by Cody Dumont
As a part of many security compliance programs, internal security assessments are required and include vulnerability scanning on the network. Many compliance standards also require an organization to provide evidence of scanning activities. These dashboards provide a summary of scan activities and the attributes used during the scan. The Nessus vulnerability scanner is a fast and diverse tool that helps organizations of all sizes to audit their assets for security vulnerabilities. Nessus features high-speed discovery, configuration auditing, asset profiling, sensitive data discovery, and vulnerability analysis of your security posture. Nessus scanners can be distributed throughout an entire enterprise, inside DMZs, and across physically separate networks. Nessus stays current through automatic updates that pull the latest vulnerability checks directly from Tenable.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Discovery & Detection.
The dashboard requirements are:
- Tenable.sc 4.8.1
- Nessus 8.4.0
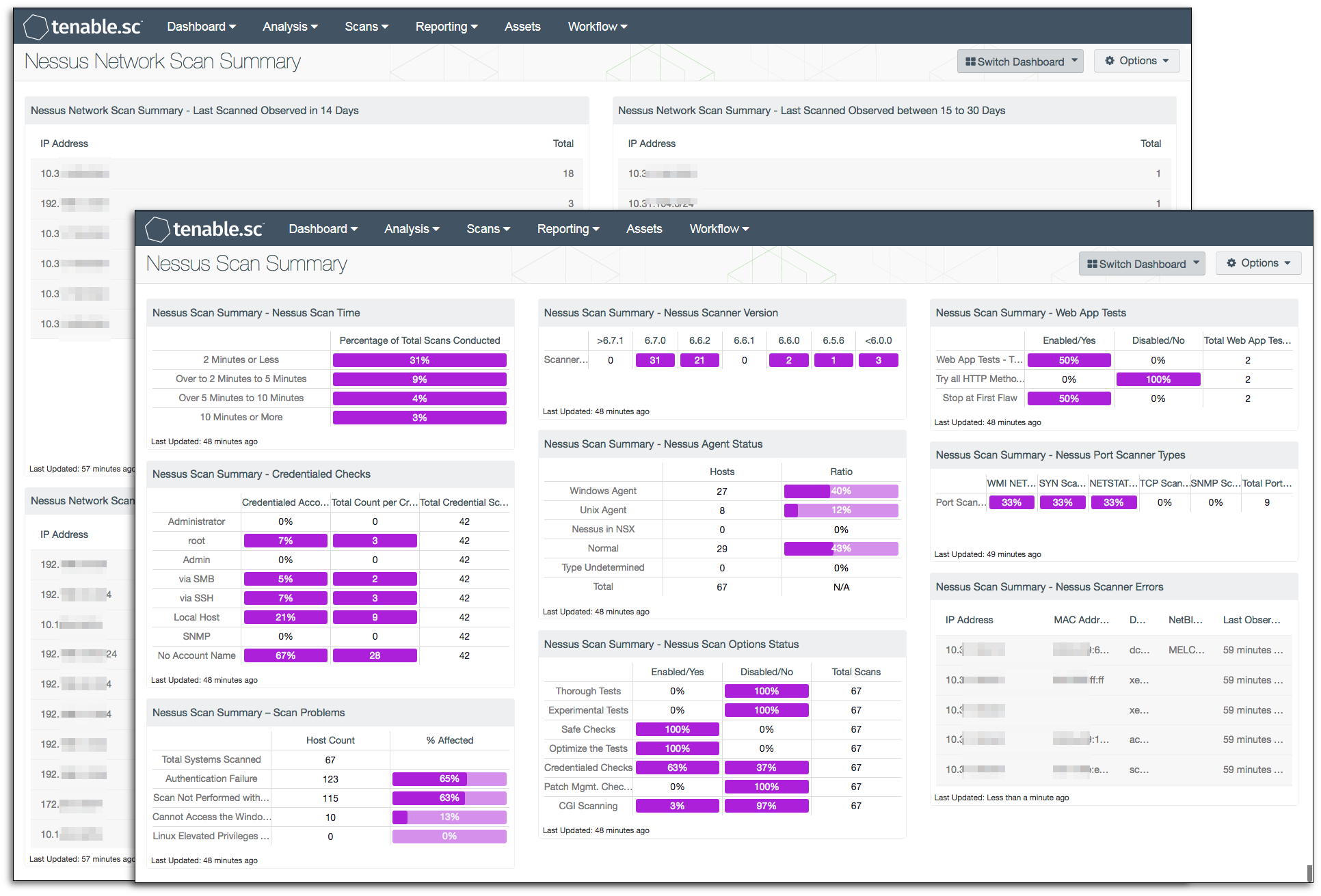
The plugin ID # 19506 (Nessus Scan Information) provides information about a scan including the version of the scan, the amount of time it takes to complete the scan, if a credentialed scan took place, and more. Knowing about the various Nessus scanner options or features can be a great benefit in producing more accurate and faster vulnerability scans. Good security practices require performing vulnerability scans, and require an organization to provide evidence of the scanning activities. The Nessus Scan Summary dashboard displays Nessus Scan Time, Web Apps Test, Nessus Scanner Version, Nessus Port Scanner Types, Nessus Scan Options Status, and Credential Checks, while the Nessus Network Scan Summary dashboard will provide a summary of Nessus scans per 24-bit subnet mask Class C network.
The Nessus Scan Summary dashboard has seven components that display different options, versions, and results of the Nessus scans of the network. Three matrices display scan options, scan durations, and credentials used during the scan. Two matrices display port scanners used and if web applications tests were enabled. Two components display the different versions of Nessus scanners and errors discovered during a Nessus scan.
The Nessus Network Scan Summary dashboard has four tables, each displaying summary of subnets scanned during a period of time. The tables identify the subnets scanned over different time periods. There is a table showing scans occurring over the past 14 days, between 15 to 30 days, between 31 to 90 days, and over 90 days.
