Risk mitigation is a constantly moving target as new exploits are developed and new vulnerabilities are discovered. Vulnerability remediation efforts can be precisely tailored to address the current threats imposed by specific exploit frameworks. As new exploit frameworks and vulnerabilities are exposed, remediation efforts have to be adjusted accordingly. By integrating with Nessus, SecurityCenter is able to present extensive data about exploitable vulnerabilities detected in the network.
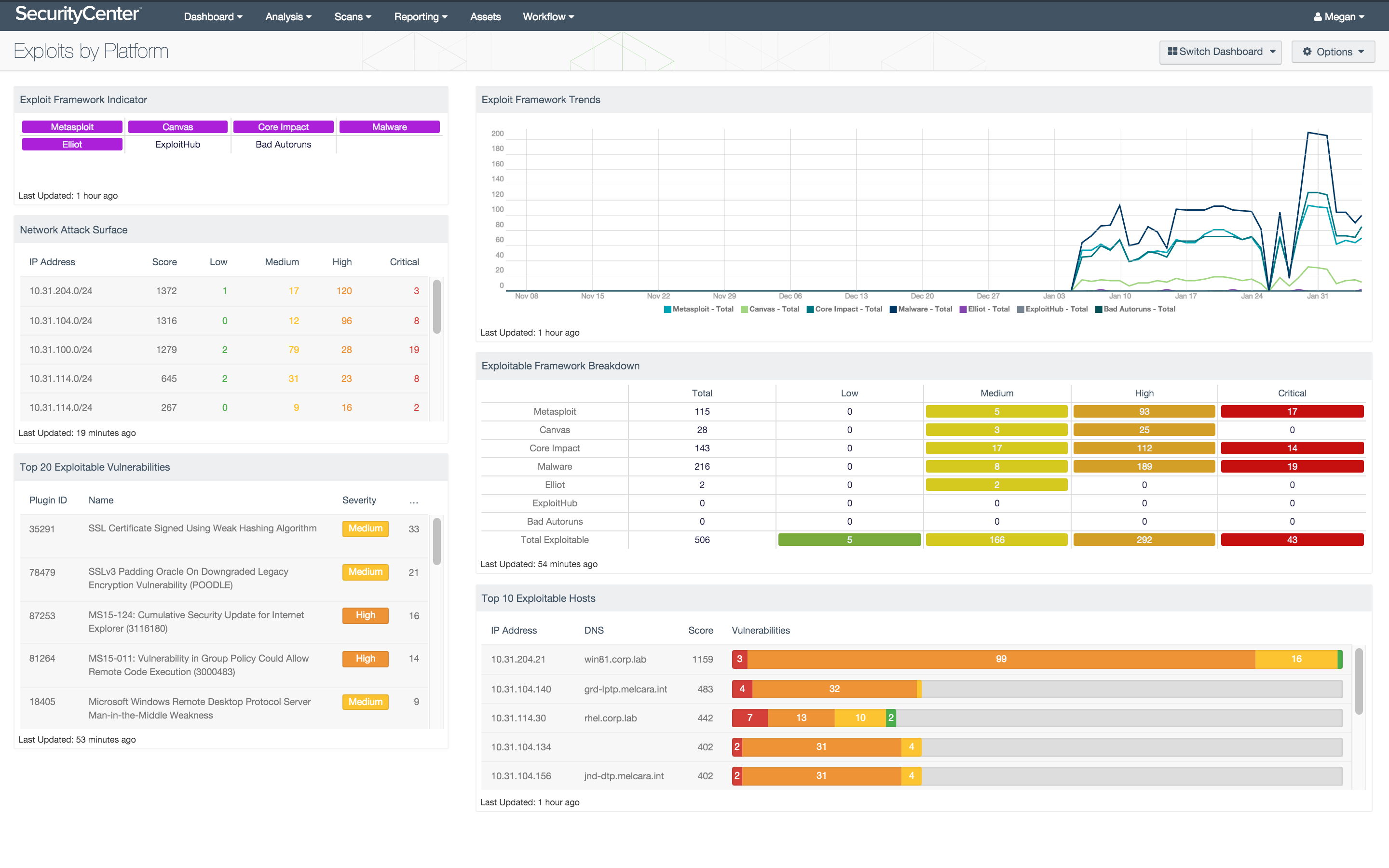
The Exploits by Platform dashboard assists security teams with the process of vulnerability remediation by providing an enhanced view of the security of a network based on specific exploit frameworks. The dashboard presents information about current vulnerabilities on the network through several views. Vulnerability data is filtered with Nessus plugins to provide details on exploit frameworks, severities, and associated plugins.
The components in this dashboard provide several perspectives on the vulnerability status of the organization. Specific filters for Nessus plugins, exploit frameworks, and severities help security teams determine where mitigation efforts should be focused in order to effectively defend against specific exploits. The effectiveness of mitigation efforts over time is conveyed through trend data so that processes can be tailored to address persisting vulnerabilities. The extensive information about the current vulnerabilities found on the network can serve as a starting point for remediation efforts. The components in this dashboard provide a current view of the vulnerability status of the network that can be used to effectively enhance mitigation efforts.
This dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. This dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments. The dashboard requirements are:
- SecurityCenter 4.8.2
- Nessus 6.5.4
SecurityCenter Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. By integrating with Nessus, SecurityCenter CV’s continuous network monitoring is able to detect systems and vulnerabilities across the enterprise.
The dashboard includes the following components:
- Exploit Framework Indicator: The Exploit Framework Indicator matrix shows whether vulnerabilities related to specific exploit frameworks are present in the network.
- Network Attack Surface: The Network Attack Surface table lists the most exploitable subnets by score.
- Top 20 Exploitable Vulnerabilities: The Top 20 Exploitable Vulnerabilities table lists the top exploitable vulnerabilities by total count.
- Exploit Framework Trends: The Exploit Framework Trends line chart presents a 25-day trend of vulnerabilities by exploit framework.
- Exploit Framework Breakdown: The Exploit Framework Breakdown matrix displays the counts of vulnerabilities by exploit framework and severity.
- Top 10 Exploitable Hosts: The Top 10 Exploitable Hosts table lists the ten most exploitable hosts based on exploitable vulnerability score.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success