by Josef Weiss
The DoD uses STIG audits to analyze risk and identify configuration vulnerabilities, as part of the proper IA controls. This collection presents the analyst with vulnerability data utilizing STIG Severity Codes in an easy to understand method. Pass/Fail compliance related audit data is located in SecurityCenter by either MAC or CAT Level code identification.
A Security Technical Implementation Guide or STIG is a methodology for standardized secure installation and maintenance of computer software and hardware. The term was coined by DISA, which creates configuration documents in support of the United States Department of Defense (DoD). The implementation guidelines include recommended administrative processes and span the devices' lifecycle.
The DISA STIG assigns a Severity Code to each system IA security weakness to indicate the risk level associated with the IA security weakness and the urgency with which the corrective action must be completed.
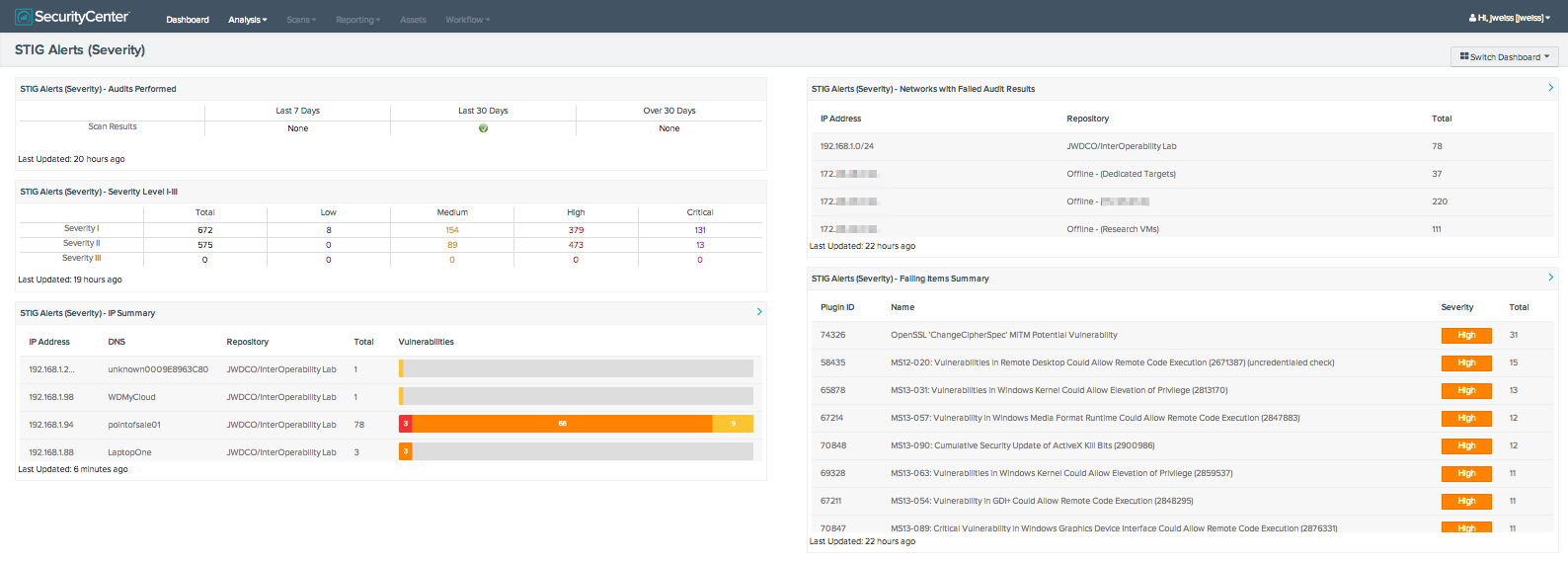
This collection presents the analyst with vulnerability information within the environment. Data is presented on the number of STIG Severity vulnerability concerns, networks that have STIG vulnerability results, when audits have been performed, IP summary, and a failing items STIG vulnerability summary.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments.
The dashboard requirements are:
- SecurityCenter 4.7
- Nessus 5.2.7
SecurityCenter Continuous View (CV) allows for the most comprehensive and integrated view of network health. SecurityCenter CV provides a unique combination of detection, reporting, and pattern recognition utilizing industry recognized algorithms and models. SecurityCenter CV also enables the analyst to react to advanced threats, zero-day vulnerabilities, and new forms of regulatory compliance.
The collection contains the following components:
- STIG Alerts (CAT) – Audits Performed - This components displays and indication of STIG Nessus scans present over the last 7, 30, or over 30 days. The component contains regex filters that look for CAT compliance results (pass or fail) that are of a specified age. An icon is displayed in the appropriate column if results are found, displaying a green check for any results found within the time frame. If no results are found, “None” is displayed in the column.
- STIG Alerts (Severity)– DISA Severity Level I-III - This component displays vulnerability results for all STIG Severity Levels (I, II, and III). A Severity Code is assigned to each system security weakness to indicate the associated risk level. The Severity Level can assist in determining the urgency with which the corrective action must be completed. The component provides indication if vulnerability results exist for the specified Severity level, the total number of vulnerabilities found, and vulnerability counts in regard to Low, Medium, High, and Critical levels.
- STIG Alerts (Severity) – Networks with Failed Audit Results - This component displays data on Class C networks that contain vulnerability results for STIG Severity Levels. The Class C network, repository, and total number of vulnerability results are displayed to the analyst. This allows the analyst to determine which Class C networks contain STIG vulnerability results, and the total counts of those results.
- STIG Alerts (Severity) – IP Summary - This component displays to the analyst an IP Summary of STIG vulnerability Severity Levels, vulnerabilities, and total counts. The component utilizes the IP Summary tool with a filter for the term for STIG Severity results, with filters for vulnerability severity results. This allows the analyst to view STIG vulnerability results quickly for a specific IP address or host name.
- STIG Alerts (Severity) – Failing Items Summary - This table component utilizes the vulnerability summary tool to display STIG vulnerability Severity Levels. Displayed are the reported vulnerabilities, sorted by count. The top 10 items are displayed, and allows the analyst to quickly determine which STIG Severity Level vulnerabilities are the most prevalent within the environment.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success