The Verizon Data Breach Investigation Report (DBIR), first published in 2008, is an annual publication that analyzes information security incidents from public and private organizations, with a focus on data breaches. Data breaches continue to have a major financial impact on organizations, as well as an impact on their reputations. Tenable Network Security offers dashboards and Assurance Report Cards (ARCs) that can assist organizations in meeting many of the recommendations and best practices in the DBIR. As in previous years, the 2016 DBIR notes that a vast majority of all attacks fall into a few basic patterns. Throughout this and past years’ reports, suggestions are given for monitoring the network for each of these patterns. This ARC can assist an organization in monitoring its network to reduce the successfulness of these attack patterns and to reduce its chances of a data breach.
The DBIR report specifically calls out vulnerabilities with corresponding CVE numbers that represent a large share of attack vectors used by attackers. Organizations may be focused on ensuring that vulnerabilities recently released are addressed, but may accept the risk of older vulnerabilities. Remediating vulnerabilities are important, but not all vulnerabilities present the same level of risk to the organization.
The report makes an important distinction that even though some of the CVEs listed in the report are from 1999, 2001 and 2002, they still represent an active threat to the organization. Remediating the latest Adobe Flash vulnerability with active zero-day exploitation is important, but so are older vulnerabilities many attackers have in their arsenal of attack tools. Attackers have different motivations, but some still focus on quick wins with reliable exploits of older vulnerabilities. As referenced in this report, analysts may not believe that a vulnerability from 2002 is a threat, but two vulnerabilities from that year are still actively exploited.
The complete top ten CVEs listed in the report are CVE-1999-1058, CVE-2001-0680, CVE-2001-0876, CVE-2002-0126, CVE-2002-0953, CVE-2003-0818, CVE-2011-0877, CVE-2012-1054, CVE-2015-0204 and CVE-2015-1637. Some organizations may not have these vulnerabilities in their organization due to the technologies exploited by the listed CVEs. Organizations should also be aware that while these CVEs made up 85% of the actively exploited vulnerabilities used to compromise organizations, 900 other vulnerabilities made up the remaining 15% of the exploitable vulnerabilities. Exploiting any common vulnerability could give an attacker access to account credentials that could then be used to further the attack to other systems on the network. Organizations who remain vigilant with continuous monitoring tools such as Tenable’s Tenable.sc can better protect themselves with up to date information. Some of these vulnerabilities may be present in the organization, but they should be mitigated as best as possible to help prevent exploitation. However, having visibility into the organization and being aware of the vulnerabilities present can help ensure that organizations can best protect themselves with appropriate responses.
