by Josef Weiss
July 29, 2014
The ability to share a remote desktop, graphically and independent of platform, can be beneficial and increase productivity. Virtual Network Computing (VNC) a platform independent application, utilizes the Remote Frame Buffer (RFB) protocol to accomplish this task. The original VNC source code was released to the general public as open source under the GNU General Public License. There are many VNC variants available, with different features and functionality.
A common use for VNC is for an analyst or administrator to access remote devices for troubleshooting or maintenance. RFB does not use encryption natively, and therefore VNC is not an inherently secure technology. RFB does not send passwords as plain text, but cracking could be accomplished by sniffing both the encryption key and encoded password on the wire. Some versions of VNC are known to truncate passwords that are longer than 8 characters, making cracking easier to accomplish.
Many existing remote desktop programs are based on VNC technology and are supported by a variety of operating systems. In additions to VNC’s lack of encryption, attackers often use VNC as a post-exploitation method for maintaining access to the victims’ computers.
Tenable SecurityCenter Continuous View (CV) with Nessus and Nessus Network Monitor (NNM) provide detailed information about VNC vulnerabilities, exploits, events, and related traffic flows. The VNC Detection dashboard contains components that report on VNC vulnerabilities, exploits, and traffic flow. By understanding the vulnerabilities and their severities, analysts can better assess risk and prioritize mitigations. Furthermore, knowing which vulnerabilities are exploitable helps security professionals resolve threats before attacks occur. Understanding the normal network traffic flow and the direction of VNC communications allows for anomaly analysis and increases the likelihood breach detection.
This dashboard provides all these tools to help assist in identifying potential VNC vulnerabilities and associated risks. The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Discovery & Detection.
The dashboard requirements are:
- SecurityCenter 5.6.1
- Nessus 7.0.1
- NNM 5.4.0
Components
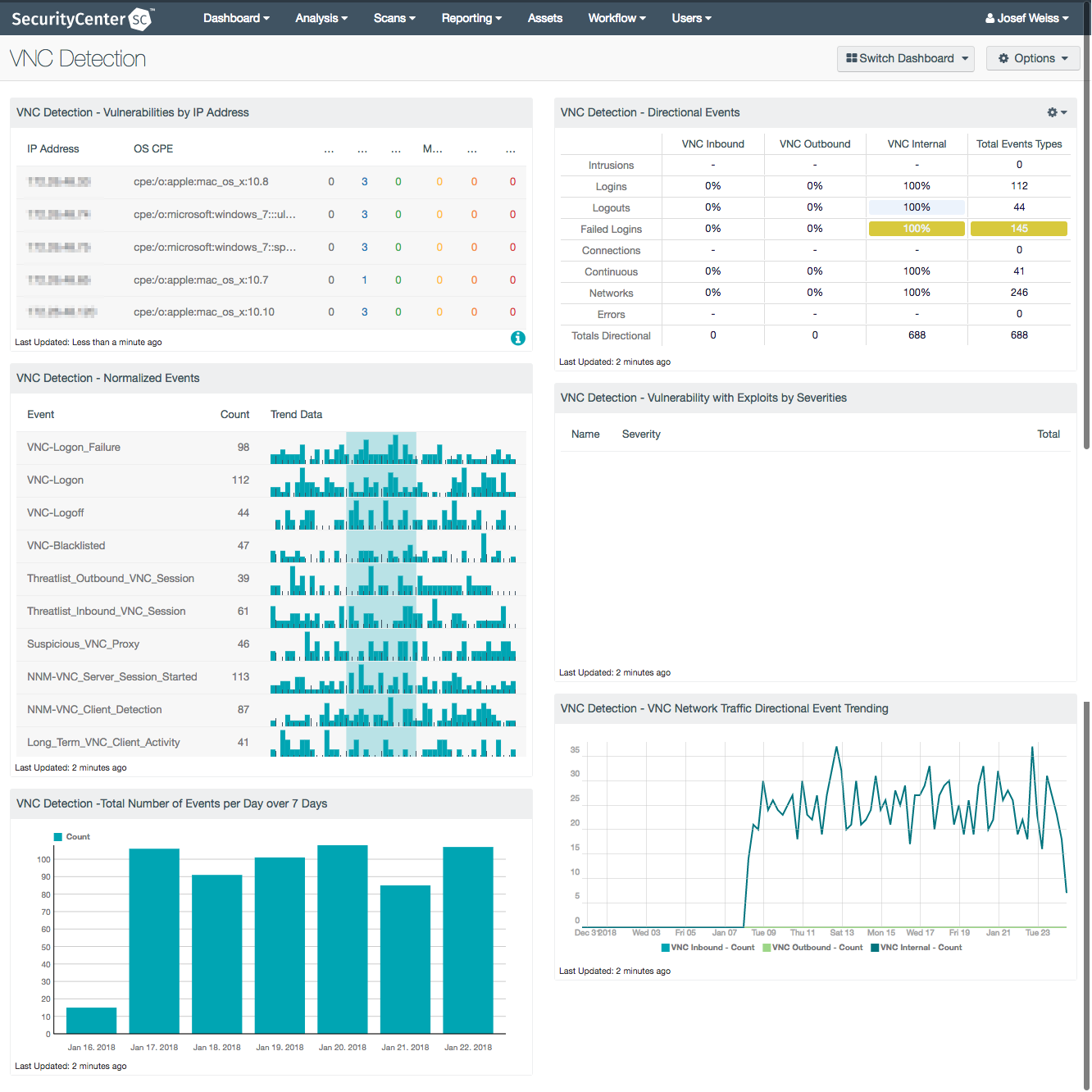
VNC Detection - Vulnerabilities by IP Address: By understanding the vulnerabilities and their severities, analysts can better assess risk and prioritize mitigations to discovered vulnerabilities. This component provides a table of the top 20 vulnerable VNC systems. The table is sorted by vulnerability weight score. The columns displayed are IP Address, OS, Score, and vulnerability severity (info, low, medium, high, and critical). The severity columns will have a total vulnerability count in each severity cell.
