Monitoring Adobe software for vulnerabilities is essential to securing a network against exploitation. Adobe software is essential to many computing tasks, and as a result is a common target for attackers. By leveraging vulnerability data gathered by Tenable Nessus, Tenable SecurityCenter is able to provide detailed insight into vulnerabilities related to Adobe software deployed in an environment.
The Adobe Summary dashboard provides insight into vulnerabilities associated with Adobe software that may expose an organization to increased risk of exploitation. Vulnerabilities related to various types of Adobe software are specifically tracked. Adobe software is a requirement for many organizations, and as a result can be targeted for exploitation. By monitoring the network specifically for vulnerabilities in Adobe software, security teams can more effectively secure the network against exploitation and intrusion.
The components in this dashboard leverage data gathered by active vulnerability scanning with Nessus and can also use passive vulnerability detection with Tenable Passive Vulnerability Scanner (PVS). The data collected is filtered to provide insight into the vulnerabilities related to Adobe software in the environment. Vulnerabilities are tracked by time, severity, and exploitability in order to provide a more complete view of the security status of the network. Security teams can use all of the components in this dashboard to assist in identifying, monitoring, and remediating vulnerabilities in Adobe software that may expose their organization to risk.
This dashboard is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments. The dashboard requirements are:
- SecurityCenter 5.3.1
- Nessus 6.8.1
Tenable SecurityCenter provides extensive network monitoring by leveraging a unique combination of detection, reporting, and pattern recognition utilizing industry recognized algorithms and models. SecurityCenter is continuously updated to detect advanced threats and vulnerabilities. Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context and enabling decisive action that transforms the security program from reactive to proactive. Continuous vulnerability analysis enables security teams to more effectively tailor remediation efforts. Monitoring the network to ensure that all systems are secured against vulnerabilities is essential to ongoing security efforts. Tenable’s extensive network monitoring capabilities can verify that systems are successfully scanned regularly and secured against vulnerabilities, enabling ongoing improvements to an organization’s security posture.
The following components are included in this dashboard:
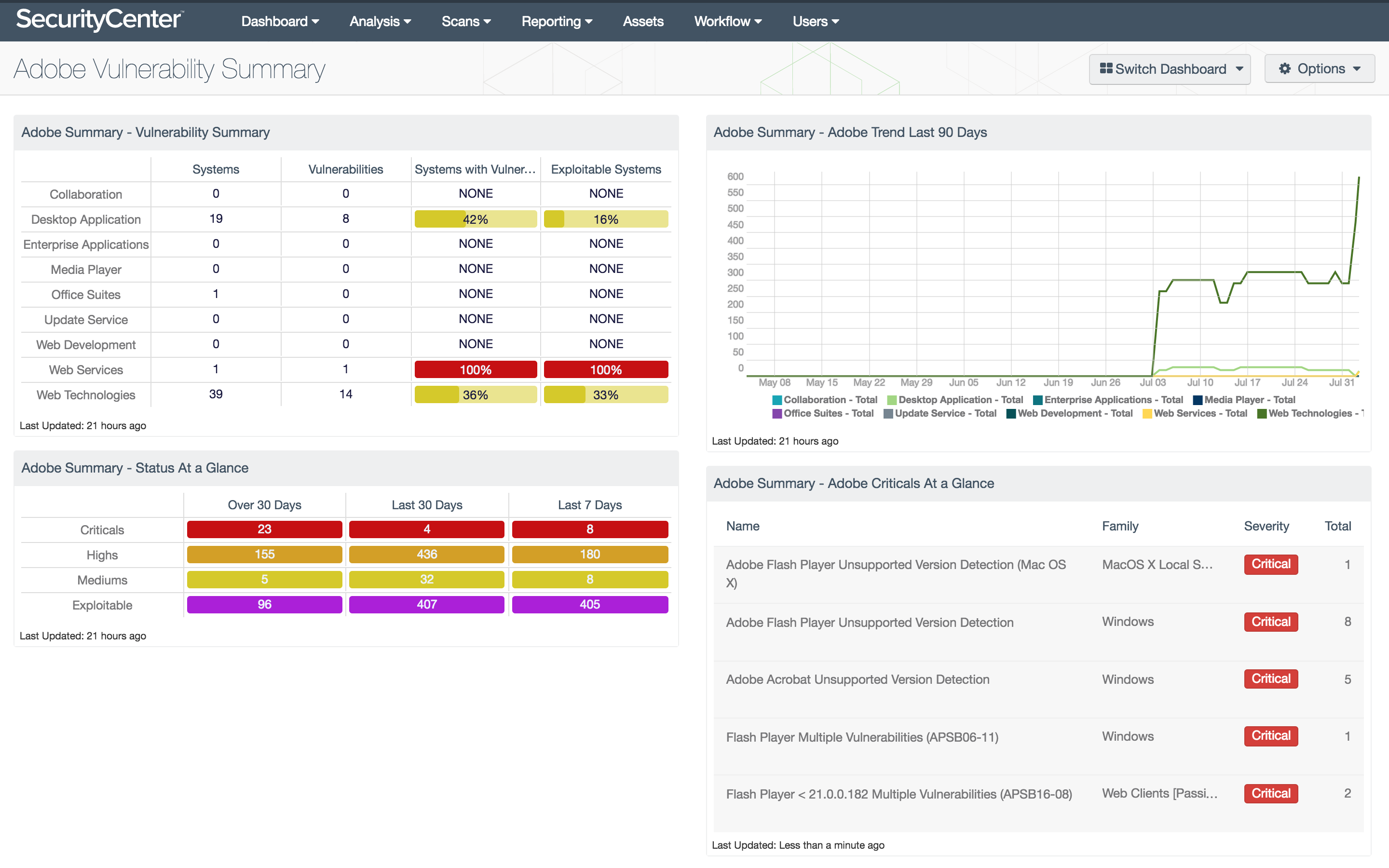
- Vulnerability Status at a Glance: This matrix displays the counts of vulnerabilities related to Adobe software by severity and discovery date. Counts are provided for medium, high, and critical severity vulnerabilities, as well as exploitable vulnerabilities. Security teams can use this matrix to monitor the detection of vulnerabilities related to Adobe software in their environment.
- Adobe Vulnerability Trend (Last 90 Days): This trend line chart depicts the detection of vulnerabilities related to specific categories of Adobe software over the last 90 days. Each line is filtered for medium, high, and critical severity vulnerabilities related to a specific category of Adobe software. Security teams can use this line chart to track the presence of various types of vulnerabilities in Adobe software over time.
- Adobe Critical Vulnerabilities at a Glance: This table lists the critical vulnerabilities related to Adobe software detected in the environment. Relevant vulnerabilities with a critical severity level are shown to focus on the vulnerabilities that present the highest level of risk to the organization. For each vulnerability, the plugin name, severity, and family are listed. Security teams can use this component to identify and remediate the highest risk vulnerabilities in Adobe software.
- Adobe Vulnerability Summary: This matrix displays information about the systems and vulnerabilities detected on the network, listed by Adobe software category. The counts of vulnerabilities and impacted systems are provided, along with percentages of systems with vulnerabilities and exploitable systems. Security teams can use this component to identify high-risk Adobe software and the potentially impacted systems.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success