Brief details of each CVE are listed below:
- CVE-1999-1058: Buffer overflow in Vermillion FTP Daemon VFTPD 1.23
- CVE-2001-0680: Directory traversal vulnerability in ftpd in QPC QVT/Net 4.0 and AVT/Term 5.0
- CVE-2001-0876: Buffer overflow in Universal Plug and Play (UPnP) on Windows 98, 98SE, ME, and XP
- CVE-2002-0126: Buffer overflow in BlackMoon FTP Server 1.0 through 1.5
- CVE-2002-0953: Arbitrary code execution with globals.php in PHP Address before 0.2f
- CVE-2003-0818: Multiple integer overflows in Microsoft ASN.1 library
- CVE-2011-0877: Unspecified vulnerability in multiple Oracle Database Server and Enterprise Manager Grid Control versions
- CVE-2012-1054: Local privilege escalation in multiple Puppet versions
- CVE-2015-0204: “FREAK” exploitation in multiple OpenSSL versions
- CVE-2015-1637: Schannel downgrade attack in multiple Microsoft Windows versions (“FREAK” exploitation)
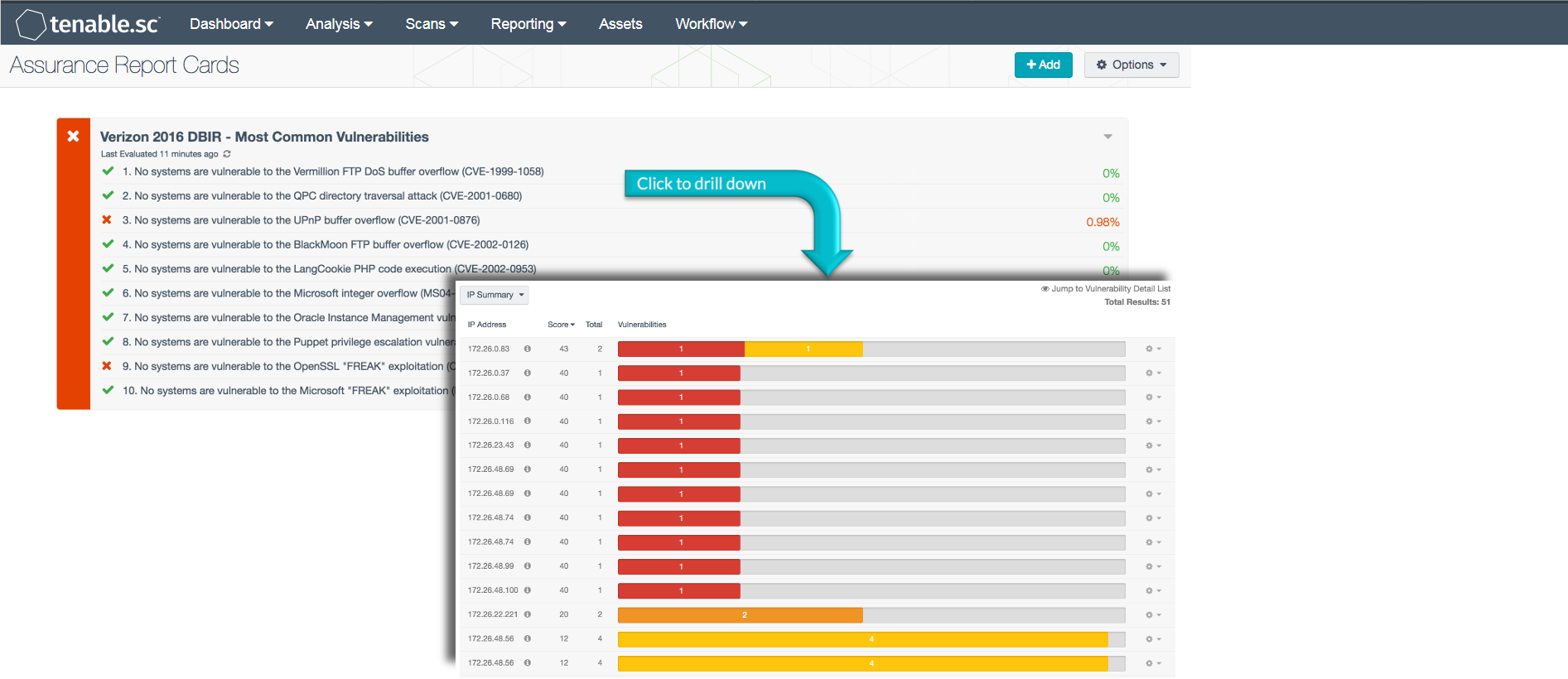
This ARC assists organizations in improving analyst awareness of higher priority vulnerabilities in the organization. Policy statements included within this ARC report on the top ten CVEs as reported by the Verizon DBIR. Organizations can use this ARC to measure their vulnerability patch process to evaluate their current policy to see if these CVEs are present. Having visibility of vulnerabilities allows organizations to proactively respond to threats, mitigate vulnerabilities, and take preventative measures before any serious damage occurs.
The information provided in this ARC provides a baseline to measure the effectiveness of an organization's information security policies and whether the current policies being enforced are effective. The ARC policy statement parameters are guides that can be customized as necessary to meet organizational requirements.
This ARC is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The ARC can be easily located in the Tenable.sc Feed under the category Security Industry Trends. The ARC requirements are:
- Tenable.sc 5.3.1
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.0
Tenable.sc provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable.sc is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. By integrating with Nessus, Tenable.sc’s continuous network monitoring is able to track vulnerabilities and mitigations across the enterprise.
The following policy statements are included in this ARC:
No systems are vulnerable to the Vermillion FTP DoS buffer overflow (CVE-1999-1058): This policy statement displays the ratio of systems with the CVE-1999-1058 vulnerability to all systems in the organization. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This CVE vulnerability was specifically called out as a top 10 vulnerability in the Verizon DBIR 2016 report. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have the CVE-1999-1058 vulnerability. Unpatched vulnerabilities, especially those which are highly exploitable, should be remediated quickly to improve security.
