by Cesar Navas
The Payment Card Industry Security Standards Council (PCI SSC) maintains, evolves, and promotes Payment Card Industry standards for the safety of cardholder data across the globe. The PCI SSC provides organizations with technical and operational requirements for organizations accepting or processing payment transactions, and for software developers and manufacturers of applications and devices used in those transactions.
The Payment Card Industry Data Security Standard (PCI DSS) helps entities understand and implement standards for security policies, technologies, and ongoing processes that protect their payment systems from breaches and theft of cardholder data. The standards have historically been revised on a 2-3 year cycle, but the PCI SSC is transitioning to a posture of revising the PCI DSS as required based on changes to the current threat landscape. The current standard revision is PCI DSS Version 3.2 released in April 2016. Any organization that handles payment card information has to comply with the PCI DSS and must demonstrate compliance annually. Tenable's Tenable.sc Continuous View (CV) is able to help organizations monitor ongoing PCI DSS compliance by integrating with Tenable Nessus, Tenable Nessus Network Monitor (NNM), and Tenable Log Correlation Engine (LCE).
In order to effectively defend the organization from all threats internal and external, security teams should implement PCI DSS security efforts into their “business-as-usual” activities. Doing so will enable organizations to monitor the effectiveness of their security controls on an ongoing basis while also maintaining their PCI DSS compliance status between assessments. Tenable has products such as Tenable.sc CV, NNM, and LCE to assist analysts with a continuous and up-to-date view of the organization. This dashboard contains components that provide analysts a continuous and accurate view into the organization.
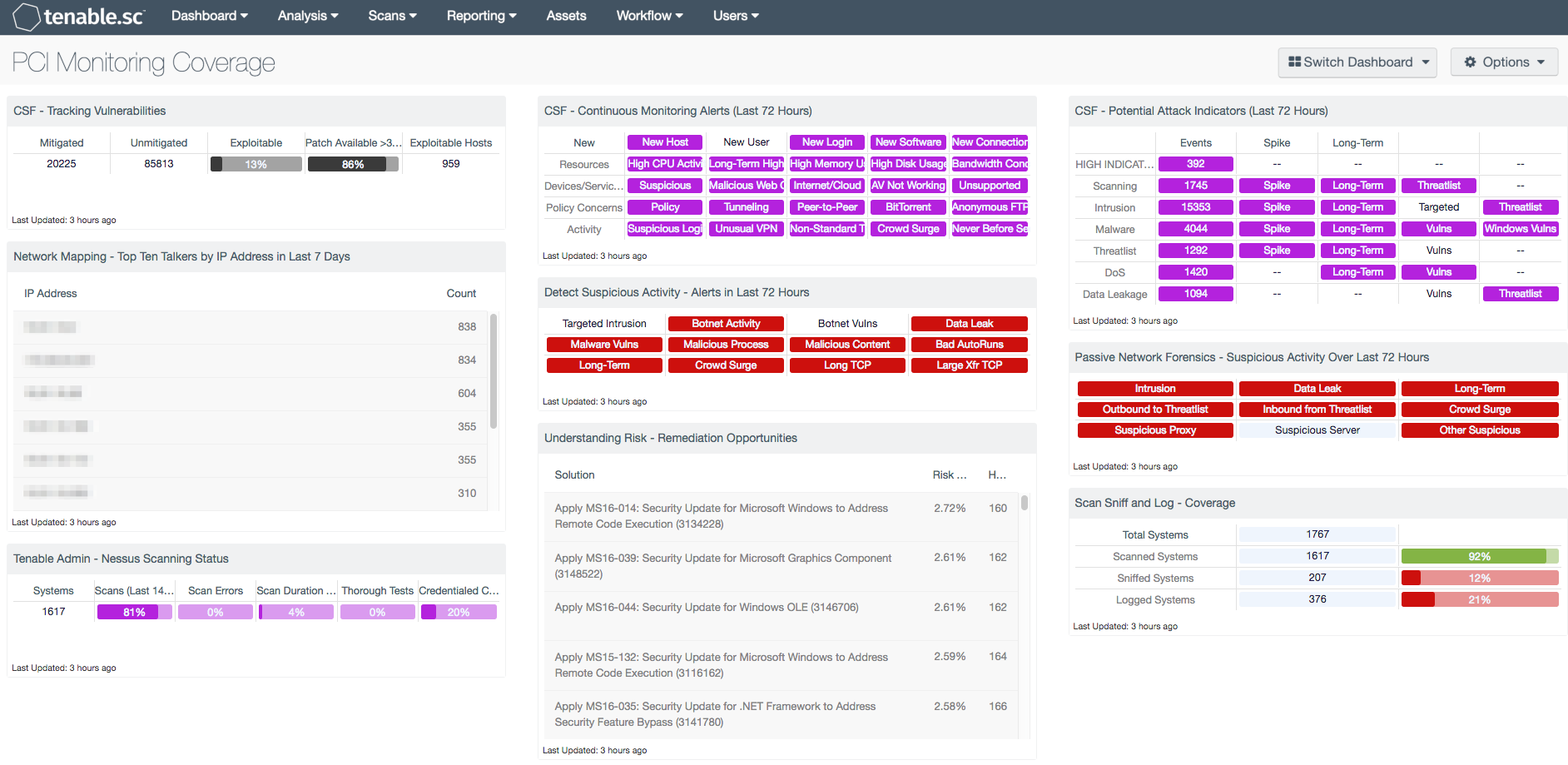
With this dashboard, organizations can assess their level of adherence with PCI requirements focusing on monitoring coverage of vulnerability scanning. The components in this dashboard are focused on PCI requirements 10, “Track and monitor all access to network resources and cardholder data” and 11, “Regularly test security systems and processes”. The components in this dashboard cover requirements such as 5.1, 10.3, 10.6, 11.1, 11.2, and 11.4 that focus on continuous monitoring indicators detected in the organization.
