Taking IBM QRadar SIEM One Step Further Using Tenable.ad

If you can't continuously monitor Active Directory, it's impossible to achieve full visibility into your evolving attack surface. Here's how combining Tenable.ad with IBM QRadar can help.
It's no secret that CISOs are constantly challenged with new cyberthreats across an expanding attack surface. The average workplace has shifted from traditional assets, such as desktops and workstations, to a more dynamic spread that includes mobile, cloud, web applications and operational technology (OT) environments. But, no matter the size and scope of your attack surface, three questions always remain the same when protecting the organization:
- Is there anything else that puts us at risk?
- How do I manage our dynamic mix of assets and applications?
- How can I achieve a centralized view of all my security information?
Most organizations leverage Active Directory (AD) to manage users, employees and contractors, as well as to control which assets the users have access to within the organization. But viewing Active Directory as simply a tool for managing access and authentication privileges overlooks the complexity inherent in such a system. Organizational churn requires constant adjustments to how privileges and group policies are configured. Yet, many organizations are unaware of the significant risk posed by Active Directory.
Active Directory not only holds the keys to the kingdom, so to speak. It goes as far as providing the blueprint of the entire castle. Yet, organizational silos often mean security professionals have minimal insight and monitoring abilities into their organization's Active Directory, leaving IT teams unable to find and fix flaws before they become business-impacting issues. If a threat actor gains an initial foothold by leveraging a misconfiguration in Active Directory, they can use the compromised credentials to move laterally, potentially gaining unprivileged access to email, important corporate data, users and credentials and access to applications and cloud resources. The original infiltration could quickly evolve into a critical security breach without the organization even knowing about it because many security teams lack continuous visibility into Active Directory. To answer the first question from earlier, ‘is there anything else' - Yup, Active Directory is it!
So how do you go about securing such a complex and ever-changing directory of users?
Tenable.ad, a new solution in the market, aims to help security professionals solve the daily challenges of managing and protecting the long-lived, dynamic lists of access points contained in Active Directory. Tenable.ad enables you to prioritize and prevent misconfigurations in Active Directory to disrupt attack paths before attackers exploit them.
Tenable + IBM QRadar
Now, let's consider our second and third questions: how do I manage our dynamic mix of assets and applications?; and how can I achieve a centralized view of all my security information?
Tenable's Technology Ecosystem allows customers to enhance their data visibility by using Security Information and Event Management (SIEM) partners, like IBM QRadar. IBM QRadar helps security teams accurately detect and prioritize threats across the enterprise, and it provides intelligent insights that enable teams to respond quickly to reduce the impact of incidents. By consolidating log events and network flow data from thousands of devices, endpoints and applications distributed throughout your network, QRadar correlates all this different information and aggregates related events into single alerts to accelerate incident analysis and remediation.
Up to this point in the strong IBM partnership, Tenable has been able to integrate with IBM QRadar to bring in vulnerability insights and misconfigurations from Tenable.io, Tenable.sc and Tenable.ot. This allows security teams to improve decision making and correlate events to take action on flaws using Tenable IT and OT findings. Tactically, security teams are able to get rich summary data for security investigations for a given offense at the asset level.
With the release of Tenable.ad into the market, IBM QRadar now adds Tenable.ad to its suite of supported products, offering a way for security teams to gain full visibility of their blind spots, including IT, OT and now AD, all within the IBM QRadar interface.
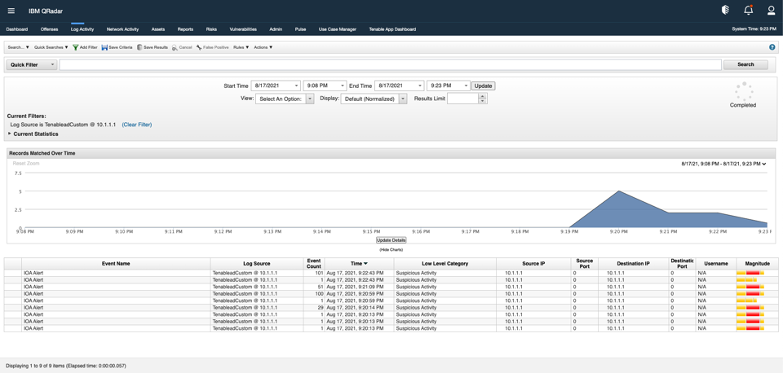
Source: Tenable and IBM QRadar, September 2021
To add some context, the above image gives security analysts a view of Tenable's Active Directory data in the form of "Indicators of Exposure." These security events found within QRadar also provide the source, the magnitude of the attack and a visual timeline of the event. Combining all of Tenable's rich vulnerability information, the integration now gives the ability to strengthen event investigations and give peace of mind to CISOs who constantly ask themselves the same three questions every day.
IBM Security is a featured partner within Tenable's Technology Ecosystem, which contains over 95 partners and 125+ unique integrations. The breadth and depth of Tenable's ecosystem helps joint customers improve their security programs by combining Tenable's market-leading risk-based vulnerability management solutions with other security applications in their environment. This "better together" approach helps serve and strengthen security programs of all sizes around the world.
Learn More:
- To learn more about Tenable.ad, visit the Tenable.ad product page
- Read more about the Tenable + IBM Partnership here
- For more information on the integration, dowload our Solution Overview
- Download IBM QRadar from IBM's App Exchange
Learn more
- Active Directory
- Cloud
- Energy Industry
- Executive Management
- Endpoint security
- Event Monitoring
- BYOD
- OT Security
- Partnerships
- Integrations
- Remote Workforce
- Risk-based Vulnerability Management
- Threat Management
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success