by Josef Weiss
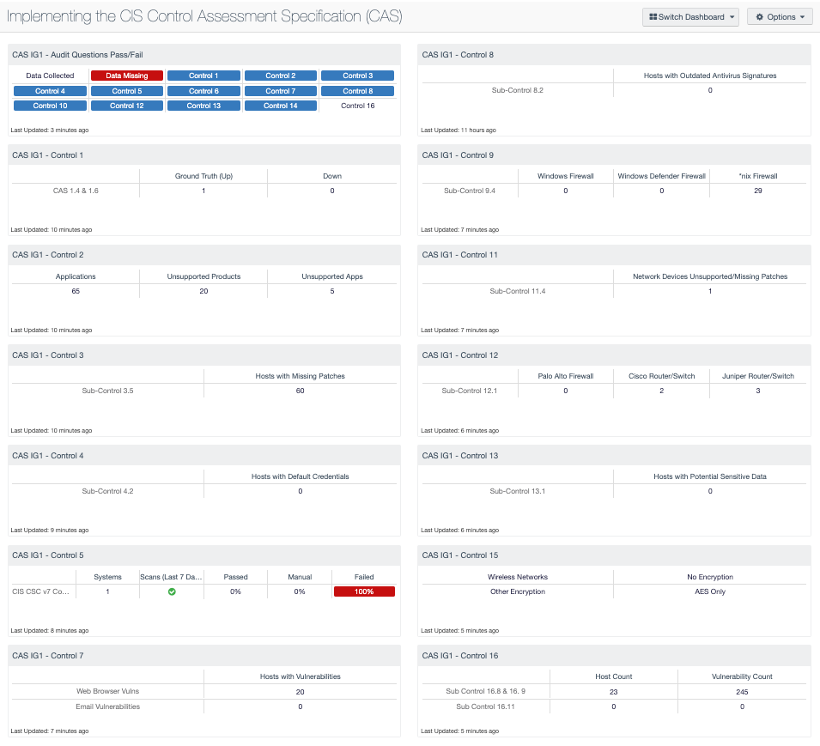
The Center for Internet Security (CIS) and Tenable partnered together to create a guide to help customers understand how to implement the CIS Controls. Starting with the SANS Top 20 Controls published several years ago, Tenable has continuously helped customers leverage Tenable.sc to understand their security posture using these controls. CIS Controls version 7.1 introduced the concept of Implementation Groups (IGs), which are self-assessed categories for organizations based on specific cybersecurity attributes. The security community has assessed the CIS Controls and identified these 20 controls to be reasonable for an organization to implement. By grouping the controls into horizontal cuts across each control, the implementation is easier to understand and integrate into security operations. These controls require several different scans and audit actions to verify the IG1 requirements are being implemented. This dashboard is used with the CIS Control Assessment Specification (CAS) to show organizations how to measure the controls supported by Tenable.sc.
To aid customers, CIS produced a Control Assessment Specification (CAS), which provides a very detailed set of input, metrics, and other details about how to measure the compliance. The 20 CIS Controls™ are broken down into 3 section, they are: Basic, Foundational, and Organizational. The Basic section (first 6 controls) are commonly referred to as the “cyber hygiene” controls. Tenable established Cyber Exposure as an emerging discipline for managing and measuring cybersecurity risk in the digital era. To facilitate this emerging discipline, Tenable also established the Cyber Exposure Lifecycle.
Tenable has extended this guidance with a CIS Deployment guide. This dashboard is designed to work hand-in-hand with the CIS Deployment guide. The matrices in this dashboard refer to specific queries and information requested from the CAS. Taking into consideration that the organization has a functioning active scanning program, the dashboard should initially populate with valuable information that will assist with understanding of the IG1 requirements. While this dashboard focuses on IG1, the data collected is often beneficial for all IG levels. In some cases the data collected is a requirement for IG2, but will be beneficial in IG1. For example with Control 1, the requirement is to maintain an inventory. Shown below in the “CAS IG1 - Control 1” matrix, the counts provide the data that would help populate the inventory, but not actually be the organization's inventory, as the inventory should exist outside of Tenable.sc. The filters in the “CAS IG1 - Control 1” matrix leverage active and passive scanning, both of which are a requirement in IG2.
Additionally Tenable.sc has a new audit file type that allows the risk manager or CISO to input data often required in a compliance report, but is not a technical control, for example, the file name of a corporate policy. These checks are added with use of the “CAS Implementation Group 1 Audit File.” This audit file helps drive focus on more administrative controls, such as: Does a policy exist and where is the file located? Many times the risk managers are asked to provide a single report to auditors to provide all the data related to the audit. With this new audit file feature, risk managers and security teams can ask these types of audit questions and provide the needed answers. The first cells provide an indicator of the data collection process. If the answers are any value other than the default of “None” or “No”, the “Data Collected” indicator will be enabled. For any of the questions that are still the default, “Data Missing” will be enabled. For each of the controls with questions that are present in the audit file, there is a separate question.
This dashboard should be used in conjunction with the corresponding report available here:
Implementing the CIS Control Assessment Specification (CAS)
Listed below are other dashboards that are helpful in deploying the CIS Controls v7.1.
• CIS Control 1: Inventory of Hardware Assets
• CIS Control 2: Inventory and Control of Software Assets
• CIS Control 3/18: Continuous Vulnerability Management & Application Security
• CIS Control 4/5: Secure Configurations & Group Memberships
• CIS Control 8: Malware Defenses
• CIS Control 9/12: Monitoring Ports, Services and Network Boundaries
• CIS Control 11: Secure Network Devices
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The reports can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.15.0
- Nessus 8.11.1
- CAS Implementation Group 1 Audit File
Tenable provides organizations with the means to effectively address a number of the security challenges with implementing the CIS Controls v7 and assists with navigating the CAS. Tenable.sc CV is the most strategic source to start a cyber hygiene for both public and private sector organizations, making foundational cybersecurity more affordable, accessible, and actionable. Tenable is the first and only vendor to automate both the implementation and auditing of an organization’s adherence to IG1, maximizing limited budgets and resource-constrained teams. Tenable.sc and CAS together help organizations transform the Controls into actionable cybersecurity recommendations and integrate basic cyber hygiene across their operations.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success