by Cody Dumont
November 20, 2015
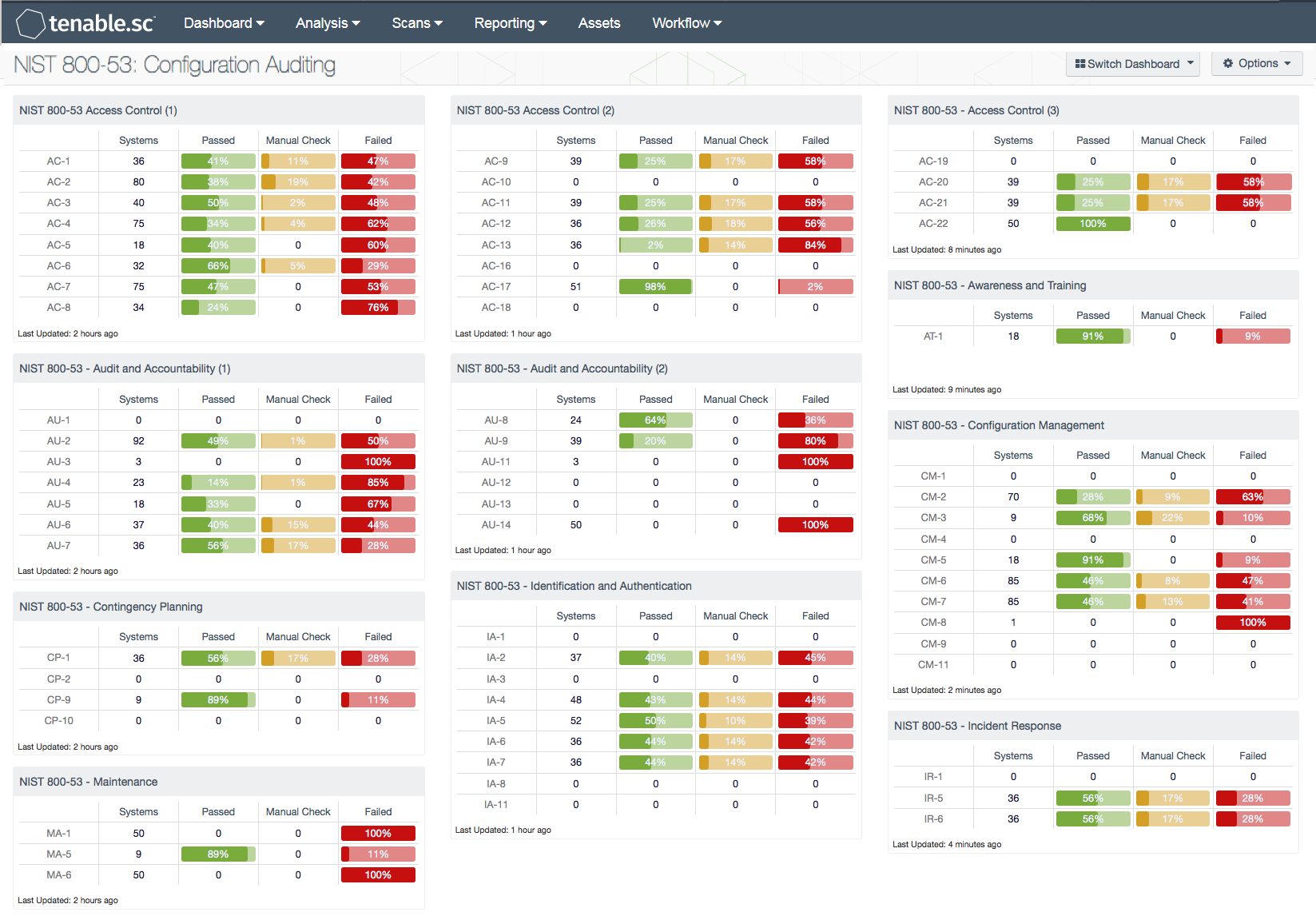
The National Institute of Standards and Technology (NIST) develops many standards that are available to all industries. A common set of standards is the NIST 800-53. This dashboard summarizes all the families outlined in the NIST Special Publication 800-53 Revision 4. The publication consists of 18 families, and each family contains security controls related to the general security topic. Each security control was designed to help organizations, both private and public, to select the controls best suited to protect mission critical services. Implementing these controls properly can aid in the defense against a diverse set of threats including hostile cyber attacks, natural disasters, structural failures, and human errors.
The NIST families and controls are not a checklist-type compliance standard like HIPAA, PCI, or CSF; rather, they are a catalog of controls that are used in achieving compliance with the aforementioned standards. Using this dashboard can assist the organization in understanding how they currently meet various standards. Each family has a component or components to provide a summary of all checks that are supported using audit files. Where multiple components are required, a number in parentheses will be displayed. Each component provides a column with system count, followed by three ratio bars for each severity level.
This dashboard covers all the NIST families currently supported by Tenable audit files, which provide the results of an audit check as one of three severity levels. The informational severity level is considered a pass. The pass is achieved when the configuration setting matches the expected result of the audit check. The match can be a defined value or a range of values. When an audit check fails, the severity is set to high, indicating that the collected result and the expected result do not match. A mismatch may not mean a failure. Each failure should be reviewed and verified to ensure the expected result is correct. If the expected result is not correct, then the audit file should be modified and the scan should be run again. Results assigned a medium severity must be evaluated by an analyst to determine whether the results are accurate or not.
The components in this dashboard use audit files (released after 1 July 2013), which incorporate the reference tag that maps many audit checks to a respective standard. In the case of this dashboard, the audit files must contain a string similar to '800-53|IA-5' on the reference line of the applicable audit check.