The components in the dashboard help analysts to take control of the noise in the organization and pare down everything happening to relevant and concise data points. Analysts have detailed matrix components that provide indicators of different potential attacks and events relating to malicious activity. Once these indicators turn purple, analysts can easily drill down into the cell to investigate the activity behind the indicator. Events relating to these indicators include malware being detected in the organization, NNM picking up events relating to activities in the “threatlist” family, and high CPU activity. Different parts of these components alone may not seem like an issue when first seen without correlation to other events. However, when these events are grouped together with more context of the organization along with Tenable products, these events can be better interpreted and show the overall threat to the organization.
Organizations can configure repositories or asset lists in order to tailor the focus of the dashboard. When the dashboard is added from the Tenable.sc Feed, the appropriate assets, IP addresses, or repositories can be specified. Assigning one of the options to the dashboard will update all filters in the components. By creating static or combination asset lists that include all systems in the Cardholder Data Environment (CDE), each component can be filtered to display results directly related to ongoing PCI security. Using an asset list filter will also allow traffic into and out of the CDE to be monitored. In order to accurately measure an organization’s PCI security posture, asset lists need to be applied as filters to provide results focused on the CDE.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessments. The dashboard requirements are:
- Tenable.sc 5.3.1
- Nessus 8.5.1
- NNM 5.9.0
- LCE 6.0.0
Tenable's Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable.sc is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. Tenable Nessus Network Monitor (NNM) performs deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. Tenable Log Correlation Engine (LCE) performs deep log analysis and correlation to continuously discover and track systems, applications, cloud infrastructure, trust relationships, and vulnerabilities. By integrating with Nessus, NNM, and LCE, Tenable.sc CV’s continuous network monitoring is able to detect systems and vulnerabilities across the enterprise.
This dashboard contains the following components:
- CSF - Tracking Vulnerabilities: This matrix assists in tracking actively and passively discovered vulnerabilities, including total mitigated vulnerabilities, total unmitigated vulnerabilities, the percent of vulnerabilities that are exploitable, the percent of vulnerabilities that have a patch available, and the number of hosts on the network that have exploitable vulnerabilities.
- Network Mapping - Top Ten Talkers by IP Address in Last 7 Days: This table presents host information for the top ten most active systems on the network in the last seven days based on the number of network traffic events generated.
- Tenable Admin - Nessus Scanning Status: This matrix component displays status information from Nessus scanners.
- CSF - Continuous Monitoring Alerts (Last 72 Hours): This matrix displays alerts for network activity over the last 72 hours that may be suspicious or of interest, such as new devices, users, software, etc., high resource usage, suspicious devices, use of Internet or cloud services, potential policy concerns, anonymous FTP detection, suspicious or never before seen activity, and more.
- Detect Suspicious Activity - Alerts in Last 72 Hours: This matrix presents warning indicators for potentially suspicious network activity detected in the last 72 hours.
- Understanding Risk - Remediation Opportunities: This table displays the top remediations for the network.
- CSF - Potential Attack Indicators (Last 72 Hours): This matrix displays alerts for network activity over the last 72 hours that may indicate attacks against the network.
- Passive Network Forensics - Suspicious Activity Over Last 72 Hours: This matrix presents indicators of suspicious events that have occurred in the last 72 hours, including intrusions, potential data leaks, potentially unwanted long-term activity, threatlist activity, crowd surges, suspicious proxy activity, suspicious server activity, and other suspicious host activity.
- Scan Sniff and Log - Coverage: This matrix presents the total number of systems, along with the total number of scanned, sniffed, or logged systems and corresponding percentages.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success