Tenable.sc Continuous View (CV) provides a centralized solution that allows for the most comprehensive and integrated view of network health. Nessus is an integral part of Tenable.sc CV, which provides a central location for configurations, deployments, dashboards, and reports of Nessus scans.
Listed below are the included components:
- Nessus Scanned Summary - Nessus Scan Time: This matrix displays a summary of the time taken to complete vulnerability scans. Scan summaries are displayed for scans completed in less than 2 minutes, over 2 minutes to 5 minutes, over 5 minutes to 10 minutes, and over 10 minutes. The results are shown in the percentage of the total scans conducted. For example, in the screenshot, 14% of the completed scans took less than 2 minutes.
- Nessus Scan Summary - Nessus Scanner Errors: This component displays any host that encountered a Nessus scan error while scanning the host. This table is configured for vulnerability text containing “error” and using plugin ID 19506. This table will display the IP Address, MAC Address, DNS, NetBIOS, and Last Observed Field columns for each host with a Nessus scan error.
- Nessus Scan Summary - Web App Tests: This component provides information on the web application test settings enabled and the number of systems where web app tests were performed. Nessus can scan web applications for SQL injection, cross-site scripting, directory traversal and many more web application vulnerabilities. As Nessus performs web application checks, the server will fail a check if any of the following are discovered: SQL injection, cross-site scripting, directory traversal vulnerabilities, HTTP response splitting/header injections, common application error messages, testing for common backup script files, include file source code disclosure, insecure HTTP methods, WebDAV, default web server installation, and testing for diagnostics page.
- Nessus Scan Summary - Scan Problems: This matrix provides a high level understanding of how many systems on the network are not being scanned, or are not being fully scanned. By using several plugins, the matrix identifies systems that are failing authentication, systems that were scanned without sufficient credentials, and if system resources (such as the registry of Windows computers) are accessible. The first column provides the host count of systems that have problems related to successful scanning, and the second column provides a percentage of systems scanned compared to their respective problems. When the percentage of scan problems are higher than 10%, then vulnerability data collected does not reflect a true state of risk to the organization. The security operations team will need to review the systems that are failing to be scanned properly, and correct any issues found.