No systems are vulnerable to the QPC directory traversal attack (CVE-2001-0680): This policy statement displays the ratio of systems with the CVE-2001-0680 vulnerability to all systems in the organization. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This CVE vulnerability was specifically called out as a top 10 vulnerability in the Verizon DBIR 2016 report. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have the CVE-2001-0680 vulnerability. Unpatched vulnerabilities, especially those which are highly exploitable, should be remediated quickly to improve security.
No systems are vulnerable to the UPnP buffer overflow (CVE-2001-0876): This policy statement displays the ratio of systems with the CVE-2001-0876 vulnerability to all systems in the organization. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This CVE vulnerability was specifically called out as a top 10 vulnerability in the Verizon DBIR 2016 report. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have the CVE-2001-0876 vulnerability. Unpatched vulnerabilities, especially those which are highly exploitable, should be remediated quickly to improve security.
No systems are vulnerable to the Blackmoon FTP buffer overflow (CVE-2002-0126): This policy statement displays the ratio of systems with the CVE-2002-0126 vulnerability to all systems in the organization. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This CVE vulnerability was specifically called out as a top 10 vulnerability in the Verizon DBIR 2016 report. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have the CVE-2002-0126 vulnerability. Unpatched vulnerabilities, especially those which are highly exploitable, should be remediated quickly to improve security.
No systems are vulnerable to the LangCookie PHP code execution (CVE-2002-0953): This policy statement displays the ratio of systems with the CVE-2002-0953 vulnerability to all systems in the organization. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This CVE vulnerability was specifically called out as a top 10 vulnerability in the Verizon DBIR 2016 report. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have the CVE-2002-0953 vulnerability. Unpatched vulnerabilities, especially those which are highly exploitable, should be remediated quickly to improve security.
No systems are vulnerable to the Microsoft integer overflow (CVE-2003-0818): This policy statement displays the ratio of systems with the CVE-2003-0818 vulnerability to all systems in the organization. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This CVE vulnerability was specifically called out as a top 10 vulnerability in the Verizon DBIR 2016 report. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have the CVE-2003-0818 vulnerability. Unpatched vulnerabilities, especially those which are highly exploitable, should be remediated quickly to improve security.
No systems are vulnerable to the Oracle Instance Management vulnerability (CVE-2011-0877): This policy statement displays the ratio of systems with the CVE-2011-0877 vulnerability to all systems in the organization. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This CVE vulnerability was specifically called out as a top 10 vulnerability in the Verizon DBIR 2016 report. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have the CVE-2011-0877 vulnerability. Unpatched vulnerabilities, especially those which are highly exploitable, should be remediated quickly to improve security.
No systems are vulnerable to the Puppet privilege escalation vulnerability (CVE-2012-1054): This policy statement displays the ratio of systems with the CVE-2012-1054 vulnerability to all systems in the organization. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This CVE vulnerability was specifically called out as a top 10 vulnerability in the Verizon DBIR 2016 report. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have the CVE-2012-1054 vulnerability. Unpatched vulnerabilities, especially those which are highly exploitable, should be remediated quickly to improve security.
No systems are vulnerable to the OpenSSL “FREAK” exploitation (CVE-2015-0204): This policy statement displays the ratio of systems with the CVE-2015-0204 vulnerability to all systems in the organization. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This CVE vulnerability was specifically called out as a top 10 vulnerability in the Verizon DBIR 2016 report. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have the CVE-2015-0204 vulnerability. Unpatched vulnerabilities, especially those which are highly exploitable, should be remediated quickly to improve security.
No systems are vulnerable to the Microsoft “FREAK” exploitation (CVE-2015-1637): This policy statement displays the ratio of systems with the CVE-2015-1637 vulnerability to all systems in the organization. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This CVE vulnerability was specifically called out as a top 10 vulnerability in the Verizon DBIR 2016 report. Vulnerabilities that remained unpatched for extended periods of time can lead to system compromise or exploitation. This policy statement will help to identify systems that have the CVE-2015-1637 vulnerability. Unpatched vulnerabilities, especially those which are highly exploitable, should be remediated quickly to improve security.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success