CVE-2023-4966 (CitrixBleed): Invalidate Active or Persistent Sessions To Prevent Further Compromise

Patching CitrixBleed isn’t enough; organizations need to invalidate active or persistent session tokens as the these tokens can be used to bypass authentication even with multifactor authentication enabled
Background
On October 10, Citrix published its advisory (CTX579459) for CVE-2023-4966, a critical vulnerability in its NetScaler Application Delivery Controller (ADC) and Gateway devices that is referred to as CitrixBleed. Tenable Research has published two blogs on CitrixBleed, our initial analysis of the vulnerability as well as a Frequently Asked Questions (FAQ) blog providing added context surrounding the in-the-wild exploitation by threat actors including multiple ransomware groups. Despite the availability of patches, organizations should be wary that simply applying the available patches is not enough and additional steps are required to mitigate the threat posed by this vulnerability.
Analysis
CVE-2023-4966 is an information disclosure vulnerability in NetScaler ADC and NetScaler Gateway. Exploitation of this flaw would enable an attacker to obtain valid session tokens from the vulnerable device’s memory. These session tokens allow an attacker to bypass authentication on a device even if multifactor authentication is enabled.
As long as these stolen session tokens remain valid, an attacker can bypass authentication on a Citrix ADC or Gateway device. Therefore, even if your organization has patched CitrixBleed across these assets in your environment, you may still be vulnerable to further compromise.
Researchers including Kevin Beaumont, who has been instrumental in sounding the alarm around CitrixBleed, have observed the theft of session tokens from vulnerable systems that have been leveraged post patch. Beaumont also says that an attacker that exploited CitrixBleed reportedly “harvested session tokens from almost every box on the internet.” It is unclear if this attacker is an initial access broker that may have already begun to sell the data to third parties including ransomware groups.
The importance of invalidating these session tokens post patch is crucial for organizations that utilize Citrix NetScaler ADC ad Gateway in their networks.
Additionally, it would be advisable for each organization to do their due diligence and determine potential impact of CitrixBleed by looking for indicators of compromise (IOCs). For instance, a joint cybersecurity advisory (AA23-325A) from several government agencies including the Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of Investigation (FBI), Multi-State Information Sharing & Analysis Center (MS-ISAC), and Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC) provides IOC’s as well as additional information on the tactics, techniques, and procedures used by the LockBit 3.0 ransomware group in their exploitation of CitrixBleed. A malware analysis report from the Department of Homeland Security provides insight on malicious files found during investigations of systems breached using CitrixBleed. Both of these resources provide valuable information for investigations to identify compromised systems that have been impacted by CitrixBleed.
Solution
Once the appropriate patches have been applied to vulnerable NetScaler ADC and Gateway assets, it is vital that organizations invalidate or kill any existing sessions from these devices.
As noted in its blog, Citrix says that the following commands must be run to “remove any active or persistent sessions” from these devices:
Commands to Remove Active or Persistent Sessions:
kill aaa session -allkill icaconnection -allkill rdp connection -allkill pcoipConnection -allclear lb persistentSessions
It is important the formatting remains intact when copy and pasting these commands.
Identifying affected systems
Customers can utilize the plugins available for CVE-2023-4966 to identify vulnerable devices.
