Organizations use patch management systems to monitor systems, install software, and patch systems on a network. Using these solutions, organizations can automate the deployment of new software installations and patch systems across the network with ease. Unfortunately, some solutions may not account for vulnerabilities on stand-alone and isolated systems, or systems that connect intermittently. Failure to account for vulnerabilities on devices and systems missed by patch management solutions can lead to increased risks for the organization. This dashboard presents a summary of vulnerabilities reported by Symantec Altiris, which can be used to determine whether vulnerabilities are being patched effectively.
Symantec Altiris is a patch management solution that supports a wide range of platforms including Windows, Linux, Unix, and macOS-based systems. This solution provides an effective way to manage and patch systems; however, Altiris may not account for vulnerabilities on laptops, mobile phones, virtualized systems, and others devices that connect in between patch cycles. Using Tenable's Tenable.sc Continuous View (CV), organizations will obtain the additional coverage needed to identify vulnerabilities on systems that patch management solutions may not be aware of. Once all assets are accounted for, administrators can identify and correct issues with existing patch management efforts. By leveraging Tenable.sc CV’s ability to continuously scan the network, organizations can establish an effective strategy to maintain an acceptable patch level.
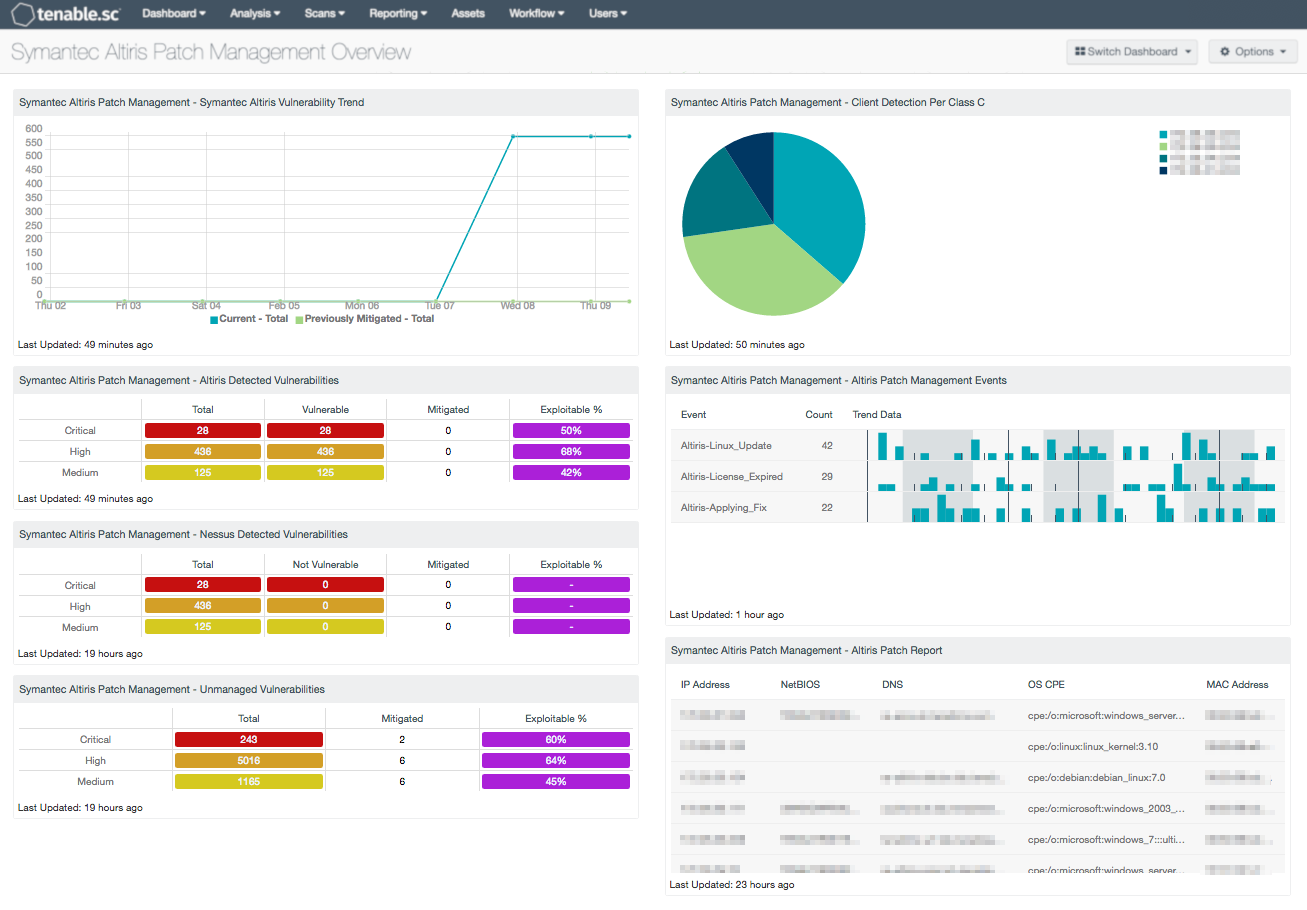
The Symantec Altiris Management Overview dashboard provides a comprehensive look at Microsoft Security Bulletin vulnerabilities detected by Altiris. Vulnerability data collected by Nessus can be used to determine whether Altiris is reporting any outdated or inaccurate information from managed hosts. Systems are scanned to identify managed clients and event data. Patch reports are collected from managed hosts that will provide analysts with a full summary of hotfixes, security advisories, and other patches that need to be applied. Data will also report on hosts not communicating properly or that may have fallen out of scope. Organizations can use the information provided within this dashboard to strengthen overall network security and improve patch management efforts.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Discovery & Detection. The dashboard requirements are:
- Tenable.sc 5.4.2
- Nessus 8.5.1
- LCE 6.0.0
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution that will assist in monitoring patch management solutions. Tenable.sc CV is continuously updated to detect advanced threats and vulnerabilities. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns on network assets. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Host data and data from other security products is analyzed to monitor events captured from patch management solutions on the network. Tenable.sc CV provides an organization with the most comprehensive view of the network and the intelligence needed to support proactive patch management efforts.
