As Governance, Risk, and Compliance (GRC) measures continue to be adopted by organizations, security teams will continue to face challenges in properly managing the complex requirements from multiple regulations and standards. Some organizations continue to rely on manual processes or inadequate tools that do not provide the real-time data needed to properly identify and mitigate existing risks. The chapters within this report can assist in managing and maintaining compliance throughout all aspects of a network by providing an accurate, real-time look at an organization’s risk and compliance status.
The ISO/IEC 27002:2013 provides a framework that can be used to develop and enhance information security policies for any organization. Each security control and objective provided within the standard can be tailored to specific business and regulatory objectives, and assist with maintaining overall compliance. This report aligns with the ISO/IEC 27002 18.1 control, which can help to ensure that legal and regulatory compliance requirements are properly managed across the enterprise.
Maintaining compliance allows organizations to reduce exposure risks, protect essential assets, and ensure that confidential information remains secure. Organizations cannot afford excessive compliance related costs due to inadequate tools, manual controls, or non-compliance. The best way to ensure total compliance is to deploy automated compliance solutions that continuously monitor the network. Tenable.sc Continuous View (CV) provides the key solutions that organizations need to scan and monitor every asset throughout the enterprise. Organizations will gain complete visibility on existing vulnerabilities and compliance status, which can help enable a faster response time to address and remediate vulnerabilities. Nessus will assist with performing compliance checks and alert organizations to issues with password requirements, existing configurations, disabling unnecessary services, and more. By continuously monitoring the network, organizations will be able to reduce the attack surface and ensure compliance.
This report provides the latest information on ISO based compliance checks. The Compliance Summary chapter presents information on compliance audits checks against existing hosts, and reports on systems that have passed, failed, or require manual checks. Each control objective that’s displayed will alert analysts and security teams to compliance failures across network assets. Compliance check failures indicate that the collected result and the expected result do not match. A mismatch may not indicate a failure, and should be reviewed further to determine whether the result is correct. Additional elements in this report also include database compliance checks from some of the most widely used database systems. Hosts with database compliance issues may include database accounts that need to be disabled, installing the latest service pack, or other configuration changes that should be made. Analysts can use this information to help address and harden systems with database compliance issues.
This report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The report requirements are:
- Tenable.sc 5.3.1
- Nessus 8.5.1
- Compliance Data
- Local Checks
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring platform. Tenable.sc CV enables you to react to advanced threats, zero-day vulnerabilities and new forms of regulatory compliance. Nessus is the global standard in detecting and assessing network data, and supports more technologies than any other vendor including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure. Tenable provides continuous network monitoring to identify vulnerabilities, reduce risk and ensure compliance.
The report contains the following chapters:
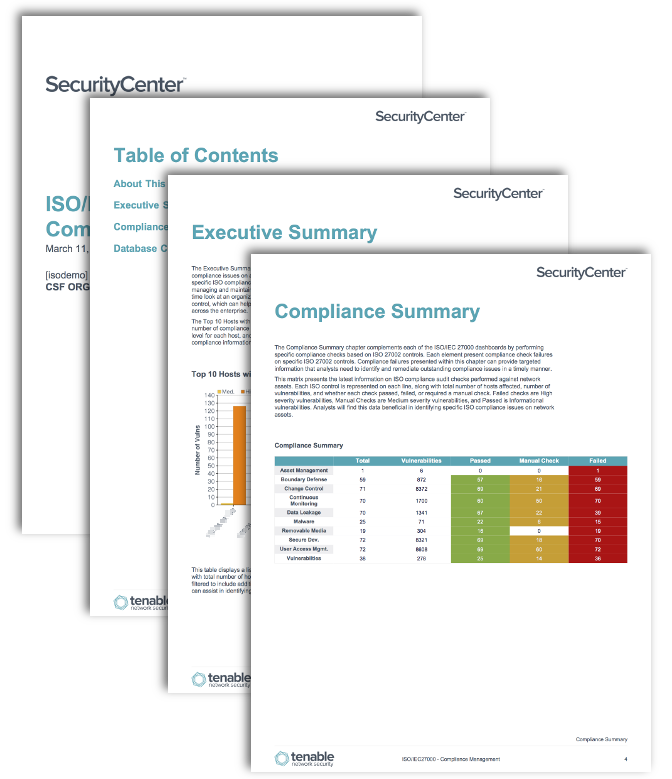
- Executive Summary: The Executive Summary chapter presents a high level overview of the top ISO/IEC 27000 and database compliance issues on a network. Within the compliance summary chapter includes multiple tables with specific ISO compliance check failures on network assets. The chapters within this report can assist in managing and maintaining compliance throughout all aspects of a network by providing an accurate, real-time look at an organization’s risk and compliance status. This report aligns with the ISO/IEC 27002 18.1 control, which can help to ensure that legal and regulatory compliance requirements are properly managed across the enterprise.
- Compliance Summary: The Compliance Summary chapter complements each of the ISO/IEC 27000 dashboards by performing specific compliance checks based on ISO 27002 controls. Each element present compliance check failures on specific ISO 27002 controls. Compliance failures presented within this chapter can provide targeted information that analysts need to identify and remediate outstanding compliance issues in a timely manner.
- Database Compliance Summary: The Database Compliance Summary chapter presents information from database compliance checks on network assets. Compliance checks are performed against the top most commonly used database servers. Each element includes compliance check information on the respective database server types. Analysts must setup appropriate database credentials and audit files before initiating database compliance scans. The information provided within this chapter will allow organizations to obtain the precise information needed to quickly address and remediate database compliance issues.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success