by Sharon Everson
July 2, 2014
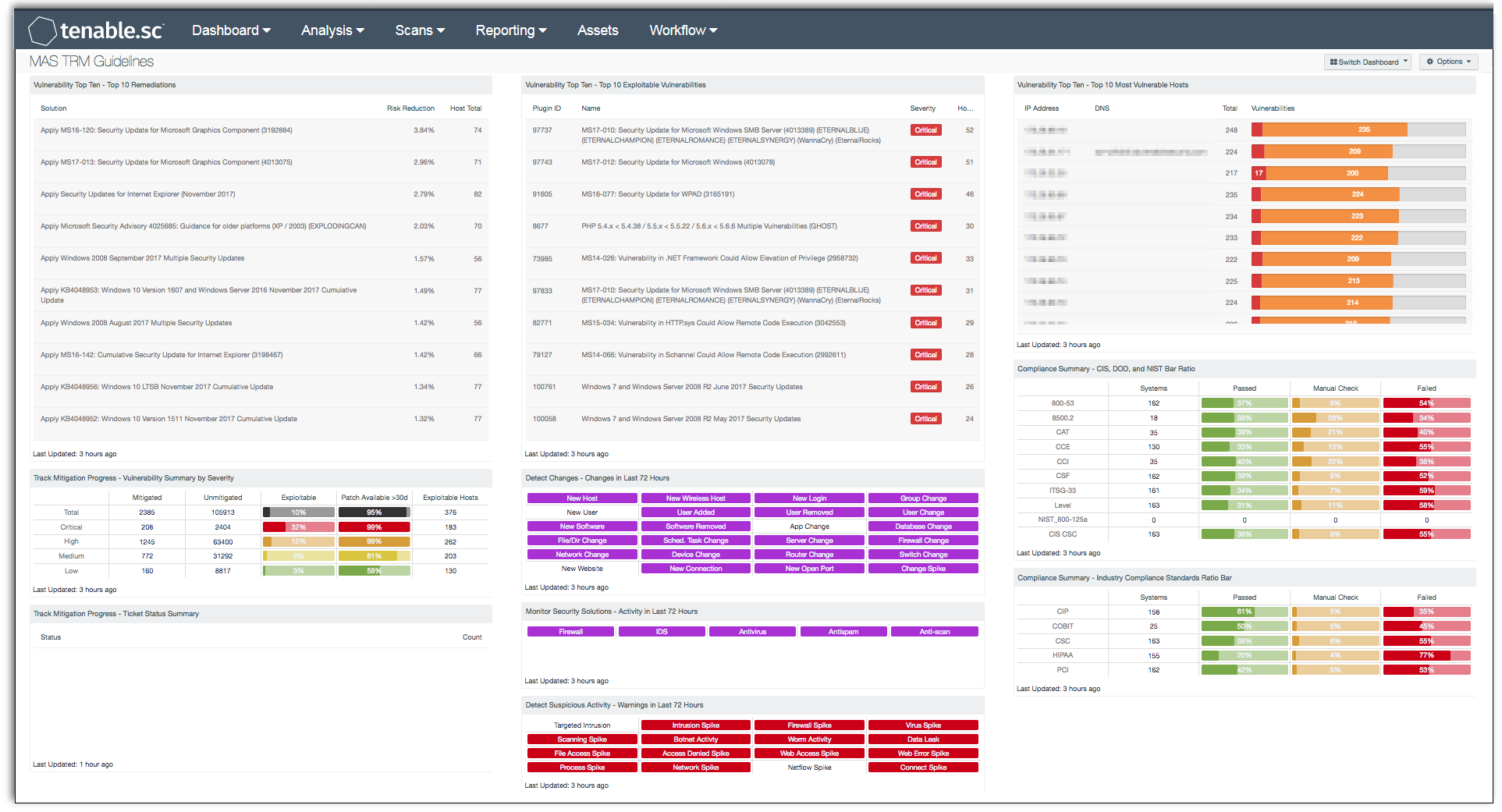
The Monetary Authority of Singapore(MAS) legislated the Technology Risk Management(TRM) guidelines for higher security in the financial industry. All financial institutions licensed, approved, or regulated by MAS must adhere to these guidelines to do business. This Dashboard provides information to assist teams in monitoring and reducing the cyber risk in their environment to comply with certain sections of the guidelines.
As financial institutions develop more online and mobile applications their attack surface and level of risk increases. The MAS TRM guidelines serve to assist financial institutions in managing their infrastructure and maximizing risk reduction. Tenable.sc CV™ provides detailed information that benefit all infrastructure teams in an organization. The components in this dashboard assist with compliance of section 4 TRM Framework by providing risk identification, assessment, monitoring and reporting. Providing the top 10 exploitable vulnerabilities, most vulnerable hosts and remediation's assists analysts and administrators, to quickly identify and mitigate critical and high issues.
Administrators and analysts can identify and monitor a wide range of changes on the network with Tenable.sc CV™ with Tenable's Log Correlation Engine(LCE) and Nessus Network Monitor(NNM). Tenable.sc CV™ provides managers with the ability to monitor the progress of mitigated and unmitigated assets and a view of all pass, fail or manual check for several standard compliance summaries. This information highlights areas of vulnerability on the network that may call for policy adjustments to better align with MAS TRM guidelines.