The following components are included within this dashboard:
- Symantec Altiris Patch Management - Altiris Vulnerability Trend: This chart presents a trend of both current and previously mitigated vulnerabilities reported by Symantec Altiris over the last seven days. Information presented within this component can provide organizations with a comprehensive view into how often systems are being scanned, patched, and rescanned. The “Current” trend line will report on the number of vulnerabilities collected from Altiris using the “Never Mitigated” filter. The “Previously Mitigated” trend line includes the number of vulnerabilities that have moved from the mitigated section to the active section. Previously Mitigated or recurring vulnerabilities can be the result of systems not being restarted after a patch was applied, virtual systems reverting to previous snapshots, or services that were disabled or failed to restart. Organizations can use this component to focus efforts on remediating both current and previously mitigated vulnerabilities.
- Symantec Altiris Patch Management – Altiris Detected Vulnerabilities: This component provides a summary of Microsoft vulnerabilities detected by Symantec Altiris. The rows include vulnerabilities at each severity level discovered within the Windows: Microsoft Bulletins Plugin Family. The columns include the total number of vulnerabilities discovered, number of vulnerabilities discovered by Nessus that Altiris is reporting as vulnerable, number of mitigated vulnerabilities, and percentage of exploitable vulnerabilities. Information presented within this component can be used to discover whether vulnerabilities are being patched in a timely manner through Altiris. This data can also be used to identify any systems reporting outdated vulnerability information.
- Symantec Altiris Patch Management – Nessus Detected Vulnerabilities: This component provides a summary of Microsoft vulnerabilities detected by Nessus that have been reported as not vulnerable by Altiris. The rows include vulnerabilities at each severity level discovered within the Windows: Microsoft Bulletins Plugin Family. The columns include the total number of vulnerabilities discovered by Altiris, number of vulnerabilities discovered by Nessus that Symantec Altiris is reporting as not vulnerable, number of mitigated vulnerabilities, and percentage of exploitable vulnerabilities. Information presented within this component can be used by the analyst to identify how often systems are being patched by Altiris, and whether current security settings need to be modified.
- Symantec Altiris Patch Management – Unmanaged Vulnerabilities: This component provides a summary of vulnerabilities detected by Nessus on hosts not managed by patch management systems. The rows include vulnerabilities at each severity level discovered within the Windows: Microsoft Bulletins Plugin Family. The columns include the total number of vulnerabilities discovered on unmanaged systems, number of mitigated vulnerabilities, and percentage of exploitable vulnerabilities. This matrix provides targeted information analysts need to compare the effectiveness of patch management efforts, and whether current security settings need to be modified.
- Symantec Altiris Patch Management - Client Detection Per Class C: This chart presents a Class C summary of hosts managed by Symantec Altiris. Nessus actively scans hosts to determine whether Altiris clients are installed. Using this component, analysts will be able to determine how much of the network is covered by Symantec Altiris. Information collected through active scanning will detect hosts managed by Altiris. By drilling down, analysts can obtain additional information on managed hosts, and can be used to identify hosts may not be fully patched or included in the patch management process.
- Symantec Altiris Patch Management – Altiris Patch Management Events: This component includes a summary of events reported by Symantec Altiris over the last 72 hours. The list is ordered so that events reported most often from Altiris are at the top. Log events from Altiris are forwarded to the LCE server. LCE can detect changes in patch management solutions that analysts can monitor to determine if further action is needed. Event data in this component may include information on packages being downloaded, patch installation errors, and systems restarts. Analysts can modify this component to include specific normalized events per organizational requirements.
- Symantec Altiris Patch Management – Altiris Patch Report: This table presents a list of hosts managed by Symantec Altiris where a patch report summary has been collected. Other components within this dashboard report on Microsoft Bulletin vulnerabilities on Windows hosts managed by Altiris. Using Nessus plugin 76869, this component will provide a full summary of missing patches from managed systems. By clicking on the Browse Component Data icon and changing the tool to Vulnerability Detail List, analysts will obtain a full summary of hotfixes, security advisories, and other patches that need to be applied. Data will also report on hosts not communicating properly or that may have fallen out of scope. Using this information, analysts will obtain the critical context needed to strengthen remediation efforts within the organization.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success