VNC Detection - Directional Events: Understanding the normal network traffic flow and the direction of VNC communications allows for anomaly analysis and increases the likelihood of breach detection. This component provides a table of VNC network traffic directional flow by 8 event types. The event types used are: Intrusion, Login, Logout, Failed Login, Connection, Continuous, Networks, and Errors. SecurityCenter CV defines network traffic flow as internal, inbound and outbound. The Total Event Types column displays a count of all of the respective events, while the remaining three columns show the percentage of events according to directional flow.
VNC Detection - Normalized Events: Analyzing both the normalized event and the trending of these events will help analysts understand VNC activity on the network and detect anomalies. This component displays normalized events from SecurityCenter CV over the past 7 days. The fields displayed are: normalized events names, total events, and a trend graph for events collected over the past 7 days.
VNC Detection - Vulnerability with Exploits by Severities: By detecting exploitable VNC vulnerabilities, analysts can identify and mitigate exploits before a compromise can occur. This component displays the top exploitable VNC vulnerabilities for both servers and clients. The table columns are: vulnerability name, family, severity, and total vulnerabilities, which are sorted by severity level.
VNC Detection -Total Number of Events per Day over 7 Days: This event-by-day component is useful for understanding the total amount of VNC events being seen each day over a period of 7 days . By viewing the total amount of VNC event each day, an IT team can quickly recognize when anomalies are happening in the network. This component displays the total number of VNC events per day over a 7 day period. Any substantial increase or decrease in VNC events indicates a change in the normal VNC activity.
VNC Detection - VNC Network Traffic Directional Event Trending: Monitoring for inbound and outbound VNC traffic will vary based on network configuration. Network administrators should review network traffic trends to determine if traffic is following normal usage patterns. This component displays a VNC network traffic directional event trending flow over 25 days. The traffic flow is represented using the directional filters of internal, inbound, and outbound.