by Cody Dumont
Many organizations attempt to proactively identify and patch every potential cybersecurity vulnerability in order to be protected from all known vectors of attack. However, with numerous vulnerabilities emerging daily, this goal is difficult to achieve. Tenable.sc is able to help prioritize mitigation efforts and help the organization understand the likelihood a given vulnerability will be exploited by using a combination of machine learning and threat intelligence to deliver the new Vulnerability Priority Rating (VPR). In 2017, 15,038 new Common Vulnerability and Exposures (CVEs) were published, up from 9,837 in 2016 – an alarming 53% increase. In 2018, there were 16,500 new CVEs. Since the average enterprise finds 870 CVEs across 960 IT assets every single day, patching all vulnerabilities just isn’t practical. Organizations must reduce the problem set to a manageable size. Many organizations use the Common Vulnerability Scoring System (CVSS) to rank what should be patched. However, CVSS is limited in its ability to aid operational effectiveness. Instead, businesses need to know the difference between vulnerabilities representing theoretical versus actual risk – and then prioritize those vulnerabilities according to the risk level they pose.
Tenable’s Research and Data Science teams have authored a new research technology called the Vulnerability Priority Rating (VPR) using a machine learning based approach called Predictive Prioritization. This dashboard helps to present vulnerability data using VPR scores compared to the Common Vulnerability Scoring System (CVSS) scores. This approach allows management and security professionals to focus prioritization efforts on those vulnerabilities with the biggest impact to their organization, thereby reducing their attack surface and minimizing risk.
VPR uses a machine learning algorithm coupled with threat intelligence to analyze every vulnerability ever published in NVD (approx. 111,000 to date), Predictive Prioritization builds on CVSS to: 1) anticipate the probability of a vulnerability being leveraged by threat actors, and 2) differentiate between real and theoretical risks. This first-of-its-kind innovation provides security teams with the unprecedented capability to tighten their focus and remediate the vulnerabilities that pose the greatest business risk.
The dashboard and components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Security Industry Trends.
The dashboard requirements are:
- Tenable.sc 5.9
- Nessus 8.4.0
Tenable.sc Continuous View® (Tenable.sc CV™) provides continuous network monitoring, vulnerability identification, and Predictive Prioritization technology. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and Vulnerability Priority Rating using advanced data science techniques to predict which threats are the most likely to allow attackers to penetrate the network. Tenable’s Data Science and Research teams are constantly analyzing information from our unique sensors and deliver continuous visibility into the risk management efforts of the organization enabling decisive action that transforms a security program from reactive to proactive. By scanning the network using active and agent base methods the security team can examine applications on the systems, the running processes and services, web applications, and configuration settings. Analysts now have a new tool to assist in the continuous battle against malicious actors.
Listed below are the components included with this dashboard.
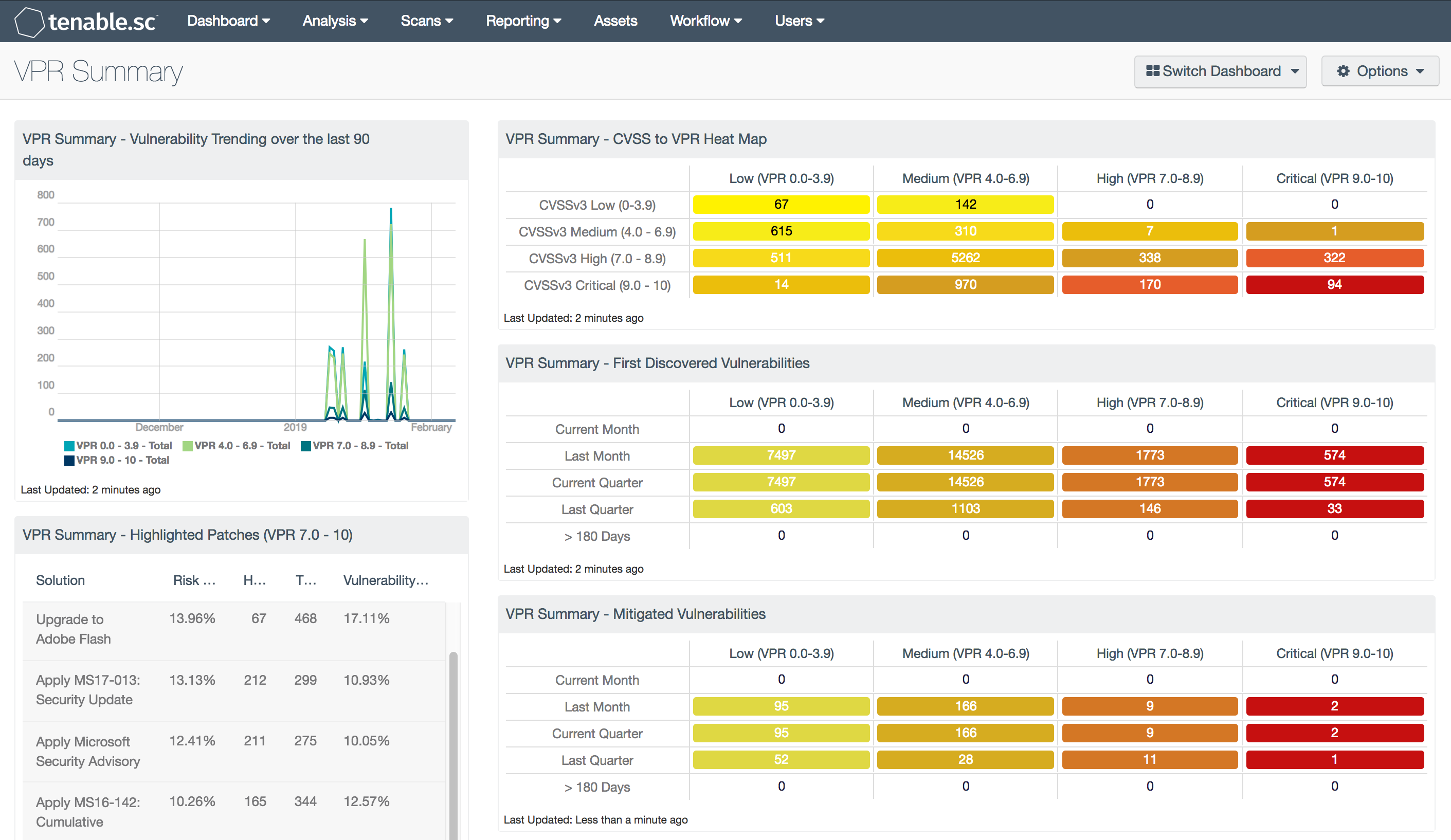
VPR Summary - Vulnerability Trending over the last 90 days
