Risk is the potential that a threat will exploit a vulnerability to cause harm to an organization. Risk management involves determining those risks with the greatest impact and greatest probability of occurring, and handling those first. If an organization does not properly manage risk, they may incur substantial losses because they focus their mitigation efforts in the wrong areas.
This dashboard can assist an organization in understanding and managing their risk. The components in this dashboard identify vulnerabilities on the network and present details to assist the organization in understanding the risks the vulnerabilities might present. This information will then enable the organization to focus mitigation efforts in the correct areas.
One aspect of risk management is deciding which risks the organization can safely accept. Tenable’s Tenable.sc Continuous View (CV) provides a way for an organization to mark a vulnerability as an ‘accepted risk’. This dashboard focuses on assisting the organization in understanding and managing the risks it has accepted.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments.
The dashboard requirements are:
- Tenable.sc 4.8.1
- Nessus 8.6.0
- LCE 6.0.0
- NNM 5.9.0
For a related Tenable.sc dashboard, see the Understanding Risk dashboard.
Tenable.sc Continuous View (CV) provides the organization with the most comprehensive and integrated view into risk analysis available. With native ability to detect more vulnerabilities than the competition, Tenable.sc CV has the ability to analyze risk across many systems, and assist the organization in properly mitigating and managing risk.
Listed below are the included components:
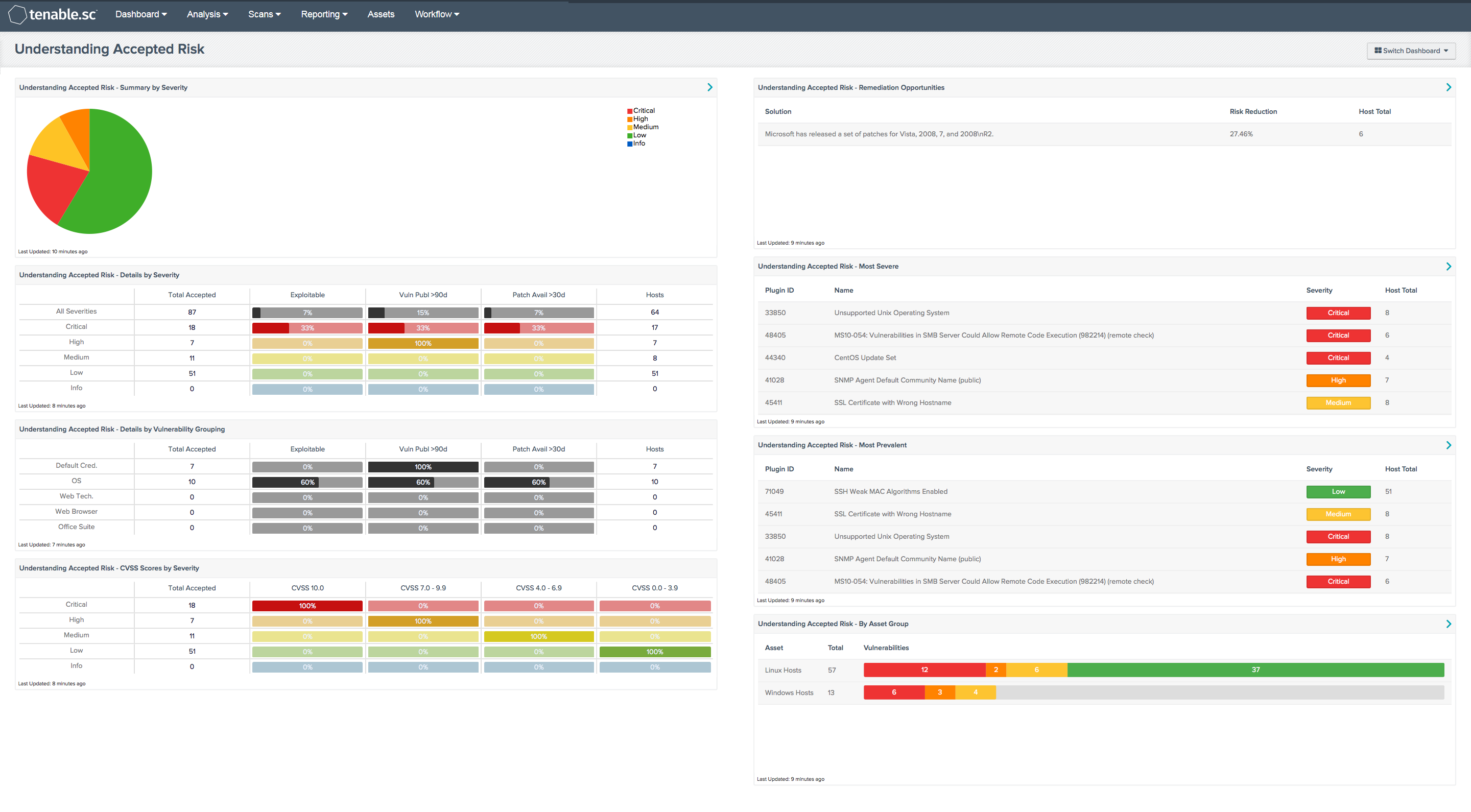
- Understanding Accepted Risk - Summary by Severity - This pie chart provides a visual depiction of current vulnerabilities found to exist in the environment that have been marked as accepted risks.
