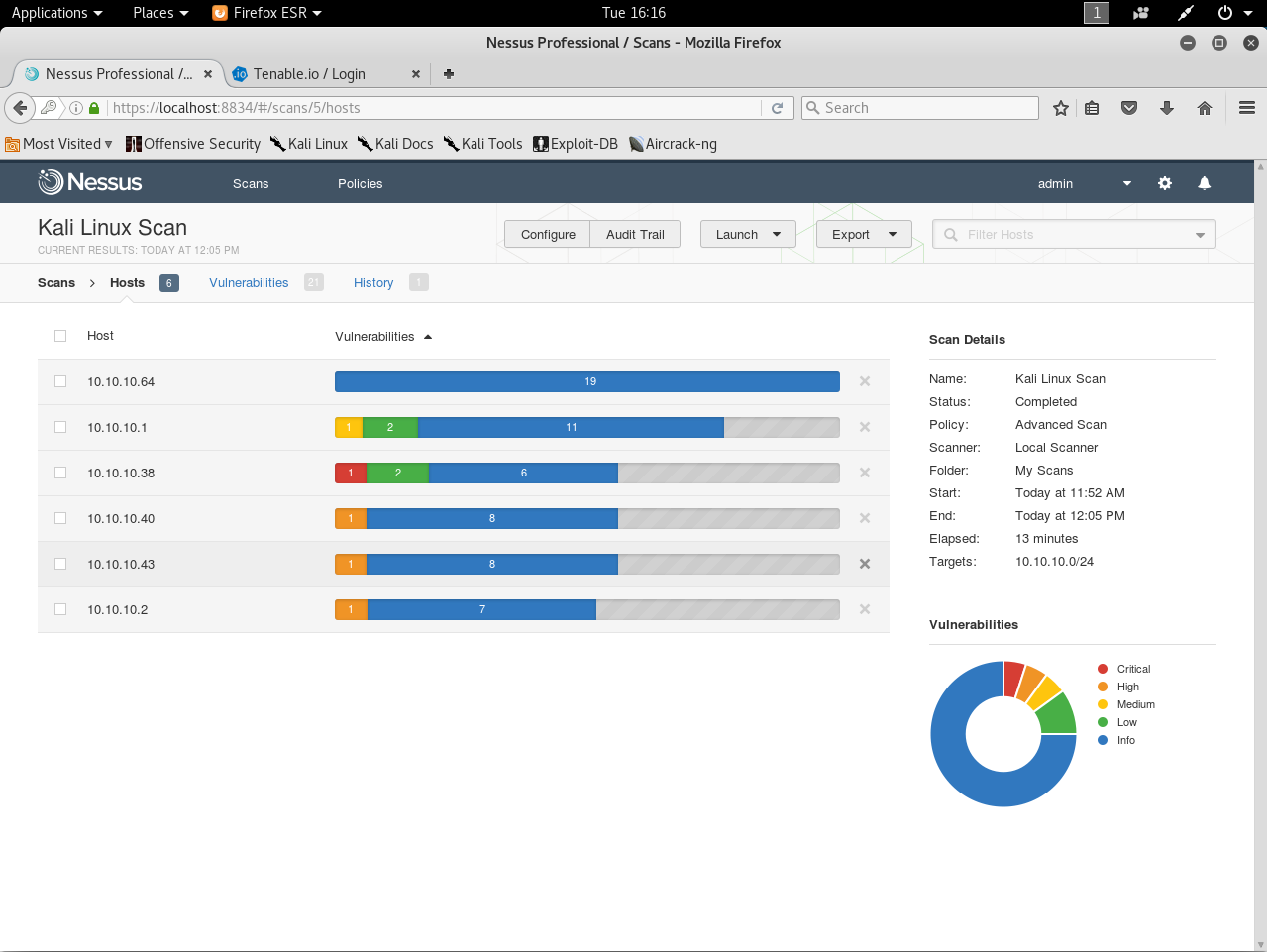
Using Nessus in a penetration test
Kali Linux tools complement your Nessus installation, with everything in one place for easy maintenance. Nessus reports on host discovery, vulnerability detection and exploitability. Here are some of the ways Nessus can be used to support penetration testing:
- Remediation prioritization and newsworthy vulnerabilities
- Finding Heartbleed, Shellshock or other newsworthy vulnerabilities may be important when assessing an organization’s security posture and reporting to the security leadership team.
- Detecting default credentials
- Use credentials harvested from other phases of testing to perform credentialed patch audits, local (client-side) application vulnerability scanning and discovery of interesting configurations on targets.
- Hunting for web shells
- A web server may already be compromised without the administrator even knowing about it. Nessus can help in the detection of compromised hosts.
- Modify a vulnerability’s severity
- Identify low-severity vulnerabilities and allow an admin-level user to re-cast them as critical vulnerabilities. Modifying the severity of a vulnerability empowers testers to raise the visibility of lower severity findings that often lead to serious exposures.
Conclusion
Nessus is the world’s most widely-deployed vulnerability assessment solution. Nessus quickly and accurately identifies vulnerabilities, configuration issues and malware in physical, virtual and cloud environments to help you prioritize what to fix first. Combine Nessus with Kali Linux to build a superior pen testing toolkit that provides deep insight into your network systems.
For more information
To download Nessus, visit the Nessus Download page or evaluate Nessus Professional for 7 days.
Learn more
- Nessus




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success