Synopsis
While investigating the Grandstream UCM6202 IP PBX, Tenable discovered a few SQL injections that an unauthenticated remote attacker could use to obtain user passwords.
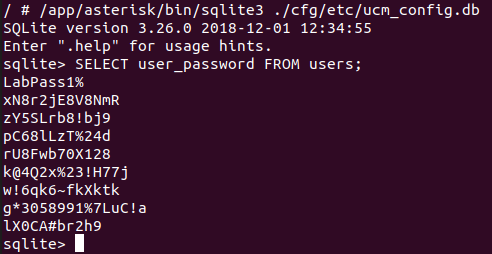
CVE-2020-5723: Cleartext Storage of Sensitive Information (CWE-312)
The UCM6200 series stores unencrypted user passwords in an SQLite database. This could allow an attacker to retrieve all passwords and possibly gain elevated privileges.
CVE-2020-5724: Unauthenticated Remote Blind SQL Injection
The webserver's websockify endpoint is vulnerable to SQL injection when the challenge action is invoked. The username provided by the unauthenticated remote attacker is used to build an SQL query into the users table. Furthermore, successful queries and unsuccessful queries generate different responses from the server. As such, an unauthenticated remote attacker can recover user passwords.
A proof of concept can be found in our GitHub repository.
CVE-2020-5725: Unauthenticated Remote Blind SQL Injection
The webserver's websockify endpoint is vulnerable to SQL injection when the login action is invoked. The username provided by the unauthenticated remote attacker is used to build an SQL query into the users table. As such, by using time based attacks, an unauthenticated remote attacker can recover user passwords.
A proof of concept can be found in our GitHub repository.
CVE-2020-5726: Unauthenticated Remote SQL Injection via CTI
The CTI server on port 8888 is vulnerable to SQL injection when the challenge action is invoked. The username provided by the unauthenticated remote attacker is used to build an SQL query into the users table. Furthermore, successful queries and unsuccessful queries generate different responses from the server. As such, an unauthenticated remote attacker can recover user passwords
A proof of concept can be found in our GitHub repository.
Solution
Upgrade to 1.0.20.22 or newer.Additional References
http://firmware.grandstream.com/Release_Note_UCM6xxx_1.0.20.22.pdfhttps://github.com/tenable/poc/blob/master/grandstream/ucm62xx/websockify_challenge_injection.py
https://github.com/tenable/poc/blob/master/grandstream/ucm62xx/websockify_login_injection.py
https://github.com/tenable/poc/blob/master/grandstream/ucm62xx/cti_injection.py
Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success