All organizations have different and unique combinations of software and hardware in the environment. Software such as operating systems and office productivity suites are common across different organizations, but may still have different versions. With most software and hardware in use in an organization, vulnerabilities are present in one way or another. The best way to remediate a vulnerability is to first detect the vulnerability.
When analysts have accurate information of what vulnerabilities are present in the environment with Tenable products, they can take knowledgeable action to remediate vulnerabilities or mitigate the risk. This report can be used as a method to ensure that analysts are able to maintain situational awareness of vulnerabilities. The report displays information from all Tenable Nessus and Tenable Nessus Network Monitor (NNM) plugin families.
The products offered by Tenable are capable of analyzing many types of software and hardware. As a result, there are many plugin families covering a great deal of different types of software and hardware grouped by a common theme, such as “Windows: Microsoft Bulletins”. There are currently over 60 plugin families between Nessus and NNM. The plugins within each family detect and evaluate information using both active scanning and passive listening approaches. Having these two methods of detection and evaluation helps organizations to be constantly aware of vulnerabilities in the environment.
Since a great deal of information is returned in this report, the first 10 results are presented for each plugin family. Analysts can reconfigure the returned results to better reflect the needs of the organization. Additionally, appropriate scans need to be in place for this report to be completely effective.
Active scans performed with Nessus and passive listening performed with NNM benefit the organization in unique and important ways. When analysts assess the network with Nessus, active scans are used to identify systems and software across the network. With active scanning and Nessus Agents, analysts obtain thorough and detailed information for each system. Depending on the organization, Nessus scans need to be set up to include all plugin families to populate this report. Analysts can choose to configure multiple scans with different plugin families to best suit the needs of the organization.
NNM provides actionable and detailed information about the network. When NNM is able to passively collect information at appropriate network locations, analysts benefit from concise knowledge derived from the network traffic inspection. The plugins within the NNM plugin families can populate this report with potentially never before seen information about the network.
Once Nessus and NNM are properly configured to scan and listen to the environment with all plugin families, analysts will see insightful and relevant information about their environment. Results feed into this report as well as many other dashboards, reports, and ARCs available within Tenable.sc. The dashboards, reports, and ARCs provide information necessary for increased situational awareness of vulnerabilities. This report can provide a great high-level insight into the environment helping analysts stay more vigilant with more information of the environment.
This report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. This report can be easily located in the Tenable.sc Feed under the category Executive. The report requirements are:
- Tenable.sc 5.4
- Nessus 8.6.0
- NNM 5.9.0
Tenable's Tenable.sc provides continuous network monitoring, vulnerability identification, and security monitoring. Tenable.sc is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audit files. Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context, enabling decisive action that transforms your security program from reactive to proactive. Active scanning examines the devices on the systems, running processes and services, configuration settings and services, and additional vulnerabilities. Continuously listening to the network with passive sensors for servers, desktops, and applications helps prioritize security efforts to mitigate threats and weaknesses. Organizations continue to operate with more mobile and transient network devices and need to have a system in place that continuously monitors traffic, devices, applications, and communications across environments. Tenable enables powerful, yet non-disruptive, continuous monitoring of the organization to ensure accurate and up-to-date information is presented on existing vulnerabilities discovered within the network.
This report contains the following chapters:
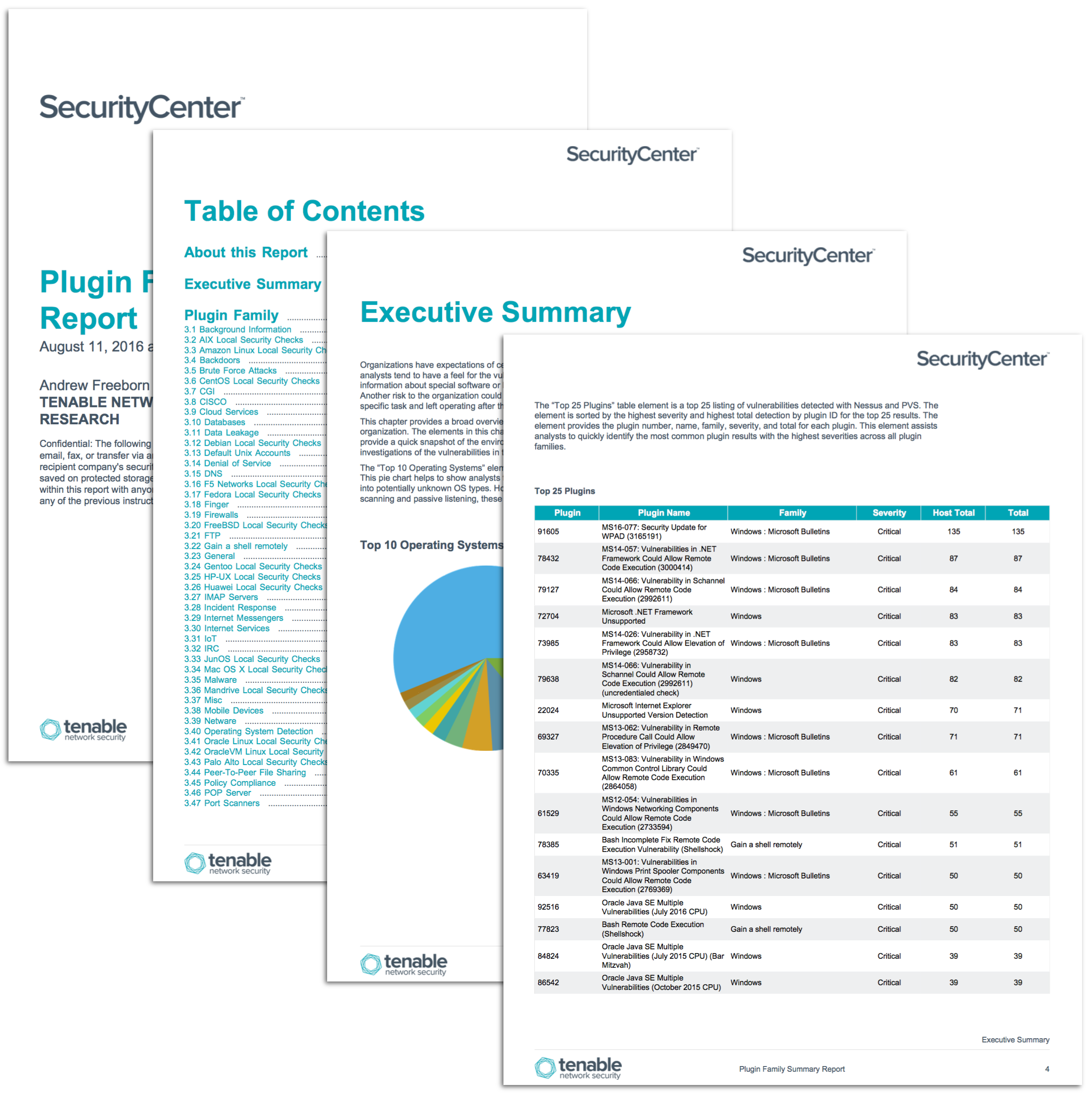
- Executive Summary: This chapter provides a broad overview of the vulnerabilities associated with software and hardware in the organization
- Plugin Family Summary: This chapter lists all of the plugin families available with Nessus and NNM
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success