by Cesar Navas
Identifying weaknesses in a network is an ongoing challenge that security teams face. Account vulnerabilities can provide attackers with easier access to an otherwise secure network. Finding weaknesses in the configuration of accounts is a key step to properly securing any network. By leveraging the capabilities of Tenable.sc, Nessus, and the Nessus Network Monitor (NNM), security teams can easily identify vulnerable accounts and tailor their remediation efforts accordingly.
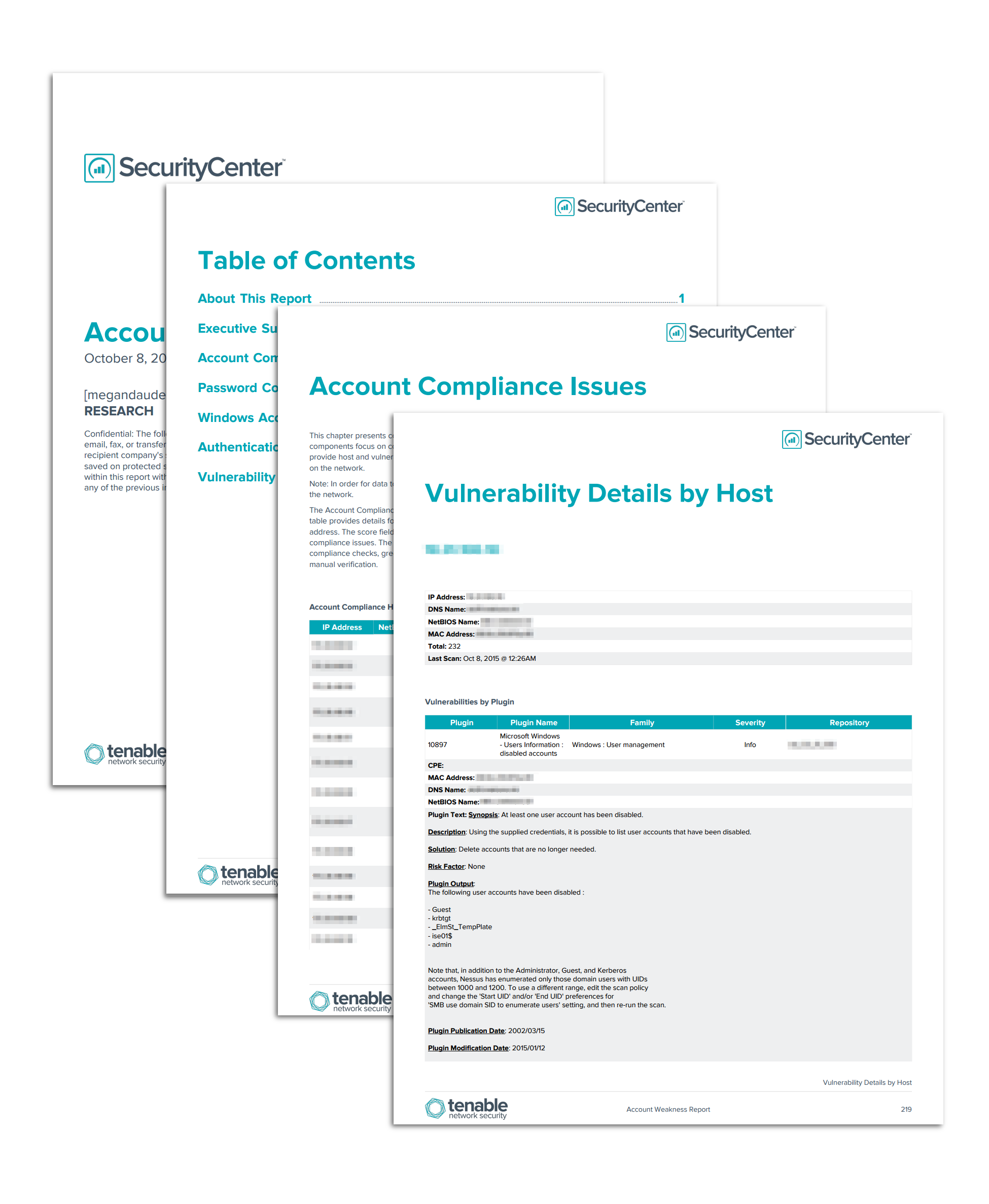
The Account Weakness Report assists security analysts in identifying the vulnerable accounts that are present on the network so that remediation efforts can be adjusted as needed. Plugin name filters are used along with 46 authentication- and account-related plugins to gather the data presented in this report. Detected vulnerabilities are correlated in order to provide details about the affected hosts. This report provides detailed documentation about the account weaknesses on an organization’s network.
The chapters in this report provide several views of the various types of account weaknesses. Compliance concerns with accounts and passwords are addressed, as well as issues with authentication and Windows account vulnerabilities. Each chapter uses components to provide extensive details on the vulnerabilities detected and the affected hosts. Security teams can use the information in these chapters to understand specific details about affected hosts, detected vulnerabilities, plugins used, and recommended solutions.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments. The report requirements are:
- Tenable.sc 4.8.2
- Nessus 8.5.1
- NNM 5.8.1
Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. Nessus Network Monitor (NNM) performs deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. By integrating with Nessus and NNM, Tenable.sc CV’s continuous network monitoring is able to detect threats and vulnerabilities across the enterprise.
This report contains the following chapters:
- Executive Summary: This chapter provides an overview of the account weaknesses covered in the report.
- Account Compliance Issues: This chapter presents compliance information based on account-related compliance checks.
- Password Compliance Issues: This chapter presents compliance information based on password-related compliance checks.
- Windows Account Vulnerabilities: This chapter presents active detections of Windows account vulnerabilities in several different areas.
- Authentication Vulnerabilities: This chapter presents active and passive detections of authentication vulnerabilities in several different areas.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success