by Josef Weiss
Databases can potentially store valuable data for an organization that may not have daily database activity monitoring mechanisms in place. Many organizations involved in retail, financial, healthcare, and other industries benefit from the utilization of databases to store customer, financial, or healthcare information. Regulations such as PCI, SOX, and HIPAA have stringent compliancy requirements to safeguard the personal information of customers
This report enumerates known databases and resources, such as Microsoft SQL Server, MySQL, and Oracle. The report displays information for enforcing and verifying IT management policies relating to assets, such as vulnerability, configuration, and remediation policies. Analysts are provided with vulnerability data, which can be easily used to assist in reducing database vulnerabilities.
The chapters in this report leverage data gathered by active vulnerability scanning with Tenable Nessus and passive vulnerability detection with Tenable Nessus Network Monitor (NNM). The data collected is filtered to provide insight into the vulnerabilities related to database software in the environment. Vulnerabilities are tracked by time, severity, and exploitability in order to provide a more complete view of the security status of the network. Security teams can use this report to assist in identifying, monitoring, and remediating vulnerabilities within database software that may expose their organization to risk.
The report uses the Common Platform Enumeration (CPE) filter to identify many of the software programs used in enterprise networks. According to NIST, the CPE is a structured naming scheme for information technology systems, software, and packages. Based upon the generic syntax for Uniform Resource Identifiers (URI), CPE includes a formal name format, a method for checking names against a system, and a description format for binding text and tests to a name. Tenable assigns CPEs to plugins where appropriate. This allows for analysts to search for common CPE prefixes such as “cpe:/a:mysql:mysql,” “cpe:/a:oracle:database,” and “cpe:/a:firebirdsql/firebird.” Associating CPE strings with vulnerabilities allows the analysts a greater view into separating operating system vulnerabilities from application vulnerabilities, and adds to the level of vulnerability detail provided to the organization.
The corresponding dashboard can be found here:
Database Software Vulnerabilities Dashboard
This report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments.
The report requirements are:
- Tenable.sc 5.3.1
- Nessus 8.6.0
- NNM 5.9.0
- LCE 6.0.0
Tenable's Tenable.sc provides extensive network monitoring by leveraging a unique combination of detection, reporting, and pattern recognition utilizing industry recognized algorithms and models. Tenable.sc is continuously updated to detect advanced threats and vulnerabilities. Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context and enabling decisive action that transforms the security program from reactive to proactive. Continuous vulnerability analysis enables security teams to more effectively tailor remediation efforts. Monitoring the network to ensure that all systems are secured against vulnerabilities is essential to ongoing security efforts. Tenable’s extensive network monitoring capabilities can verify that systems are successfully scanned regularly and secured against vulnerabilities, enabling ongoing improvements to an organization’s security posture.
Chapter Description
The following chapters have been developed to provide a quick visual representation of the number of systems certain applications are installed on, the number of vulnerabilities, ratio of vulnerable systems, and percentage of systems that are currently exploitable. Vulnerability Trend displays application vulnerabilities over the last 90 days. The two remaining components provide a fast; at-a-glance summary that really puts how the organization stands into a quick perspective, continuing the format of quick visual data presentation without having to drill down to get into it. All fields are clickable for a deep dive analysis into the presented data.
- Executive Summary - This chapter contains components that present a visual overview of various defined technologies by row, and enumerates any found vulnerabilities across the columns. Included components present the number of critical, high, and medium vulnerabilities displayed across three columns, as well as the number of days they have been detected. The Database Trend presents a trend of the number of vulnerabilities by installed application over the last 90 days.
- Database Vulnerability Status Report - This chapter gives a quick status report on patching efforts. The number of critical, high, and medium vulnerabilities is displayed across three columns, as well as the number of days they have been detected.
- Database Critical Vulnerability Information - The Database Critical Vulnerability Information chapter displays the most critical vulnerabilities in a text format for a fast, readable reference without having to do a deep dive.