- Nessus Scan Summary - Nessus Agent Status: This component provides a host count and ratio analysis of the scan types performed by Nessus. The matrix uses plugin 19506 and the “Scan Type” line to identify if the scans were completed using agents or by scanning the systems using traditional active scanning. There are five distinct possible results; they are: Windows Client, Unix Client, NSX, Normal, and Undetermined.
- Nessus Scan Summary - Nessus Scanner Version: This matrix displays the number of hosts that have been scanned by different Nessus scanner versions. The purpose is to understand what versions of Nessus scanners are being used on the network. Tenable recommends installing the same Nessus scanner version throughout the network. Having older versions of Nessus might lead to false or misleading results, whereas having the latest Nessus version with updated plugins and matching configurations will provide the same results throughout the network.
- Nessus Scan Summary - Nessus Port Scanner Types: This matrix displays the percentage of port scans used during vulnerability scan. Understanding if a port is open or closed is a critical step in the discovery process associated with successfully attacking systems. Nessus port scanner system includes five types of network-based port scanners. This matrix displays the percentage of scans to port scanner used during the vulnerability scan. Knowing what options are available in Nessus port scanners can be of great benefit in tuning your Nessus port scans. Understanding the situations in which to use each of the Nessus port scanners will result in more accurate and faster vulnerability scans. Below are brief descriptions of the different types of Nessus port scanners.
- Nessus Scan Summary - Nessus Scan Options Status: This component displays an overview of the Nessus Scan Options that are enabled or disabled while conducting vulnerability assessments. Knowing what options are enabled or disabled will help a Nessus user optimize their scans. Nessus users have a wide range of powerful options whose functionalities are critical to successful vulnerability scans.
- Nessus Scanned Summary - Credentialed Checks: This component displays a matrix providing a count of credentials used while scanning the network. The rows show which credentials are being used by percentage, and a total count for each credential.
- Nessus Network Scan Summary - Last Scanned Observed in 14 Days: This table displays a Class C summary table of the number of hosts that have been scanned per 24-bit subnet mask on the network for the last 14 days. This component uses the plugin ID #19506(Nessus Scan Information) with a last observed within 14 days. Most Nessus scan should be performed within 14 days depending on the purpose of the scan and the size of the network environment. Individual company requirements would dictate how often Nessus scans are performed.
- Nessus Network Scan Summary - Last Scanned Observed between 15 to 30 Days: This component displays a Class C summary table of the number of hosts that have been scanned per 24-bit subnet mask on the network between 15 to 30 days. This component uses the plugin ID #19506 (Nessus Scan Information) with a last observed between 15 to 30 days. IIn general, Nessus scans that are done between 15 to 30 days would be the more complicated and have a more impact on the network. Depending on the scan and the network environment these scan are doing a more explicated scan or thorough scans.
- Nessus Network Scan Summary - Last Scanned Observed between 31 to 90 Days: This component displays a Class C summary table of the number of hosts that have been scanned in each of the 24-bit subnet mask on the network for the last 31 to 90 days. This component uses the plugin ID #19506 (Nessus Scan Information) with a last observed between 31 to 90 days. The Nessus scans could be utilized as a one-time scan for a unique concern or question. Another reason a host could be on this table could that host no longer is part of the network.
- Nessus Network Scan Summary - Last Scanned Observed Over 90 Days:This component displays a Class C summary table of the number of hosts that have been scanned per 24-bit subnet mask on the network for over the last 90 days. This component uses the plugin ID #19506 (Nessus Scan Information) with the last observed over 90 days. In general, all scans should be performed within 90 days. If you are seeing information within this table, then there should be an investigation as to why.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success