by Cesar Navas
Vulnerable application development software can be exploited, increasing the threat landscape to an organization. Tenable.sc Continuous View (CV) (via Nessus Network Monitor, Log Correlation Engine, and Nessus) collects information about installed products, and identifies those products using standardized industry methods. Tenable.sc CV enumerates known application development software, such as VBScript, Xcode, and Java Development Kit. This report provides a quick visual representation of the number of systems certain development applications are installed on, the number of vulnerabilities, ratio of vulnerable systems, and percentage of systems that are currently exploitable. This information in this report can assist the analyst in the identification of vulnerable software, which potentially can give an attacker the ability to execute arbitrary code.
Application development software is software used to create and maintain applications and frameworks. Many times development systems and software are overlooked during the routine patching and update process of an organization’s workstations and servers. Vulnerable application development software can be exploited, increasing the threat landscape to an organization. Under certain circumstances, vulnerable libraries or components of these development applications can introduce vulnerabilities into software applications being developed, which can later be exploited. This information assists with the enforcement and verification of IT management policies relating to assets, such as vulnerability, configuration, and remediation policies.
The chapters in this report leverage data gathered by active vulnerability scanning with Tenable Nessus. Application development software vulnerability data is presented to the analyst via four chapters. The report uses the Common Platform Enumeration (CPE) filter to identify many of the software programs used in application development. According to NIST, the CPE is a structured naming scheme for information technology systems, software, and packages. Based upon the generic syntax for Uniform Resource Identifiers (URI), CPE includes a formal name format, a method for checking names against a system, and a description format for binding text and tests to a name. Tenable assigns CPE’s to plugins where appropriate. This allows for analysts to search for common CPE prefixes such as cpe:/a:apple:xcode, cpe:/a:oracle:jdk, and others. Associating CPE strings with vulnerabilities allow the analysts a greater view into separating operating system vulnerabilities from application vulnerabilities, and adds to the level of vulnerability detail provided to the organization.
This report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments. The report requirements are:
- Tenable.sc 5.3.1
- Nessus 8.5.0
Tenable.sc Continuous View (CV) provides extensive network monitoring by leveraging a unique combination of detection, reporting, and pattern recognition utilizing industry recognized algorithms and models. Tenable.sc CV is continuously updated to detect advanced threats and vulnerabilities. Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context and enabling decisive action that transforms the security program from reactive to proactive. Continuous vulnerability analysis enables security teams to more effectively tailor remediation efforts. Monitoring the network to ensure that all systems are secured against vulnerabilities is essential to ongoing security efforts. Tenable’s extensive network monitoring capabilities can verify that systems are successfully scanned regularly and secured against vulnerabilities, enabling ongoing improvements to an organization’s security posture.
The following chapters are included in this report:
- Executive Summary – This chapter contains a trend component, which displays application vulnerabilities over the last 90 days. An additional matrix providing a fast, at-a-glance summary that demonstrates the effectiveness of the current patching and remediation policies.
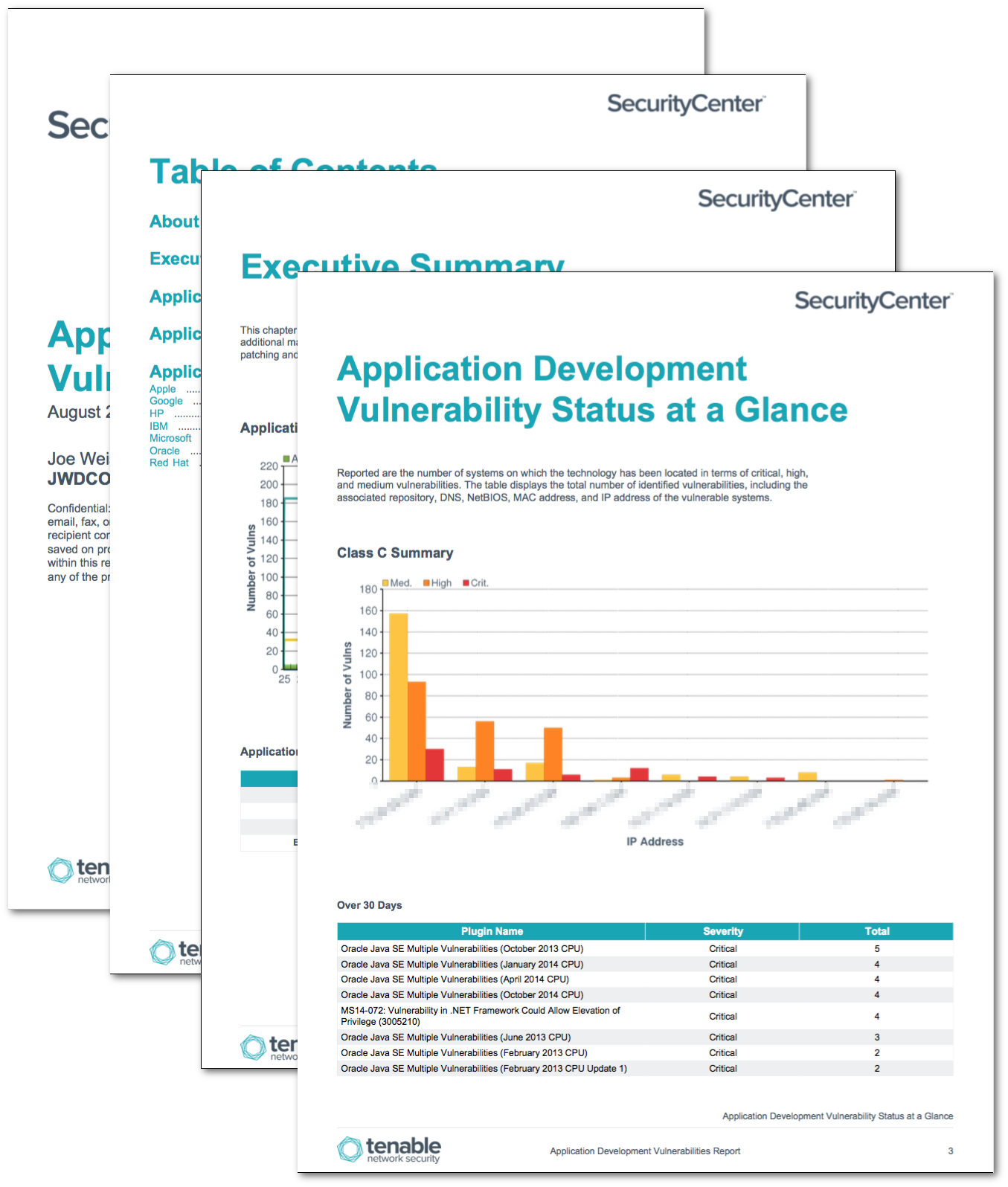
- Application Development Detailed Vulnerability Summary – Reported are the number of systems on which the technology has been located in terms of critical, high, and medium vulnerabilities. The table displays the total number of identified vulnerabilities, including the associated repository, DNS, NetBIOS, MAC address, and IP address of the vulnerable systems.
- Application Development Vulnerability Status at a Glance – This chapter gives a quick status report on patching efforts. The number of critical, high, and medium vulnerabilities is displayed across three columns, as well as the number of days they have been detected. Represented are known vulnerabilities that have existed for: Over 30 Days, the Last 30 Days, or the Last 7 Days.
- Application Development Critical Vulnerability Information – This chapter reports the most critical vulnerabilities for a fast, readable reference to the most significant concerns. The total number of critical vulnerabilities displayed is sorted on vulnerability count, from highest to lowest.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success