| Plugin ID | Title | Type |
|---|---|---|
| 183026 | NetScaler ADC and NetScaler Gateway Multiple Vulnerabilities (CTX579459) | Version Check |
| 186176 | Citrix ADC and Citrix NetScaler Gateway Information Disclosure (CTX579459) (Direct Check) | Direct Check |
| 114100 | Citrix Gateway / ADC Sensitive Information Exposure | Tenable Web App Scanning (formerly Tenable.io Web Application Scanning)Remote Check |
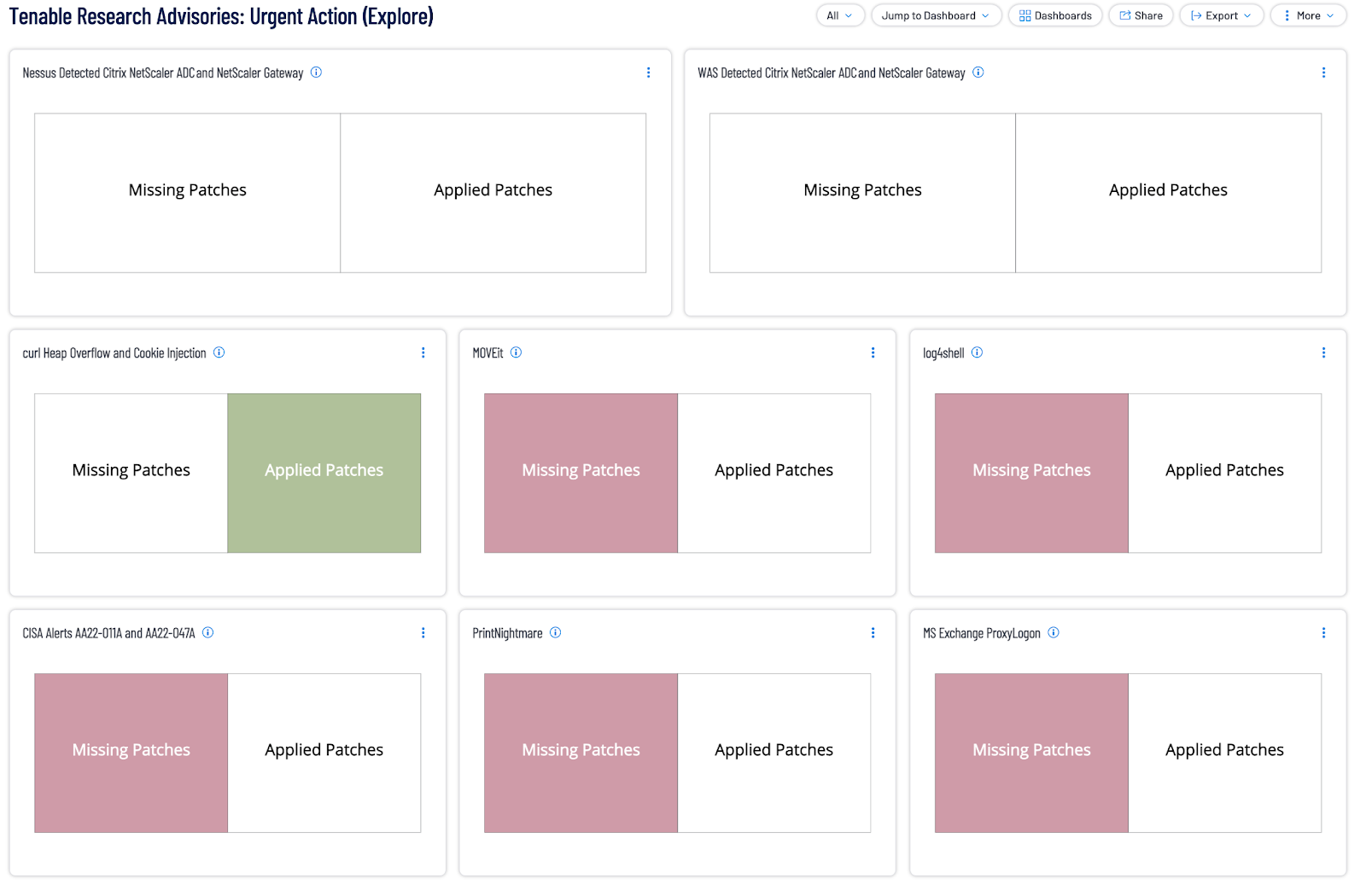
Additionally, customers can utilize our Tenable Research Advisories dashboards in Tenable Vulnerability Management and Tenable Security Center as well as a widget for Tenable Vulnerability Management to identify assets in your environment that are missing patches for Netscaler ADC and Gateway.
Get more information
- Tenable Blog Post for CVE-2023-4966 ("Citrix Bleed")
- Tenable FAQ Blog Post for CitrixBleed
- CTX579459: Citrix Security Bulletin for CVE-2023-4966, CVE-2023-4967
- NetScaler investigation recommendations for CVE-2023-4966
- Kevin Beaumont Blog: Mass Exploitation of CitrixBleed including Ransomware Group
- Cybersecurity Advisory: LockBit 3.0 Ransomware Affiliates Exploit CVE 2023-4966 Citrix Bleed Vulnerability
- DHS MAR-10478915-1.v1 Citrix Bleed
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
Learn more
- Exposure Management
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success