by Cesar Navas
October 27, 2015
Identifying vulnerable hosts in a network is only the first step in securing an organization. Unaddressed vulnerabilities on hosts can provide attackers with easier access to an otherwise secure network. Determining and implementing remediation measures is key to properly securing any network. By leveraging the capabilities of Tenable.sc, Nessus, and the Nessus Network Monitory (NNM), security teams can more easily identify hosts with vulnerabilities requiring remediation in order to more effectively secure their network.
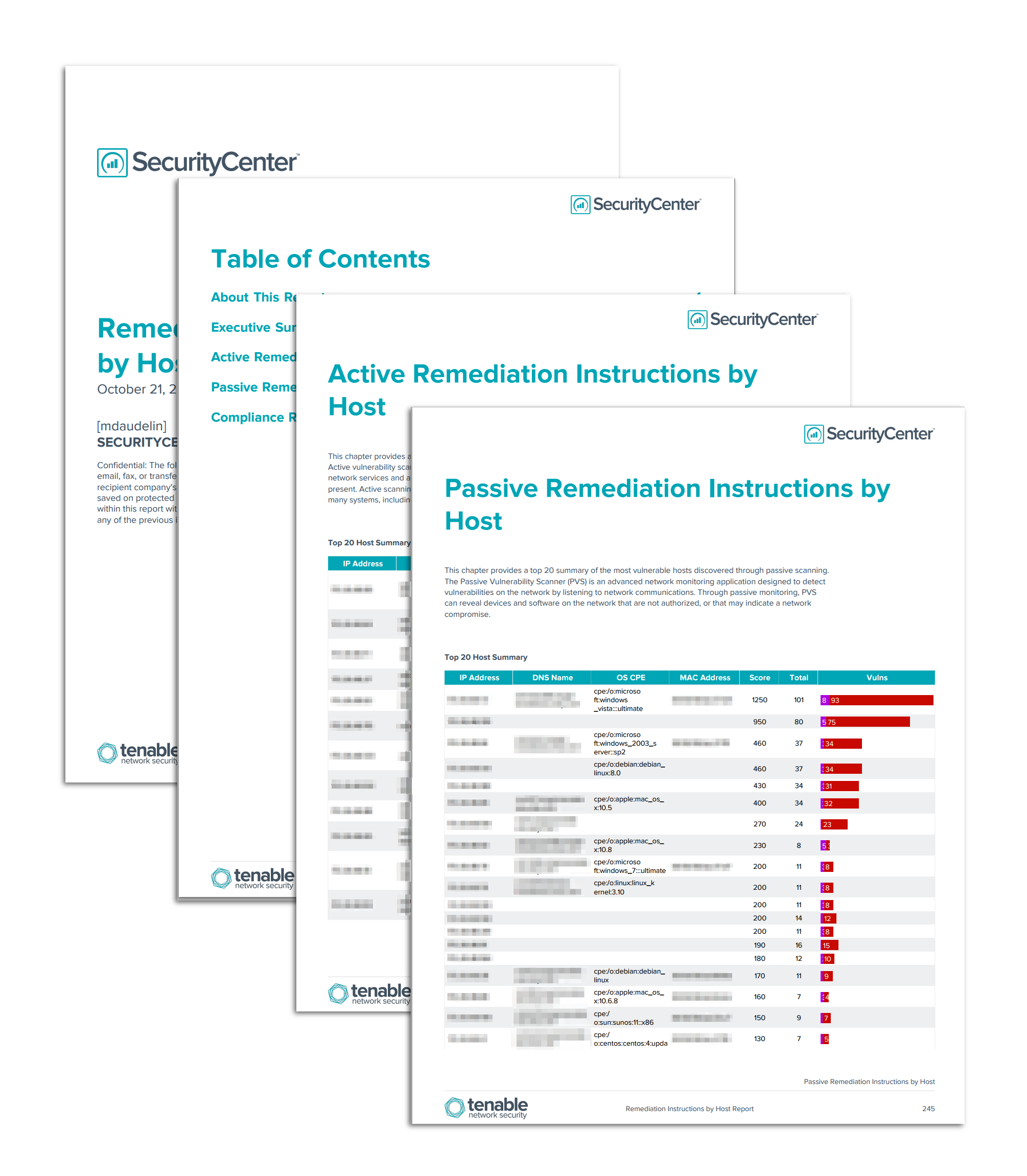
The Remediation Instructions by Host report provides detailed information on the most vulnerable hosts identified on the network. The report is organized by plugin type (Active, Passive, and Compliance) and broken down by host. For each of the top 20 most vulnerable hosts, detailed steps to mitigate the risk of the vulnerabilities, including CVE, BID, and vendor knowledgebase articles, are provided. Additionally, this report provides information about the top services and ports on each vulnerable host.
The chapters in this report provide distinct views of the vulnerable hosts detected on the network. Each chapter focuses on a specific plugin type: active, passive, or compliance. For each type, the 20 most vulnerable hosts and suggested steps to remediate vulnerabilities on them are detailed. Security teams can use these chapters to understand the vulnerable hosts that could impact their network and implement the steps necessary for remediation.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The report requirements are:
- Tenable.sc 4.8.2
- Nessus 8.5.1
- NNM 5.9.1
Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. The Nessus Network Monitor (NNM) performs deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. By integrating with Nessus and NNM, Tenable.sc CV’s continuous network monitoring is able to detect threats and vulnerabilities across the enterprise.
This report contains the following chapters:
- Executive Summary: This chapter provides an overview of the vulnerability statuses of hosts covered in this report.
- Active Vulnerability Remediation Plan: This chapter provides a top 20 summary of vulnerabilities discovered through active scanning by severity level.
- Passive Vulnerability Remediation Plan: This chapter provides a top 20 summary of vulnerabilities discovered through passive scanning by severity level.
- Compliance Check Remediation Plan: This chapter provides a top 20 summary of compliance check failures and checks that require manual verification, which are reported through performing scans with audit files in Tenable.sc.