by Steve Tilson
Having and maintaining accurate host configuration information for all devices in an environment is a difficult task for analysts. Organizations require this information for deployment and active inventory checks; however, information provided may also assist in audit and security checks. This report provides administrators with basic information for all hosts on the network that have been scanned by Nessus.
The scan information in this report includes information such as the IP address, NetBIOS name, DNS name and MAC address for each host, along with more detailed information, such as network interface information, user accounts, operating system, manufacturer information, BIOS information, installed software and CPE matches. This organized table of basic information may critically assist when planning, tracking and verifying host deployment activities.
Organizations generally develop standards and guidelines for their network environment. This report displays the basic, but critical, information with which organizations can verify deployment settings. Most common standards maintained by organizations are equipment manufacturers with specific OSes, software installed and host naming convention. Others include specific administrative or guest accounts disabled, correct BIOS versions and verification of correct IP for the host deployed.
This dashboard is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Compliance & Configuration Assessment.
The dashboard requirements are:
- SecurityCenter 5.4.5
- Nessus 6.10.5
- LCE 5.0.1
Tenable SecurityCenter provides continuous network monitoring, vulnerability identification and security monitoring. SecurityCenter is continuously updated with information about advanced threats and zero-day vulnerabilities and new types of regulatory compliance configuration audit files. Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context, enabling decisive action that transforms a security program from reactive to proactive. Active scanning periodically examines the applications on systems, running processes and services, detections of web applications, configuration settings and additional vulnerabilities. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Tenable enables powerful, yet non-disruptive, continuous monitoring of the organization to ensure vulnerability information is available to analysts.
Note that this report might be very long, depending on the number of hosts on the network. Consider modifying the Host Summary table and the Hosts iterator in the report definition and filtering on an asset, to produce a more specific and more manageable report.
This report contains the following chapters:
About This Report: Having and maintaining accurate host configuration information for all devices in an environment is a difficult task for analysts. Organizations require this information for deployment and active inventory checks; however, information provided may also assist in audit and security checks. This report provides administrators with basic information for all hosts on the network that have been scanned by Nessus.
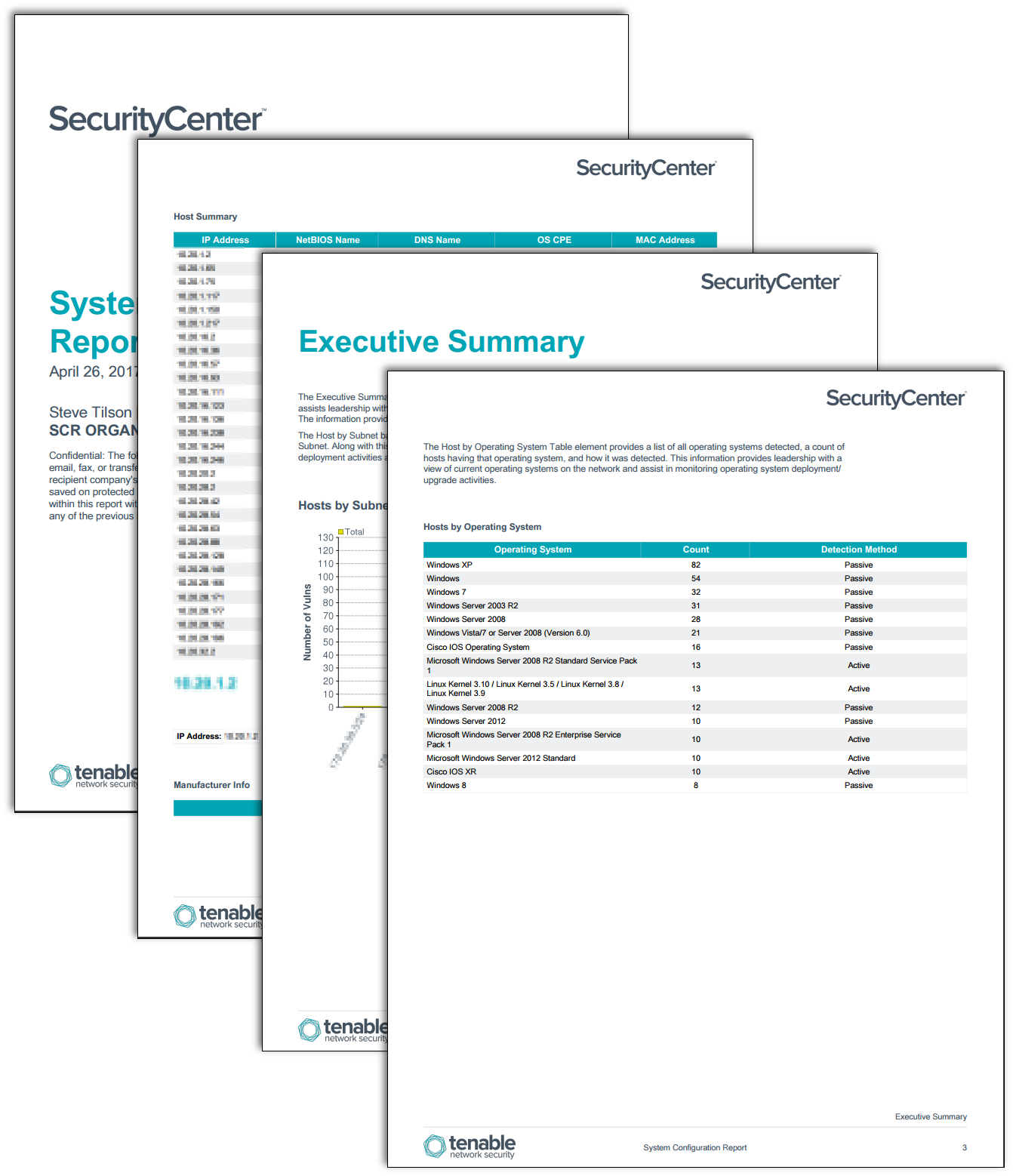
Execuitve Summary: The Executive Summary provides a high-level view of host information found in the environment. This view assists leadership with a brief understanding of the current endpoint configurations detected on the network. The information provided assists in the monitoring and evaluation of deployment activities.
System Configuration: The System Configurations chapter provides information about all hosts on the network that have been scanned by Nessus. The Host Summary table presents basic information for the hosts. This basic information includes IP address, NetBIOS name, DNS name, OS designation and MAC address along with more detailed information presented for each host.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success