How to Extract Data and Value from Tenable’s EASM Solution

It’s essential for external attack surface management products to offer users a variety of data-extraction methods so that they can use the data in different scenarios and use cases. Learn how Tenable.asm’s various data-extraction capabilities can help you operationalize your EASM data.
One of the first things organizations want to do after building an external attack surface map is to start extracting data out of the system so they can use the data within other workflows. That’s understandable because an external attack surface management (EASM) tool should be treated more like a data pipeline in a security management process. As the external asset data flows in, it is enriched and then extracted into useful buckets of data to triage.
An EASM solution should offer a variety of data-extraction methods in order to give users flexibility to operationalize data and options so they can choose the best method based on their needs and use cases. That’s how Tenable.asm is designed.
In this blog, we’ll explain how and when you might use different extraction methods, why they’d be useful for different scenarios, and how to use Tenable.asm’s robust data-extraction capabilities.
Using the data within the user interface
First and most obvious is viewing the data right within Tenable.asm user interface. At first blush, people may overlook this option, but it's one of the most useful methods to view the data in real time. Here are some instances where using the UI is convenient and powerful.
- Often people have theories and to prove or disprove them they look for patterns and signals in the EASM metadata. For instance, let's say you want to know if you have any Apache 2.2 web servers in your network. That type of binary question is best answered by looking at the data in the UI and seeing what assets – if any – show up.
- Many times executives will want to know something like: “Are we still using our old branding in any assets?” or “How many XYZ products do we have?” because the organization wants to replace them and needs to know that number. The UI method is particularly well suited for obtaining a one-time snapshot check of how many, say, Windows laptops you have, because it’s not something you want to ask of the data every day.
CSV, XLSX and JSON exports
The second method to get data out of Tenable.asm is via an XLSX, CSV or JSON download. This makes sense when people want to download data into some other tool like Excel to do additional analysis/processing so they can come up with numerical data for reporting, or when they want to use the output of the downloads as an input to other tools, like dynamic web application scanners. If you want to run a manual penetration test, you can utilize a one-off download of the assets and give them to your penetration testing partner, so that they don’t have to guess what your company’s infrastructure is.
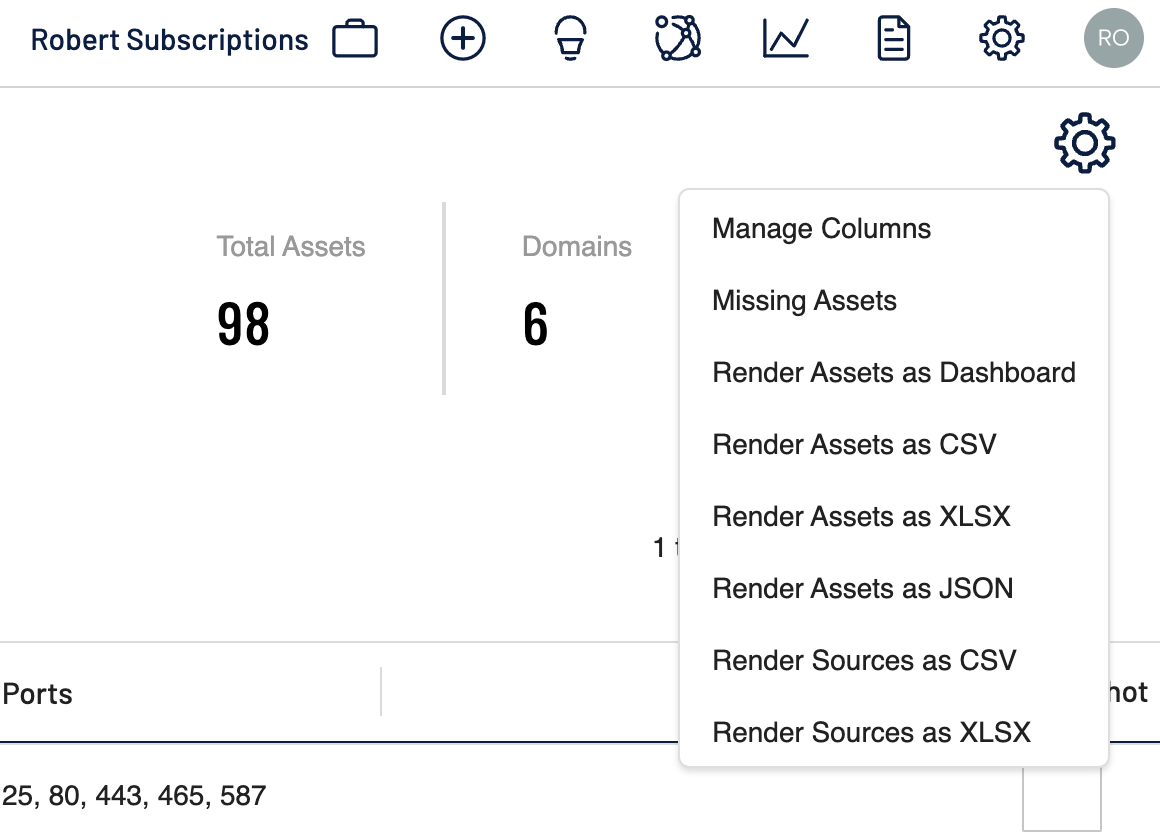
Incidentally, it turns out that many of Tenable’s customers have inventories that are so large that attempting to download all of the assets in XLSX and then opening them in Excel just crashes Excel, so that is why we have given a number of different download functions. One other extremely useful feature is that the download function only downloads the visible columns of data on the screen at the time of downloading. So if you need only to download the hostnames and IPs, you won’t have to wrestle with 150+ different columns of data to extract the one that you’re after.