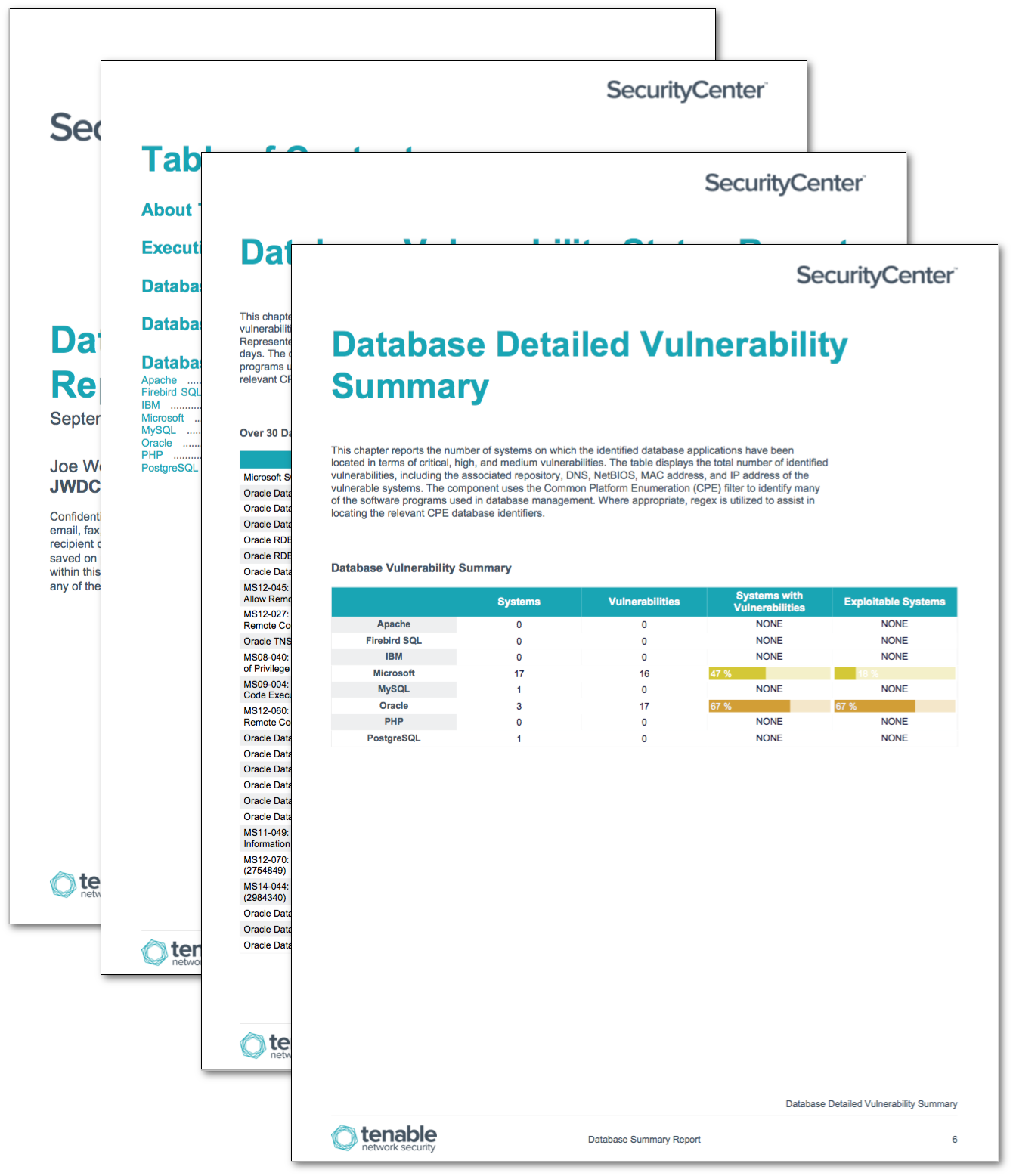
- Database Detailed Vulnerability Summary – This chapter reports the number of systems on which the technology has been located in terms of critical, high, and medium vulnerabilities. The tables display the total number of identified vulnerabilities, including the associated repository, DNS, NetBIOS, MAC address, and IP address of the vulnerable systems for each database application vendor.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success