by Stephanie Dunn
November 8, 2016
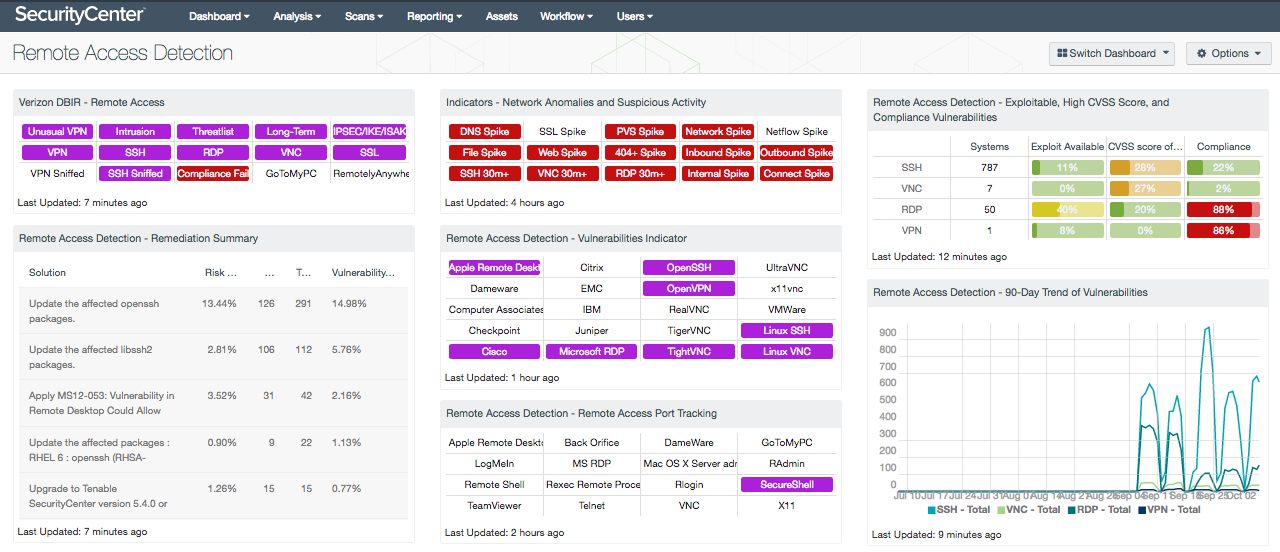
Many organizations today utilize remote access services and applications to remotely connect to internal systems within a network. Without continuous monitoring, these services can be exploited and leave critical data at risk. This dashboard presents the latest information on known remote access vulnerabilities from products such as Cisco AnyConnect, Citrix GoToAssist, Microsoft Remote Desktop, and RealVNC.
The content in this dashboard embraces all collection methods from Tenable SecurityCenter Continuous View (CV). By using Tenable Nessus and the Tenable Passive Vulnerability Scanner (PVS), the components are able to identify systems capable of remote access. Nessus looks for installed software, browser plugins, and other artifacts pointing to desktop control software to identify systems with remote access capabilities. PVS passively monitors network traffic to identify vulnerabilities and perform host, application, and operating system discovery using advanced packet analysis.
This dashboard uses the Common Platform Enumeration (CPE) filter to identify many of the software programs used in enterprise networks. According to NIST, the CPE is a structured naming scheme for information technology systems, software, and packages. Based upon the generic syntax for Uniform Resource Identifiers (URI), CPE includes a formal name format, a method for checking names against a system, and a description format for binding text and tests to a name. Tenable assigns CPEs to plugins where appropriate. This allows for analysts to search for common CPE prefixes such as “cpe:/a:cisco:vpn,” “cpe:/a:citrix:gotoassist,” and “cpe:/a:realvnc.” Associating CPE strings with vulnerabilities allows the analysts to separate operating system vulnerabilities from application vulnerabilities, and adds to the level of vulnerability detail provided to the organization.