Another useful feature of the JSON download is for our customers to monitor third-parties; for example, when an acquirer wants to identify changes in the third-party’s assets over time. After an initial one-time analysis (a point in time download) of the inventory, the bulk of the value comes from the deltas between what was initially downloaded and what the state of the inventory is at any time in the future. Having a full dump of all the assets is particularly useful for identifying changes.
Subscriptions
The third method of extracting data out of Tenable.asm is by utilizing subscriptions, which could be thought of as active monitoring. Once a day the subscriptions will fire looking for assets that meet your pre-set criteria, such as monitoring upcoming SSL certificates that are about to expire. The data generated by the subscriptions can then be funneled for triage into a number of different systems, like chatops; security orchestration, automation and response (SOAR) software; or trouble ticketing systems. This is one of the most commonly used methods of extracting data from the system because automation frees your staff to focus on other more strategic tasks.
Alternatively, subscriptions can be shared, using a unique link, with other team members or third-parties who need access to the data on an ongoing basis, but who don’t need to have access to the entire inventory. Using subscriptions in this way can reduce the daunting back-and-forth exchange by allowing users to access both a real-time vs snapshot version of the inventory.
The API
Lastly, one of the most efficient methods of extracting data is to leverage the Tenable.asm API. Advanced customers will eventually prefer to use the API over the other data-extraction methods because it is highly efficient to have two machines talk to one another and to store the data locally for enrichment and further processing. The API uses swagger, which is a very intuitive API documentation that can allow users to test their queries in real-time, so it is incredibly easy to build prototypes. Not to mention there are sample scripts that Tenable.asm has built to help developers easily extract data.
Further, Tenable.asm eats our own dogfood, so to speak, and utilizes the same API endpoints that our customers do on our front-end. That means that we have made our API easy for customers to use because it is easy for us to use. In fact, users who leverage modern web browsers can turn on dev tools and watch the HTTP traffic in their browser. The same requests that are seen on the front-end exist as APIs that can be leveraged by the customer. This speeds up prototyping of potential methods of extracting specific datasets of interest.
Putting it together
By providing this variety of data-extraction options, Tenable.asm offers users great flexibility and power to gain valuable insights into their attack surface.
For instance, I can leverage the UI to test my hypothesis with a set of filters. Then I can download that data in CSV, XLSX or JSON formats and send it over to another team to validate its accuracy. I could then use subscriptions to run a test to make sure everyone agrees it is updating in the way that my custom code and database expect, without giving other parties access to the rest of the inventory. Then finally I can set up a back-end request directly connecting the API to internal systems that can fully automate the process, so that no humans are ever required to be involved in consumption of that specific ongoing querying of data again, until some other use case is identified.
In this way, a traditional user interface can seem a bit antiquated given that humans tend to become the bottleneck. We believe that end users should only have to do a task once or maybe twice – once to validate the theory is correct and once to set up the automation. After that, the systems should talk to themselves.
Tenable.asm’s user interface should be used to:
- further enrich data
- better slice and dice inventories using tagging and separation of assets by inventory
- adding new assets as they become available/known
Once that work has been completed to a customer’s satisfaction, the rules engines and supplemental download functions take over, allowing full automation. By having these methods of working with and extracting data in these various forms in Tenable.asm, it becomes possible to operationalize the data in many different ways either in common uses and in custom ways.
If you have questions or want to learn more, visit our Tenable.asm product page to see how external attack surface management can accelerate your journey to exposure management.
Learn more
- Attack Surface Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success