This component contains a trend analysis for each of the VPR levels: low (VPR 0-3.9), medium (VPR 4.0-6.9), high (VPR 7.0-8.9) and critical (VPR 9.0 - 10) over the past 90 days. Each line in the chart uses the Vulnerability Last Observed filter to allow the analysts to observe changes from day to day. As you move the mouse over the lines, you will see data points, with Vulnerability Last Observed filter the query between the data points will highlight the change from day-to-day. If the scanning strategy is to scan every 7 days, the graph will show spikes every seven days. However, if the organization is scanning daily, then a more accurate view of the trend data will be displayed, as the daily changes are shown.
VPR Summary - Highlighted Patches (VPR 7.0 - 10)
The component uses the High and Critical VPR levels (VPR 7.0 - 10) combined with the remediation summary tool to provide a focused view of patches that should be considered at a higher priority than other patches. The tool provides a list of patches to apply, the amount of risk reduced (based on vulnerability weight score), hosts affected, and percentage of vulnerabilities. Using Predictive Prioritization, organizations are able to better understand which vulnerabilities should be mitigated first. Combined with this comprehensive view Tenable.sc provides the list of patches that can have the more immediate impact.
VPR Summary - CVSS to VPR Heat Map
This component provides a correlation between CVSSv3 scores and VPR scoring for the vulnerabilities present in the organization. The CVSSv3 scores are the traditional method of analyzing risk, while VPR is a new method based on data science analysis and threat modeling. Each cell is comprised of a combination of cross-mapping of CVSS & VPR scoring. Using a heat map approach, the filters begin in the left upper corner with vulnerabilities with the least risk. Moving to the right and lower down the matrix the colors change darker from yellow to red as the risk levels increase. Customers should mitigate risks in the lower right corners, and then work towards the upper left cells.
VPR Summary - VPR First Discovered
This component provides organizations with a view of vulnerabilities over a period of time. The columns are grouped using the VPR score levels, ranging from least risk to the greatest risk. Each row uses the Vulnerability First discovered filter to track when a risk first appeared on the network. The rows progress from the current month, last month, current quarter, last quarter, to vulnerabilities first discovered over 180 days ago. Most SLA’s allow for the vulnerability to exist on the network for 30 days, due to a standard 30-day patch cycle. Organizations can modify this matrix to support the SLA as defined by their risk management officer.
VPR Summary - VPR Mitigated Vulnerabilities
This component provides organizations with a view of vulnerabilities that have been mitigated, showing progress towards risk management SLA’s. The columns are grouped using the VPR score levels, ranging from least risk to the greatest risk. Each row uses the Vulnerability Mitigated filter to track when a risk first appeared on the network. The rows progress from the current month, last month, current quarter, last quarter, to vulnerabilities first discovered over 180 days ago. Most SLA’s allow for the vulnerability to exist on the network for 30 days, due to a standard patch cycle. Organizations can modify this matrix to support the SLA as defined by their risk management officer.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success