For example 'reference: CCE|CCE-8912-8,800-53|IA-5,PCI|8.5.12,800-53|CM-6'
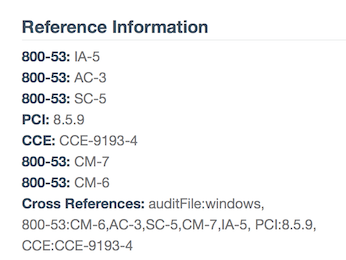
Please note that if you are creating you own filters and reports, the '800-53: IA-5' shown in the example is actually '800-53|IA-5' in the data query.
The dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, ARC, and assets. The dashboard can be easily located in the Tenable.sc Feed by selecting category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 4.8.2
- Nessus 8.5.1
- Audit Files containing NIST references
Tenable provides continuous network monitoring to identify vulnerabilities, reduce risk, and ensure compliance. Tenable.sc Continuous View (CV) measures compliance in real-time without human intervention. Allowing the organization to identify gaps and lapses are detected and prioritized immediately. With more supported technologies than any other vendor including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure, Tenable.sc CV provides the best solution for managing compliance with regulations. Tenable provides peace of mind to customers, because Tenable.sc CV detects security and compliance issues before our competitors.
Components
- NIST 800-53 - Access Control (1): This component monitors the following NIST 800-53 audit controls: AC-1, AC-2, AC-3, AC-4, AC-5, AC-6, AC-7, and AC-8.
- NIST 800-53 - Audit and Accountability (1): This component monitors the following NIST 800-53 audit controls: AU-1, AU-2, AU-3, AU-4, AU-5, AU-6, and AU-7.
- NIST 800-53 - Contingency Planning: This component monitors the following NIST 800-53 audit controls: CP-1, CP-2, CP-9, and CP-10.
- NIST 800-53 - Maintenance: This component monitors the following NIST 800-53 audit controls: MA-1, MA-5, and MA-6.
- NIST 800-53 - Personnel Security: This component monitors the following NIST 800-53 audit controls: PS-1, PS-4, PS-5, PS-6, and PS-7.
- NIST 800-53 - Program Management (1): This component monitors the following NIST 800-53 audit controls: PM-1, PM-2, PM-4, PM-5, PM-6, and PM-7.
- NIST 800-53 - System and Communications Protection Family (1): This component monitors the following NIST 800-53 audit controls: SC-1, SC-2, SC-3, SC-4, SC-5, SC-7, SC-8, and SC-9.
- NIST 800-53 - System and Information Integrity (1): This component monitors the following NIST 800-53 audit controls: SI-1, SI-2, SI-3, SI-4, SI-5, SI-6, and SI-7.
- NIST 800-53 - Access Control (2): This component monitors the following NIST 800-53 audit controls: AC-9, AC-10, AC-11, AC-12, C-13, C-16, AC-17, and AC-18.
- NIST 800-53 - Audit and Accountability (2): This component monitors the following NIST 800-53 audit controls: AU-8, AU-9, AU-11, AU-12, AU-13, and AU-14.
- NIST 800-53 - Identification and Authentication: This component monitors the following NIST 800-53 audit controls: IA-1, IA-2, IA-3, IA-4, IA-5, IA-6, IA-7, IA-8 and IA-11.
- NIST 800-53 - Physical and Environmental Protection: This component monitors the following NIST 800-53 audit controls: PE-1, PE-3, PE-5, PE-16 and PE-19.
- NIST 800-53 - Program Management (2): This component monitors the following NIST 800-53 audit controls: PM-8, PM-9, PM-10, PM-11, and PM-14.
- NIST 800-53 - Risk Assessment: This component monitors the following NIST 800-53 audit controls: RA-1, RA-2, RA-3, and RA-5.
- NIST 800-53 - System and Communications Protection Family (2): This component monitors the following NIST 800-53 audit controls: SC-10, SC-12, SC-13, SC-15, SC-16, SC-17, SC-18, and SC-20.
- NIST 800-53 - System and Information Integrity (2): This component monitors the following NIST 800-53 audit controls: SI-8, SI-9, SI-10, SI-11, and SI-12.
- NIST 800-53 - Access Control (3): This component monitors the following NIST 800-53 audit controls: AC-19, AC-20, AC-21, and AC-22.
- NIST 800-53 - Awareness and Training: This component monitors the following NIST 800-53 audit control: AT-1.
- NIST 800-53 - Configuration Management: This component monitors the following NIST 800-53 audit controls: CM-1, CM-2, CM-3, CM-4, CM-5, CM-6, CM-7, CM-8, CM-9, and CM-11.
- NIST 800-53 - Incident Response: This component monitors the following NIST 800-53 audit controls: IR-1, IR-5, and IR-6.
- NIST 800-53 - Media Protection: This component monitors the following NIST 800-53 audit controls: MP-1, MP-2, MP-3, MP-4, MP-6, MP-7, and MP-8.
- NIST 800-53 - Planning: This component monitors the following NIST 800-53 audit controls: PL-1, PL-2, PL-5, and PL-8.
- NIST 800-53 - Security Assessment and Authorization: This component monitors the following NIST 800-53 audit controls: CA-1, CA-2, CA-3, CA-5, CA-6, and CA-7.
- NIST 800-53 - System and Communications Protection Family (3): This component monitors the following NIST 800-53 audit controls: SC-22, SC-23, SC-26, SC-28, and SC-39.
- NIST 800-53 - System and Services Acquisition: This component monitors the following NIST 800-53 audit controls: SA-1, SA-4, SA-6, SA-7, SA-8, SA-10, SA-12, and SA-13.