The Tenable Log Correlation Engine (LCE) is used to log PVS events and track other remote access related events. LCE also provides the ability to monitor NetFlow information by either collecting NetFlow flows using the Tenable NetFlow Monitor or by using the Tenable Network Monitor Agent. The Network Monitor Agent works similar to a NetFlow collector, but stores the records in a LCE-friendly method. An additional benefit of the Network Monitor Agent is that any syslog messages captured will also be forwarded to LCE for analysis. The NetFlow and Network Monitor Agent can detect traffic patterns, which can then be identified as interesting. One of the components uses the destination port filter; this shows common ports used for several protocols related to remote access to identify possible remote access activity. This traffic may be false positives, but should be investigated to determine if malicious activity is occurring.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection and Vulnerability Assessments. The dashboard requirements are:
- SecurityCenter 5.3.1
- Nessus 6.8.1
- PVS 5.1.0
- LCE 4.8.0
- Tenable NetFlow Monitor
- Tenable Network Monitor
Tenable Network Security transforms security technology for the business needs of tomorrow through comprehensive solutions that provide continuous visibility and critical context, enabling decisive actions to protect the organization. SecurityCenter is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audit files. Active scanning examines running processes and services, including remote access services, and detects vulnerable software applications, configuration settings, and additional vulnerabilities. Monitoring the network to ensure that all systems are secured against vulnerabilities is essential to ongoing security efforts. With more than one million users and more than 20,000 enterprise customers worldwide, organizations trust Tenable for proven security innovation. Tenable’s customers range from Fortune Global 500 companies, to the Department of Defense, to mid-sized and small businesses in all sectors, including finance, government, healthcare, higher education, retail, and energy. Transform security with Tenable, the creators of Nessus and leaders in continuous monitoring, by visiting tenable.com.
The following components are included within this dashboard:
- Verizon DBIR - Remote Access: The Verizon DBIR notes that it is important to restrict remote access to systems. This matrix assists the organization in monitoring remote access activity across the network. The Unusual VPN indicator is highlighted purple when a VPN login originates from an IP address that is not normal for the user ID. Multiple indicators highlight VPN, SSH, RDP, VNC, and SSL traffic events within the last 72 hours, including potential intrusion events, events associated with known bad IP addresses (threatlist), and long-term events. The VPN Sniffed and SSH Sniffed indicators are highlighted purple if those protocols, respectively, are passively detected on the network. The Compliance Fails indicator is highlighted red if there are any remote access compliance failures. The GoToMyPC and RemotelyAnywhere indicators are highlighted purple if those applications are detected on the network. Clicking on a highlighted indicator will bring up the analysis screen to display details on the detections and events and allow further investigation.
- Remote Access Detection - Remediation Summary: This table provides information on vulnerability remediation solutions available for remote access vulnerabilities. Filters used within this component use associated CPE strings for applications associated with each remote access protocol, which provides a greater view for analysts to quickly detect vulnerabilities associated with these applications, and adds to the level of vulnerability detail provided to the organization. Each solution provides the percentage of risk reduction, the total hosts affected, and the percentage of vulnerabilities resolved. This component can be used to obtain a list of patches that can be installed to quickly remediate vulnerabilities and reduce risk.
- Indicators - Network Anomalies and Suspicious Activity: This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs and continuous scanning activity and places them into one spot.
- Remote Access Detection - Vulnerabilities Indicator: This component displays warning indicators for 20 specific remote access applications. The useful part of this component is the depth taken to find the obscure remote access applications or separate common applications within their respective operating systems using CPE filters. Organizations can use the information provided within this component to gain a better understanding of systems that may be at risk and accessible from outside of the network. An indicator will display purple when a vulnerability has been detected in that specific remote access application.
- Remote Access Detection - Remote Access Port Tracking: This component uses NetFlow and Network Monitor analysis to identify systems with traffic that may be related to a specific protocol. LCE also provides the ability to monitor NetFlow information by either collecting NetFlow or by using the Network Monitor Agent. The Network Monitor Agent works similar to a NetFlow collector, but stores the records in a LCE-friendly method. The NetFlow and Network Monitor can detect traffic patterns and which can then be identified as interesting traffic. The filters use the “Destination Port” filter as the ports are on well-known sources, and tracking based on “Destination Port” will result in less false positives. When a pattern is discovered the indicator will turn purple.
- Remote Access Detection - Exploitable, High CVSS Score, and Compliance Vulnerabilities: This table presents an overview of vulnerability details with respect to four remote access protocols. The number of systems using remote access capable applications are included. For each protocol, the percentages of vulnerabilities that are exploitable are included. Additionally, for each protocol a CVSS score of 7.0 or above are noted. Both the Exploit and CVSS columns are filtered by CPE string, which provide a greater view of existing applications vulnerabilities on the network. Lastly, compliance checks are filtered using plugin name, which will provide additional information on the detected compliance issue. For each percentage, 0 to 24 percent will display green, 25 to 49 percent will display yellow, 50 to 74 percent will display orange, and 75 to 100 percent will display red. Security teams should attempt to keep all of these percentages as close to zero as possible.
- Remote Access Detection - 90-Day Trend of Vulnerabilities: This component presents a trend chart of detected vulnerabilities from remote access software over the last 90 days. Information presented within this uses the CPE filter to identify vulnerabilities associated within applications utilizing SSH, VNC, RDP, and VPN protocols. Data points are calculated every 3 days to provide the most accurate trend of vulnerabilities detected over time. This chart can be useful in monitoring the presence of various types of vulnerabilities in security software over time. Analysts can modify this component to include additional or specific CPE strings to filter data per organizational requirements.