The National Information Assurance (NIA) Policy v2.0 is associated with the State of Qatar’s Ministry of Transport and Communications (MOTC). This policy was developed to help agencies and entities in the State of Qatar enable a full-fledged information security management system within their agency. These entities need to show compliance with the NIA Policy v2.0 through an annual audit by a certification body. This policy includes a series of security governances and technical controls, grouped into security domains that cover control areas that an agency needs to implement as baseline security to be compliant with the NIA Policy and in accordance with the NIA Manual.
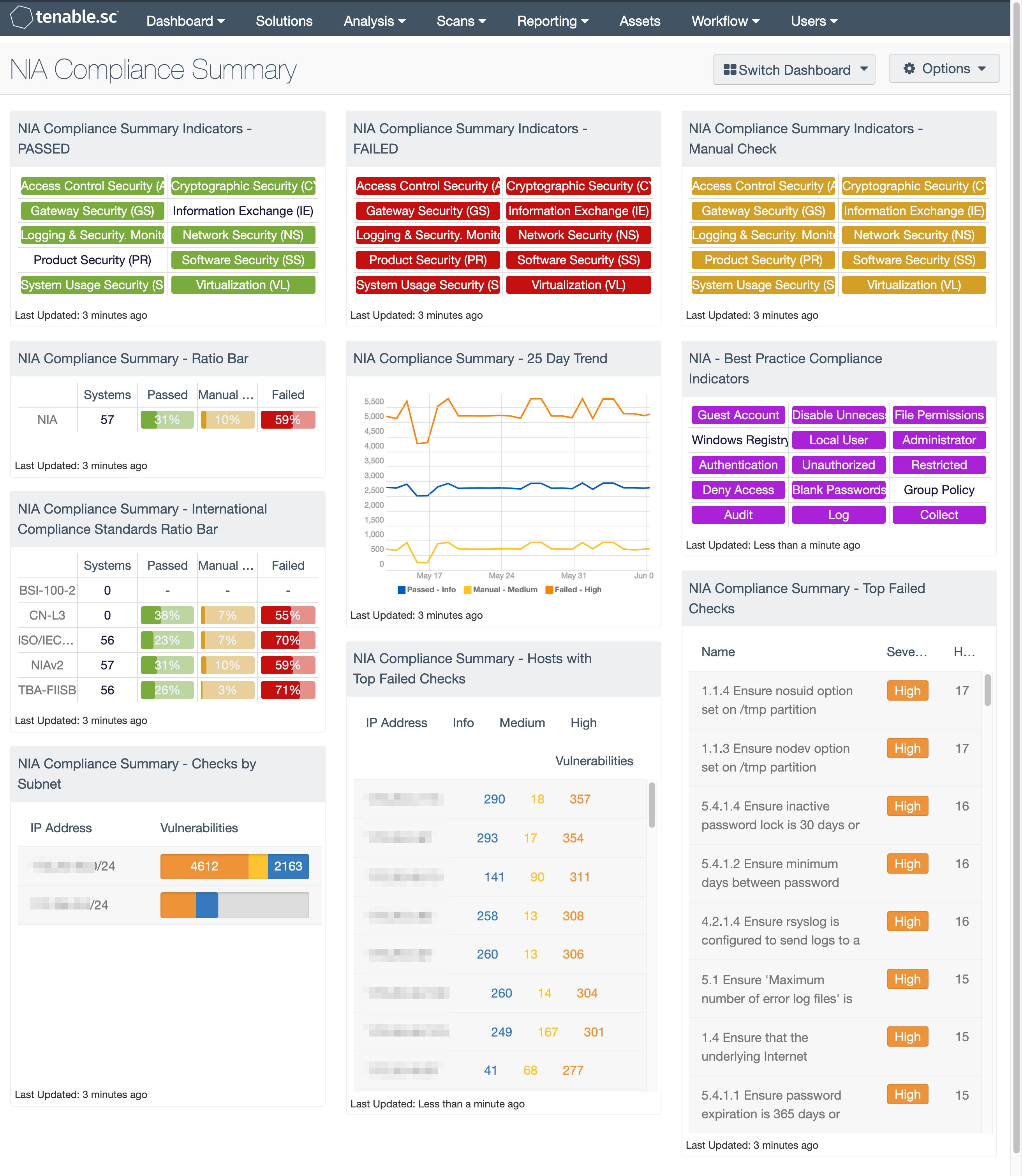
Tenable.sc provides agencies the ability to show compliance status with the NIA v2.0 policy. The dashboard is grouped with 3 areas of focus; the first shows three NIA Compliance Summary Indicators which provide an at-a-glance status of the Passed, Failed, and Manual Check compliance audit results for various security domains of the NIA policy. These domains include Access Control Security [AM], Cryptographic Security [CY], Gateway Security [GS], Information Exchange [IE], Logging and Security Monitoring [SM], Product Security [PR], Network Security [NS], Software Security [SS], System Usage Security [SU], and Virtualization [VL].
The center grouping provides the compliance team with historic view of NIA compliance along with other international standards such as the ISO 27000. By comparing the compliance results with NIA and other standards the risk officer can show how the agency is keeping pace with other generally accepted best practices. The final grouping of components provides a detailed view on compliance based on host, subnet, and failed checks.
