The Payment Card Industry Security Standards Council (PCI SSC) maintains, evolves, and promotes Payment Card Industry standards for the safety of cardholder data across the globe. The PCI SSC provides technical and operational requirements for organizations accepting or processing payment transactions. The guidance also applies to software developers and manufacturers of applications and devices used in those transactions.
The Payment Card Industry Data Security Standard (PCI DSS) helps entities understand and implement standards for security policies, technologies and ongoing processes that protect their payment systems from breaches and theft of cardholder data. The standards have historically been revised on a 2-3 year cycle, but the PCI SSC is transitioning to a posture of revising the PCI DSS as required based on changes to the current threat landscape. The current standard revision is PCI DSS Version 4.x. Any organization that handles payment card information must comply with the PCI DSS and must demonstrate compliance annually. Tenable Security Center is able to help organizations monitor ongoing PCI DSS compliance.
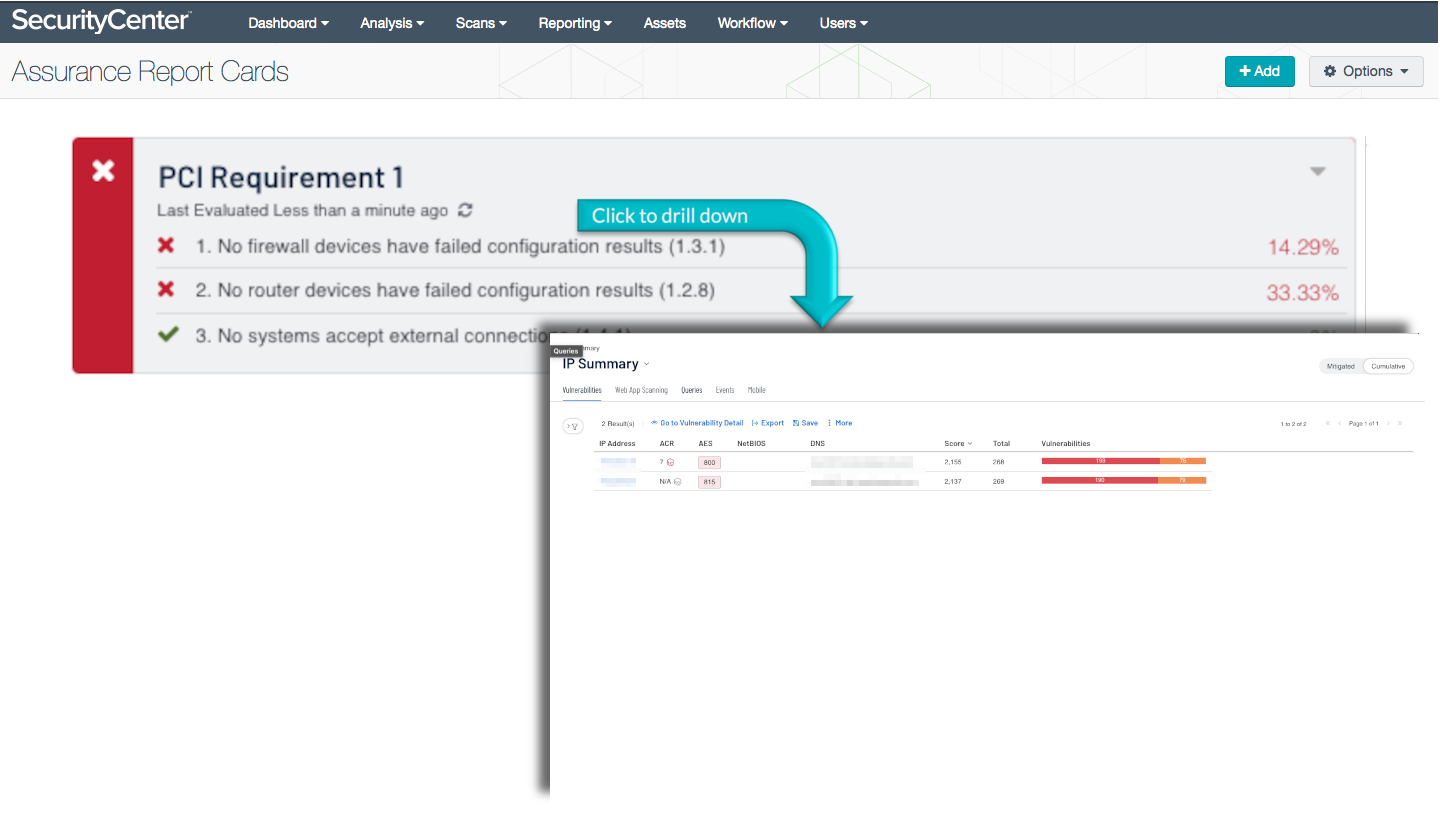
The PCI Requirement 1 ARC analyzes policy statements related to the first PCI DSS requirement. This requirement mandates organizations to secure the network border to protect cardholder data. A network segment that is of higher importance and requires robust protection is the network encompassing the cardholder data environment (CDE). The CDE is the most important network segment within the scope of PCI security requirements. Analysts and administrators need to ensure the CDE network provides appropriate protection for the CDE.
Organizations should focus on securing and hardening firewall and network devices such as routers and switches across all network segments. Devices such as these focus on providing a strong deterrent against attackers attempting to circumvent security controls. Security teams can use this ARC to identify and monitor network security related to meeting requirement 1 of PCI DSS.
Organizations can configure repositories or asset lists in order to tailor the focus of the ARC. When the dashboard is added from the Tenable Security Center Feed, the appropriate assets, IP addresses, or repositories can be specified. Assigning one of the options to the dashboard will update all filters in the components. By creating static or combination asset lists that include all systems in the CDE, each component can be filtered to display results directly related to ongoing PCI security. Using an asset list filter will also allow traffic into and out of the CDE to be monitored. In order to accurately measure an organization’s PCI security posture, asset lists need to be applied as filters to provide results focused on the CDE.
