by Cody Dumont
Governance, Risk Management, and Compliance is a substantial part of any information assurance program. The GRC requires information systems to be audited, regardless of the standard to which the audit is performed. These report provide the audit results for VMware vCenter/vSphere & Citrix XenServer.
One of the initial steps in a successful GRC program is to set configuration guidelines and establish a supportable set of security policies. Tenable.sc Continuous View (CV) can measure compliance, using audit files that cover a wide range of major regulations and other auditable standards. Tenable provides over 500 audit files, which are available for download from the Tenable Support Portal, in categories such as operating systems, applications, databases, and network devices. Tenable products can be used to audit systems based on SCAP content, and many Tenable audit policies have been certified by the Center for Internet Security (CIS). For more information on using audit files, see the Nessus Compliance Checks: Auditing System Configurations and Content document.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The report requirements are:
- Tenable.sc 4.8.1
- Nessus 8.5.1
- Compliance Data
Audit files can be customized to match the values defined in an organization’s corporate policies. The organization can review several audit files and then create a specific audit file that applies directly its policies. When an audit is performed, for each individual compliance check, Nessus attempts to determine if the host is compliant, non-compliant, or if the results are inconclusive and need to be verified manually. Unlike a vulnerability check that only reports if the vulnerability is actually present, a compliance check always reports a result. This way, the data can be used as the basis of an audit report to show that a host passed or failed a specific test, or if it could not be properly tested.
Tenable.sc Continuous View (CV) is the market leader in providing a unique combination of vulnerability detection, compliance auditing, and reporting. Tenable.sc CV supports auditing more technologies than any other vendor including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. This makes Tenable.sc CV the market-defining continuous network monitoring platform, and Nessus the market-defining vulnerability scanning for auditors and security analysts.
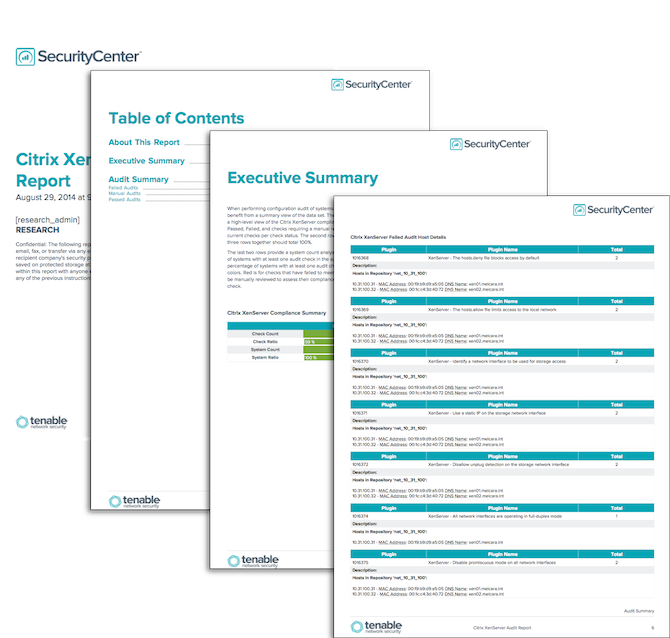
Citrix XenServer Compliance Checks: Tenable.sc CV using Nessus can audit XenServer hypervisors using the APIs published for Citrix XenServer and other vendors who create their own versions of XenServer based on open sourced code. This capability allows customers to harden the virtualization layer of their infrastructure. Too often, organizations forget to harden infrastructure, and this feature fulfills a critical component in a complete security program. Tenable blogged about this in 2013: Nessus Configuration Checks Available for Citrix XenServer. More information about audit files can be found in the Tenable Discussion Forums, Tenable Support Portal, Nessus Compliance Checks, and Nessus Compliance Reference.
VMware vCenter/vSphere Compliance Checks: Tenable.sc CV using Nessus can audit VMware vCenter/vSphere hypervisors using the VMware SOAP API to audit ESX, ESXi, and vCenter software. Three new customizable compliance audit files are now available on the Tenable Support Portal. The VMware-hardening Compliance Audit contains industry-standard recommendations used to harden VMware infrastructure. The Tenable vCenter/vSphere Best Practices Configuration Audit uses the VMware API to go beyond the hardening guidelines provided by VMware. There is additional information that Nessus is able to audit and report on that is useful to VMware administrators. For example, Nessus can report if VMware Tools is installed, the heartbeat settings on VMs, Guest operating system listings, overall VM status, floppy/CD-ROM drives connected, and iSCSI device status. The DISA VMware ESXi/vCenter 5 STIG Audit implements the majority of the recommendations provided by recent version of the DISA VMware ESXi/vCenter 5 Security Technical Implementation Guide (STIG). Tenable blogged about this in 2013: Nessus VMware vSphere/vCenter Audits. More information about audit files can be found in the Tenable Discussion Forums, Tenable Support Portal, Nessus Compliance Checks, and Nessus Compliance Reference.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success