Hardcoded Credentials Expose Customers of AT&T U-Verse
On August 31, 2017, Nomotion released five vulnerabilities for two Arris modems used by AT&T U-Verse customers in the US. The vulnerabilities are of the following types:
- Hardcoded Credentials (CWE-798)
- Information Exposure (CWE-200)
- Authenticated Command Injection (CWE-78)
- Firewall Bypass (CWE-653)
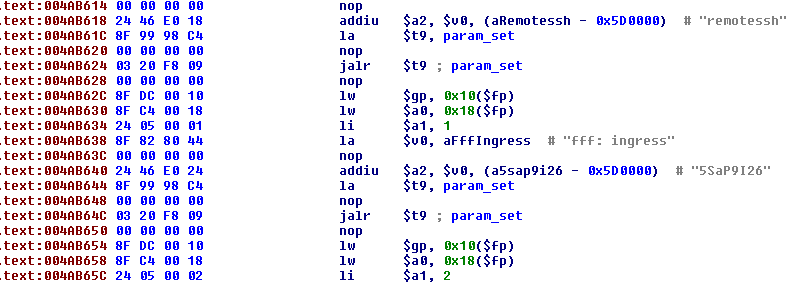
The hardcoded credentials give attackers access to the device via SSH or HTTP/HTTPS. On certain devices, when logged into the modem, the attacker can then leverage the authenticated command injection vulnerabilities to get a root shell. This vulnerability is especially bad for users whose devices are exposed to the internet.
The firewall bypass vulnerability is particularly worrisome. After successfully gathering the list of hosts behind the firewall using the port 61001 information exposure, an unauthenticated remote attacker can then connect to any device behind the firewall by using the firewall bypass. Effectively opening the internal network to attack.
Nomotion reported that these vulnerabilities were found on the following Arris models used by AT&T U-Verse:
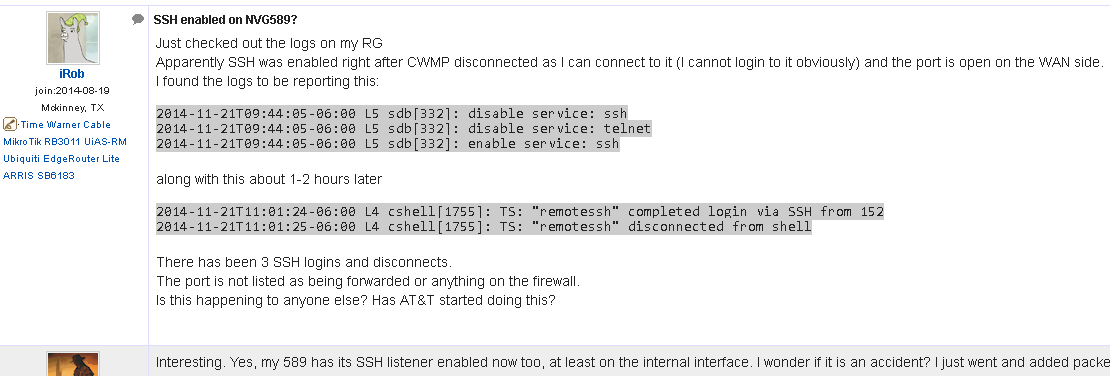
- NVG589
- NVG599
Tenable Research has further identified that Arris made Motorola DSL modems 2210, 2241, 2247, 2310, 3347, and 3360 are currently vulnerable to one or more of these vulnerabilities. Additionally, some newer AT&T U-Verse devices such as the Arris 5268AC also suffer from one or more of the vulnerabilities. Arris 5268AC’s newer firmware contains the embedded bdctest credentials mentioned in Nomotion’s disclosure as well as the firewall bypass vulnerability (this is partially mitigated due to the increased difficulty associated with obtaining the device’s serial number). Tenable has reached out to Arris to inform them of the Nomotion research as well as the additional vulnerable devices.
Despite the recent disclosure of the vulnerabilities, public reference to remote SSH access via the “remotessh” user account has been previously published on November 2014 post on dsl-report.com:
Furthermore, the last firmware Arris released for many of these devices was 9.1.1h0d34 released back in May 2013. That’s not to say that the various ISPs that use these devices haven’t been issuing their own patches though.
In response to these vulnerabilities, Tenable has released the following plugins:
- Plugin ID 102915: Hardcoded SSH credentials
- Plugin ID 102916: AT&T U-verse Arris Modems NVG589 / NVG599 / 5268AC Multiple Vulnerabilities (SharknATTo)
Because no updated firmware that remediates these issues has yet been deployed or made available, Tenable recommends customers follow Nomotion’s mitigation guide until Arris or AT&T provide a formal response. Customers should also always be wary about the services they are exposing to the internet and minimizing the attack surface as much as possible.
Learn more
- Internet of Things



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success