The dashboard requirements are:
- Tenable.sc 5.14.1
- Nessus 8.10.1
- Compliance data
- Audit files containing NIAv2
Tenable.sc Continuous View (CV) is the market-defining On-Prem Cyber Exposure Platform. Tenable.sc CV provide the ability to Discover hardware assets, for a more details analysis. Not only detecting risks based on Common Vulnerabilities and Exposures (CVE), but also using more advanced methods such a Vulnerability Priority Rating (VPR). Tenable.sc provides customers with a full and completed Cyber Exposure platform for completing an effective Information Security Management System program. Tenable.sc supports configuration audits for more technologies than any other vendor, including operating systems, network devices, hypervisors, databases, web servers, and critical infrastructure.
The dashboard and its components are availabe in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Executive.
This dashboard contains the following components:
NIA Compliance Summary Indicators - PASSED: This component presents the results of controls with specific audit checks in the Tenable provided audit files, showing the domains with a “Passed” status. Passed checks are displayed in green and have the “Informational” severity designation. Clicking on a highlighted indicator will bring up the vulnerability analysis screen to display details on the compliance checks and allow further investigation. In the vulnerability analysis screen, setting the tool to IP Summary will display the systems on which the compliance checks are present. Setting the tool to Vulnerability Detail List will display all the details on each compliance check, including further applicable information, such as the expected and actual policy values and the specific sections of the various standards to which the compliance check relates.
NIA Compliance Summary Indicators - FAILED: This component presents the results of controls with specific audit checks in the Tenable provided audit files, showing the domains with a “Failed” status. Failed checks are displayed in red and have the “High” severity designation. Audit checks that are out of compliance need to be reviewed in case the configured check does not align with the policies in place. For example, if the password length policy says 8 – 15 characters is compliant, a configured policy of 25 characters will be marked noncompliant even though the policy is certainly very secure. Security professionals can download and edit the audit files to match specific policies. Clicking on a highlighted indicator will bring up the vulnerability analysis screen that display details on the compliance checks and allow further investigation. In the vulnerability analysis screen, setting the tool to IP Summary will display the systems on which the compliance checks are present. Setting the tool to Vulnerability Detail List will display all the details on each compliance check, including further applicable information, such as the expected and actual policy values and the specific sections of the various standards to which the compliance check relates.
NIA Compliance Summary Indicators - Manual Check: This component presents the results of controls with specific audit checks in the Tenable provided audit files, showing the domains with a “Manual” status. Manual checks are displayed in orange and have a “Medium” severity designation. Audit checks that require manual verification need to be reviewed to determine why the check was not marked passed or failed. Clicking on a highlighted indicator will bring up the vulnerability analysis screen which displays details on the compliance checks and allow further investigation. In the vulnerability analysis screen, setting the tool to IP Summary will display the systems on which the compliance checks are present. Setting the tool to Vulnerability Detail List will display all the details on each compliance check, including further applicable information, such as the expected and actual policy values and the specific sections of the various standards to which the compliance check relates.
NIA Compliance Summary - Ratio Bar: This matrix displays a summary of NIA compliance checks. The component provides host count columns and ratio bars for each severity level. The three columns with ratio bars provide a ratio of total audit checks to a specified status of the check. Checks that have passed are green, failed are red and checks that require manual verification are orange.
NIA Compliance Summary - International Compliance Standards Ratio Bar: This matrix displays a summary of several cross-referenced standards that are based on well-known international controls, providing hosts count and ratio bars for each severity level. The three columns with ratio bars show the ratio of total audit checks to a specified status of the check. Checks that have passed are green, failed checks are red, and checks that require manual verification are orange.
NIA Compliance Summary - 25 Day Trend: This component provides a 25-day trend analysis for all NIA compliance checks. The data points are calculated using the 'Days Since Observation' set to 'within the last day'. Thus, each data point only calculates the new compliance checks observed daily. The resulting graph more accurately depicts the change in compliance over the period of 25 days.
NIA - Best Practice Compliance Indicators: This component uses results from the NIA compliance audit to trigger on specific plugin keywords for best practice configuration guidelines. When the keyword or phrase has been detected within the plugin name, the indicator will turn purple. The analyst can click on the indicator and drill down to obtain additional information on hosts affected. This matrix will allow the analyst to readily identify specific compliance best practice keywords, and can be modified to suit organizational needs.
NIA Audit Results – Audit Check Subnet Summary: This table provides a summary of NIA audit results for the top 30 affected subnets. The columns are sorted using the failed compliance check (vulnerability) count column. The audit checks return 1 of 3 values: Info severity represents passed checks, High severity represents failed audit checks, and Medium severity represents checks that must be manually verified.
NIA Compliance Summary - Hosts with Top Failed Checks: This component provides a list of the top 100 systems on the network with NIA compliance audits. This table uses the IP Summary tool and displays systems with Passed, Failed, and Manual Check audit results sorted by Failed audit checks.
NIA Compliance Summary - Top Failed Checks: This table provides a list of the top 100 failed NIA compliance audit checks and a count of the systems having the failed audit check.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success