This ARC is available in the Tenable Security Center Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The ARC can be easily located in the Tenable Security Center Feed under the category Compliance. The ARC requirements are:
- Tenable Security Center
- Nessus
- NNM
Tenable's Tenable Security Center provides continuous network monitoring, vulnerability identification, risk reduction, and PCI compliance monitoring. Tenable Security Center is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of PCI regulatory compliance configuration audit files. Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context, enabling decisive action that transforms your security program from reactive to proactive. Active scanning of network devices examines the configurations on the network devices, running processes and services, and vulnerabilities. Continually scanning the network helps prioritize security efforts to mitigate threats and weaknesses. With increasing mobile and transient network devices, it is important to have a system in place that continuously monitors traffic, devices, applications, and communications across environments. Knowing when hosts come online and taking a zero-touch approach to assess them, Tenable enables powerful, yet non-disruptive, continuous monitoring of your network.
This ARC contains the following policy statements:
- No firewall devices have failed configuration results (1.3.1)
This policy statement displays the number of failed to total firewall configuration compliance checks. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Default firewall configurations settings may not provide adequate protection to the organization. To protect the organization against unauthorized access and potential compromise, administrators should harden firewall devices with vendor and best practice industry recommendations. - No router devices have failed configuration results (1.2.8)
This policy statement displays the number of failed to total router configuration compliance checks. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Default router configurations settings may not provide adequate protection to the organization. To protect the organization against unauthorized network activity and potential compromise, administrators should harden router devices with vendor and best practice industry recommendations. - No systems accept external connections (1.4.1)
This policy statement displays the number of systems that are accepting external connections to total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This policy monitors external connections to internal hosts. While some systems require external connections for business purposes, unauthorized external connections could introduce security risks. External connections are defined as connections from IP addresses that are not included within the monitored network range configured in the Nessus Network Monitor (NNM).
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success