- Understanding Accepted Risk - Details by Severity - This matrix presents details by severity on vulnerabilities found to exist in the environment that have been marked as accepted risks. At each severity level, the number of vulnerabilities is displayed, along with three percentage columns and the number of hosts affected. The percentage columns show the percentages of the vulnerabilities that are exploitable, that were published more than 90 days ago, and that have had a patch available for more than 30 days. If more details are desired (for example, what are the specific critical vulnerabilities that are exploitable?), click on the appropriate matrix cell to display more information. Of particular interest for accepted risk are those vulnerabilities published more than 90 days ago; this may be a good indication of those vulnerabilities that have been accepted for a long time and which may need to be reviewed.
- Understanding Accepted Risk - Details by Vulnerability Grouping - This matrix presents details by vulnerability grouping on vulnerabilities found to exist in the environment that have been marked as accepted risks. For each vulnerability grouping, the number of vulnerabilities is displayed, along with three percentage columns and the number of hosts affected. The percentage columns show the percentages of the vulnerabilities that are exploitable, that were published more than 90 days ago, and that have had a patch available for more than 30 days. If more details are desired (for example, what are the specific critical vulnerabilities that are exploitable?), click on the appropriate matrix cell to display more information. Some important vulnerability groupings are given, including default credential vulnerabilities, OS vulnerabilities, web technology (Java, Flash, PHP, etc.) vulnerabilities, web browser vulnerabilities, and office suite vulnerabilities. Most of these groupings are based on Common Platform Enumeration (CPE) strings. If desired, more vulnerability groupings can be added. Of particular interest for accepted risk are those vulnerabilities published more than 90 days ago; this may be a good indication of those vulnerabilities that have been accepted for a long time and which may need to be reviewed.
- Understanding Accepted Risk - CVSS Scores by Severity - This matrix presents Common Vulnerability Scoring System (CVSS) information by severity on vulnerabilities found to exist in the environment that have been marked as accepted risks. CVSS is an open industry standard for assessing the severity of computer system security vulnerabilities; it attempts to establish a measure of how much concern a vulnerability warrants, compared to other vulnerabilities, so efforts can be prioritized. The scores range from 0 to 10. Vulnerabilities with a base score in the range 7.0-10.0 are critical, those in the range 4.0-6.9 are major, and those in the range 0.0-3.9 are minor. The CVSS scores correspond to the Tenable severity levels as follows: 10.0 = Critical severity, 7.0-9.9 = High, 4.0-6.9 = Medium, and 0.0-3.9 = Low. At each severity level, the number of vulnerabilities is displayed, along with the percentages of those vulnerabilities in each CVSS score grouping.
- Understanding Accepted Risk - Remediation Opportunities - This table displays the top remediations for the network, considering only those vulnerabilities that have been marked as accepted risks. For each remediation, the risk reduction for the network if the remediation is implemented is shown, along with the number of hosts affected. The table is sorted so that the highest risk reduction is at the top. Implementing the remediations, if possible, will decrease the overall vulnerability of the network.
- Understanding Accepted Risk - Most Severe - This table presents the most severe vulnerabilities found to exist in the environment that have been marked as accepted risks. The table is sorted so that the most severe vulnerability is at the top.
- Understanding Accepted Risk - Most Prevalent - This table presents the most prevalent vulnerabilities found to exist in the environment that have been marked as accepted risks. The table is sorted so that the vulnerability found on the most hosts is at the top.
- Understanding Accepted Risk - By Asset Group - This table presents a summary by asset grouping of vulnerabilities found to exist in the environment that have been marked as accepted risks. The table is sorted so that the most vulnerable asset group is at the top. This table can be used to determine which asset groups have the most accepted risk.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success