by Cody Dumont
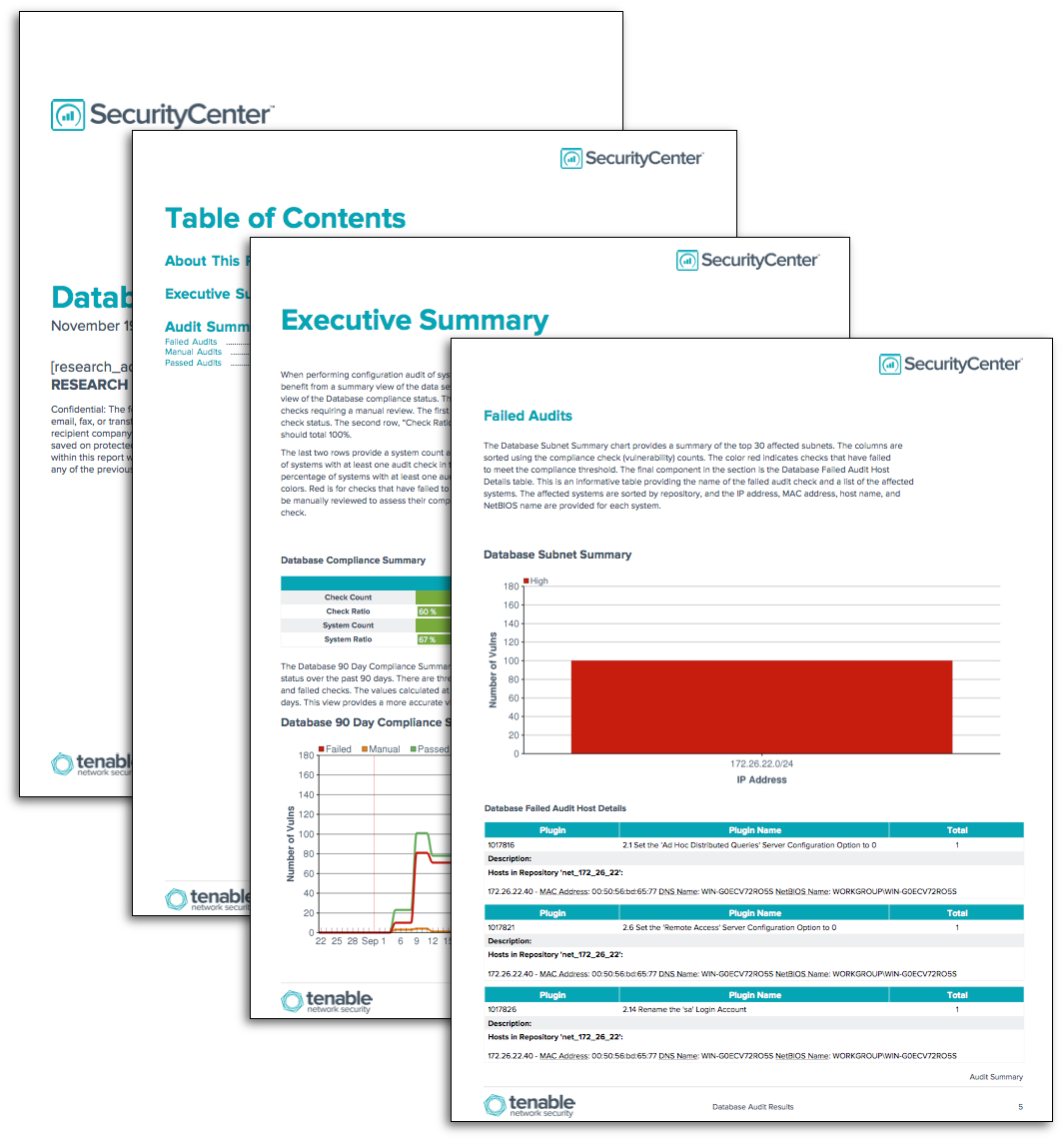
Governance, Risk Management, and Compliance is a substantial part of any information assurance program. The GRC requires information systems to be audited, regardless of the standard to which the audit is performed. This report provides the audit results for databases.
One of the initial steps in a successful GRC program is to set configuration guidelines and establish a supportable set of security policies. Tenable.sc CV can measure compliance, using audit files that cover a wide range of major regulations and other auditable standards. Tenable provides over 500 audit files, which are available for download from the Tenable Support Portal in categories such as operating systems, applications, databases, and network devices. Tenable products can be used to audit systems based on SCAP content, and many Tenable audit policies have been certified by the Center for Internet Security (CIS). For more information on using audit files, see the Nessus Compliance Checks: Auditing System Configurations and Content document.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The report requirements are:
- Tenable.sc 4.8.1
- Nessus 8.5.1
- Database Compliance Data
Tenable.sc Continuous View (CV) using Nessus has the ability to access the Application Programming Interfaces (APIs) used to audit systems running Relational Database Management Systems (RDMS). Nessus implements various APIs used to audit database systems, such as Microsoft SQL Server, Oracle, MySQL, PostgreSQL, DB2, and Informix. The audit checks include password, remote access, separate partitions for database files, server memory settings, and SA account locked down. Using an asset to identify specific systems running different RDMS can enhance this report. An example of how to add an asset to a report can be found in the following how-to guide: FindUpdateReportFilters-HowTo_v1.4.pptx
Audit files can be customized to match the values defined in an organization’s corporate policies. The organization can review several audit files and then create a specific audit file that applies directly its policies. When an audit is performed, for each individual compliance check, Nessus attempts to determine if the host is compliant, non-compliant, or if the results are inconclusive and need to be verified manually. Unlike a vulnerability check that only reports if the vulnerability is actually present, a compliance check always reports a result. This way, the data can be used as the basis of an audit report to show that a host passed or failed a specific test, or if it could not be properly tested.
Tenable.sc Continuous View (CV) is the market leader in providing a unique combination of vulnerability detection, compliance auditing, and reporting. Tenable.sc CV supports auditing more technologies than any other vendor including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. This makes Tenable.sc CV the market-defining continuous network monitoring platform, and Nessus the market-defining vulnerability scanning for auditors and security analysts.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success