Note that this dashboard relies on NNM detections being forwarded to the LCE. Make sure that the NNM is configured to send syslog messages to the LCE: in Configuration > NNM Settings > Syslog, include the LCE host (with port 514) in the Real-time Syslog Server List. The LCE listens for syslog messages by default.
The dashboard and elements are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessments.
The dashboard requirements are:
- Tenable.sc 5.2.0
- Nessus 8.5.1
- NNM 5.9.0
- LCE 6.0.0
- LCE Client - Tenable NetFlow Monitor
Tenable's Tenable.sc Continuous View® (Tenable.sc CV™) provides continuous network monitoring, vulnerability identification and security monitoring. Tenable.sc CV™ is continuously updated with information about advanced threats, zero-day vulnerabilities and new types of regulatory compliance configuration audit files. Tenable constantly analyzes information from unique sensors, delivering continuous visibility and critical context, and enabling decisive action that transforms a security program from reactive to proactive. Active scanning periodically examines the applications on the systems, the running processes and services, web applications and configuration settings. Passive listening provides real-time discovery of vulnerabilities on operating systems, protocols, network services, wireless devices, web applications, and critical infrastructure. Tenable.sc CV™ provides an organization with the most comprehensive view of the network and actionable information to support mitigation efforts and reduce cyber risk. Teams can better monitor and asses their network with Tenable.sc CV™ to be in compliancy with MAS TRM Guidelines. Tenable enables powerful, yet non-disruptive, continuous monitoring that will provide organizations with the information needed to reduce risk within the enterprise.
This dashboard contains the following components:
- Vulnerability Top Ten - Top 10 Remediations - This table displays the top 10 remediations for the network. For each remediation, the risk reduction for the network if the remediation is implemented is shown, along with the number of hosts affected. The list is sorted so that the highest risk reduction is at the top of the list. Implementing the remediations will decrease the vulnerability of the network.
- Vulnerability Top Ten - Top 10 Exploitable Vulnerabilities - This table displays the top 10 exploitable vulnerabilities on the network. The list is sorted so that the most critical vulnerability is at the top of the list. For each vulnerability, the severity and the number of hosts affected is shown.
- Vulnerability Top Ten - Top 10 Most Vulnerable Hosts - This table displays the 10 hosts on the network that have the greatest number of exploitable critical and high severity vulnerabilities. The list is sorted so that the most vulnerable host is at the top of the list. For each host, a bar graph of its critical and high severity vulnerabilities are shown.
- Track Mitigation Progress - Vulnerability Summary by Severity - Tenable.sc records when vulnerabilities are discovered, when patches are issued, and when vulnerabilities are mitigated. This component assists in tracking vulnerability mitigations. The matrix presents vulnerability summary information by severity. In the matrix, the row with purple is critical severity vulnerability information, the row with red is high severity, the row with orange is medium severity, and the row with blue is low severity. The Mitigated column displays the total number of mitigated vulnerabilities. The Unmitigated column displays the total number of vulnerabilities that have not yet been mitigated. The Exploitable column displays the percentage of those unmitigated vulnerabilities that are known to be exploitable. The Patch Available column displays the percentage of the unmitigated, exploitable vulnerabilities that have had a patch available for more than 30 days. Ideally, both of these percentages should be 0%, because all exploitable vulnerabilities and all vulnerabilities with patches available should have been mitigated already. The Exploitable Hosts column displays the number of hosts on the network that have unmitigated, exploitable vulnerabilities.
- Track Mitigation Progress - Ticket Status Summary - Tenable.sc includes an integrated ticketing and alerting system; this table presents a status summary of tickets. Tickets are a means by which tasks are assigned to users to perform important actions such as vulnerability or event remediation. Tickets can be created both manually and automatically by a predefined set of conditions through the alerting functionality. Integration with any existing third-party ticketing systems is also supported, typically via e-mail integration. When the Tenable.sc ticketing system is used to track the vulnerability mitigation process, this component can assist in tracking mitigation progress.
- Detect Changes - Changes in Last 72 Hours - This component can assist in maintaining up-to-date inventories and detecting changes. The matrix presents indicators for network changes detected in the last 72 hours. Each indicator is based on one or more Log Correlation Engine (LCE) events; the indicator is highlighted yellow if the event occurred in the last 72 hours. Any changes should be investigated to determine if they are authorized. More information can be obtained on these events (such as change details, time, and IP address) by clicking on the specific indicator and viewing the raw syslog.
- Monitor Security Solutions - Activity in Last 72 Hours - This component assists in monitoring security solutions. The matrix presents activity indicators for various security solutions: Firewall, IDS, Antivirus, Antispam, and Anti-scanning. This component assumes that if log events were received in the last 72 hours from a particular technology, then that technology is active on the network, so the indicator is highlighted green. Further investigation is warranted if a protection technology should be active, but no events are being received.
- Detect Suspicious Activity - Warnings in Last 72 Hours - This matrix presents warning indicators for potentially suspicious network activity detected in the last 72 hours. Each indicator is based on one or more Log Correlation Engine (LCE) events; the indicator is highlighted red if the event occurred in the last 72 hours. Any warnings should be further investigated. More information can be obtained on these events (such as details, time, and IP address) by clicking on the specific indicator and viewing the raw syslog.
- Compliance Summary - Check Result Ratio - This component provides a ratio view of systems that have been checked for a variety of compliance standards. The ratio bar provides a visual of the number of compliance checks that have either passed, failed, or that require some manual verification.